What is the Practice Guide on Cloud Adoption?
The Hong Kong Monetary Authority (HKMA) issued the latest “Practice Guide on Cloud Adoption” (Practice Guide) on January 8th, 2026, setting out enhanced guidance to support Authorized Institutions (AIs) in adopting cloud technology securely and responsibly under the "Fintech 2030" strategy.

The latest HKMA Practice Guide illustrates supervisory principles and best practices to help AIs safely scale cloud use across hybrid/multi-cloud environments, as cloud initiatives now account for about 80% of reportable technology projects among banks in Hong Kong (including one-third to one-half involving critical systems).
The Practice Guide expands the number of cloud-related domains covered from four to eight, including governance, security, and resilience, to help AIs manage risks, strengthen operational resilience, and facilitate digital transformation. It also translates existing requirements from relevant Supervisory Policy Manual (SPM) modules into actionable, lifecycle-based guidance proportionate to workload criticality. The “dual-layered" approach binds high-level principles plus optional good practices drawn from HKMA supervision and global benchmarks, superseding the 2022 cloud circular.
Compliance Brief
Complying with the HKMA Practice Guide on Cloud Adoption in Hong Kong
Learn how Thales helps AIs comply with the Practice Guide across five domains.
How Thales Helps with HKMA Practice Guide on Cloud Adoption Compliance
Thales’ solutions can help Authorized Institutions (AIs) in Hong Kong to address the Practice Guide across five domains by simplifying compliance and automating security with visibility and control, reducing the burden on security and compliance teams.
HKMA Compliance Solutions
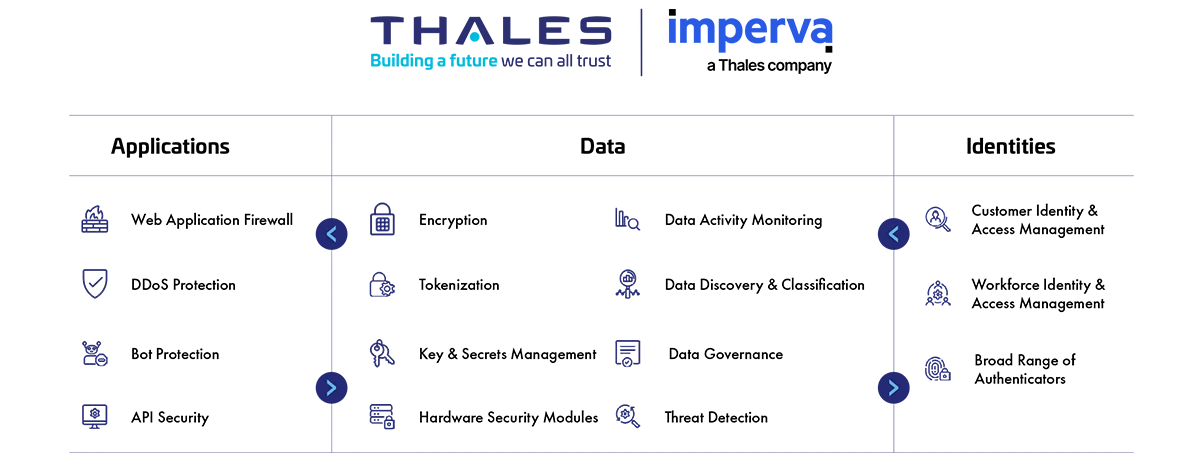
Application Security
Protect applications and APIs at scale in the cloud, on-premises, or in a hybrid model. Our market leading product suite includes Web Application Firewall (WAF), protection against Distributed Denial of Service (DDoS) and malicious BOT attacks, security for APIs, and a secure Content Delivery Network (CDN).
Data Security
Discover and classify sensitive data across hybrid IT and automatically protect it anywhere, whether at rest, in motion, or in use, using encryption tokenization and key management. Thales solutions also identify, evaluate, and prioritize potential risks for accurate risk assessment as well as identify anomalous behavior, and monitor activity to verify compliance, allowing organizations to prioritize where to spend their efforts.
Identity & Access Management
Provide seamless, secure and trusted access to applications and digital services for customers, employees and partners. Our solutions limit the access of internal and external users based on their roles and context with granular access policies and Multi-Factor Authentication that help ensure that the right user is granted access to the right resource at the right time.
Address the Principle on Cloud Adoption – The Practice Guide
How Thales helps:
- Allow AIs to protect the root-of-trust of a cryptographic system within a highly secure environment on-premises in Hong Kong to meet data sovereignty.
- Offer hardware-based crypto key operations with FIPS 140-3 Level 3 and Common Criteria validation, which enables AIs with strong, independently tested physical and logical safeguards around crypto operations with on-premises control rather than CSP’s native solutions.
- Provide on-premises solutions for data discovery, classification and protection to AIs to achieve “equivalent to internal standards”.
- Enable data sovereignty by centralizing encryption key management across hybrid and multi-cloud environments, supporting “Bring Your Own Key" (BYOK) and "Hold Your Own Key" (HYOK) models, allowing AIs to maintain control over encryption keys and data access.
- Manage encryption keys centrally, provide granular access control, and configure security policies with on-premises key management solutions to achieve cross-border data transfer practices.
How Thales helps:
- Employ a FIPS 140 validated virtual key management solution for managing encryption keys, security policies, and data protection across multi-cloud and hybrid environments, for better control and visibility than a native CSP.
- Protect cryptographic keys in a tamper-resistant FIPS 140-3 Level 3 validated environment for securing the key lifecycle, giving AIs stronger and independently attested protection for cryptographic operations.
How Thales helps:
- Centralise key management across on‑prem and multiple CSPs, so encrypted workloads can move between environments while maintaining consistent key and access policy control.
- Secure encryption keys rooted in HSMs but used across cloud regions/providers, supporting resilient, CSP‑agnostic data protection designs.
How Thales helps:
- Manage encryption keys used for primary, secondary and tertiary backups on‑prem and in cloud storage, with secure key backup/restore and clustering.
- Enable recovery of encrypted backups with centralised key custody even if a CSP region or native KMS is unavailable.
How Thales helps:
- Secure keys and encryption policies independent of any single CSP; encrypted data can be re-hosted elsewhere while access remains governed centrally.
- Orchestrate native/BYOK/HYOK keys across various cloud providers such as AWS, Azure, GCP, SAP and more, providing a consistent portable key layer across environments with Cloud Key Management.
How Thales helps:
- Enable revoke, rotate, or disable keys with Hold-Your-Own-Key (HYOK) and Bring-Your-Own-Key (BYOK) with Cloud Key Management, so data can be rendered unreadable at the old CSP and re-protected in the new environment.
- Provide audit trails of key lifecycle events (creation, rotation, deletion) to evidence secure exit, data erasure and decommissioning of access.
How Thales helps:
- Enforce separation of duty between your data and external party, as well as your cloud service provider (CSP), by securely storing encryption keys outside of the corresponding cloud.
- Automate key lifecycle management across clouds and hybrid environments with processes and tools.
- Protect cryptographic keys in a FIPS 140-3 Level 3 environment for strong and independently validated cryptographic controls.
- Enable relationship management with suppliers, partners or any third-party user, with clear delegation of access rights.
- Minimize privileges by using relationship-based fine-grained authorization.
How Thales helps:
- Secure sensitive data and maintain complete governance and control of sensitive data and the associated encryption keys and policies with Bring-Your-Own-Encryption (BYOE), Hold-Your-Own-Key (HYOK) and Bring-Your-Own-Key (BYOK) approaches, as well as a centralized multi-cloud key management.
- Offer transparent encryption and access control for data residing.
- Encrypt sensitive data once it is created and make sure cleartext data will not be processed or stored by unauthorized applications and personnel.
- Allow root users to do their job without abusing data by privileged user access controls.
- Accelerate threat detection and ease forensics with data access audit logging.
- Simplify key management across on-premises and multi-cloud deployments by centralizing control on the FIPS140-3 Level 3 environment.
Application and API security
- Provide continuous discovery and classification potential risk of all public, private, and shadow APIs.
- Monitor API activity, track usage, detect anomalies, and identify potential unauthorized access attempts.
- Offer advanced API Verification capabilities to strengthen your defenses against potential vulnerabilities.
- Safeguard your login endpoints from credential stuffing, brute force attacks, and account fraud.
- Detect and prevent cyber threats with web application firewall, ensuring seamless operations and peace of mind.
- Integrate bot protection, API security, and machine learning to safeguard against all OWASP Top 10 threats.
- Enable complete visibility and help in singling out enterprise-wide attack campaigns.
- Safeguard critical network assets from DDoS attacks and Bad Bots while continuing to allow legitimate traffic.
- Protect against both volumetric and application-layer DDoS attacks in one scalable solution at ease.
- Deploy data protection controls in hybrid and multi-cloud applications to protect DevSecOps.
- Protect and automate access to secrets across DevOps tools.
- Offer FIPS 140-2 Level 3 root of trust for credentials and keys.
Automated deployment and configuration management
- Protect application data and eliminate the need for Developers (Devs) to manage security and update data protection.
- Deploy data protection solutions into environments through orchestration.
- Perform updates and keep up with compliance requirements by Data Security Admins without taking Devs off of other projects.
- Adopt “Shift left” – Security measurement in the early stage of development.
Patch Management
- Run assessment tests on data stores such as MySQL or so to scan for known vulnerabilities.
- Scan your databases with over 1,500 predefined vulnerability tests based on CIS and PCI-DSS benchmarks to help you keep your databases covered for the latest threats.
- Detect and virtually patch database software vulnerabilities.
Solutions:
Application Security
Cloud Web Application Firewall
Data Security
Enterprise & Cloud Key Management
How Thales helps:
- Limit access to systems and data based on roles and context with policies.
- Apply contextual security measures based on risk scoring.
- Centralize access policies and enforcement to multiple hybrid environments in a single pane of glass.
- Enable continuous monitoring to capture and analyze all data store activity, providing detailed audit trails that show who accesses what data, when, and what was done to the data.
- Provide a unified strategy for access control across all user populations.
- Enable a consistent and policy-driven approach to identification, authentication, and authorization of all users to their IT assets, data, and services.
- Manage all users, including the workforce, contractors, third-party users such as customers, suppliers, logistics, and B2B or B2C type users.
How Thales helps:
- Classify and assign specific sensitivity levels for data when you are defining your data stores and your classification profiles for different types of data sets.
- Identify the current state of compliance and document gaps.
- Encrypt data at rest on-premises, across clouds, and in big data or container environments.
- Pseudonymize sensitive data at the source, ensuring that cleartext data is never exposed to unauthorized applications or personnel during processing or storage.
- Offer advanced multi-cloud Bring Your Own Encryption (BYOE) solutions to ensure data mobility to efficiently secure data across multiple cloud vendors with centralized and independent encryption key management.
- Provide data activity monitoring for structured and unstructured data across cloud and on-prem systems.
- Monitor data access activity over time to set up alerts on activity that can put AIs at risk.
- Manage encryption keys, provide granular access control and configure security policies.
- Centralize key lifecycle management, including generation, rotation, destruction, import, and export.
- Ensure secure deletion by removing keys from CipherTrust Manager, digitally shredding all instances of the data.
- Enforce access controls, including the use of passphrases or key encryption keys. Private keys stored in the HSM remain encrypted and require proper authentication to access.
- Feature detailed logging and audit trails for cryptographic operations and key management activities for reporting mandates.
- Unify all cloud Key Management Services with a single pane of glass view across regions for cloud native, BYOK and HYOK keys and one straightforward UI.
- Enforce separation of duty between your data and external party as well as your cloud service provider (CSP) by securely storing encryption keys outside of the corresponding cloud.
- Allow automatic key rotation with no application downtime, enabling AIs to easily migrate to newer cryptographic standards if and when required.
- Manage and protect all secrets and sensitive credentials.
- Protect the root-of-trust of a cryptographic system within FIPS140-3 Level 3 - a highly secure environment.
- Adopt Post-Quantum Agility to deal with the threats from quantum computing.
- Protect data in motion with high-speed encryption.
- Protect data in use by leveraging confidential computing.
- Categorize and prioritize by real risks with risk scoring rather than anomalies.
- Enable relationship management with suppliers, partners or any third-party user; with clear delegation of access rights.
- Minimize privileges by using relationship-based fine-grained authorization.
Solutions:
Application Security
Cloud Web Application Firewall
Data Security
Data Discovery & Classification
Identity & Access Management
How Thales helps:
- Support Bring Your Own Key (BYOK) and Hold Your Own Key (HYOK) use cases across multiple cloud infrastructures and SaaS applications in a single interface.
- Combine support for cloud provider BYOK APIs, cloud key management automation, and key usage logging and reporting, to provide cloud consumers with a cloud key management service that delivers strong controls over encryption key life cycles for data encrypted by cloud services.
- Provide a strong separation of duty for the encryption keys; AIs can maintain control of their keys instead of entrusting them to the CSP.
How Thales helps:
- Record access to the database system and detect login attempts on the database system.
- Produce audit trail and reports of all access events to all systems, stream logs to external SIEM systems.
- Manage authentication and access control by supporting Multi-Factor Authentication and Single Sign-On (SSO) and displaying access log reports.
- Detect and alert administrators if abnormal access attempts are found, and administrators can respond quickly.
- Detect and pinpoint critical threats to data, prioritizes what matters most, and provides actionable insights.
- Support the creation of audit trail reports of all accesses for auditing and investigation in the event of any incidents.
- Detect system threats with Web Application Firewall, API Security and Database Security and stream logs to SIEM system.
- Monitor API activity, track usage, detect anomalies, and identify potential unauthorized access attempts.
- Safeguard critical network assets from DDoS attacks and Bad Bots while continuing to allow legitimate traffic.
- Apply contextual security measures based on risk scoring.
- Manage and monitor access controls to enterprise-wide systems effectively.
- Flag access anomalies for investigation by the security team, and integrate seamlessly with SIEM solutions for a more comprehensive approach to threat and anomaly detection.
- Log all user access and authentication activities.
Solutions:
Application Security
Data Security
Identity & Access Management
How Thales helps:
- Correlate and distill thousands of security events into a few distinct readable narratives and allow quick and decisive response to threats.
- Enable complete visibility and help in singling out enterprise-wide attack campaigns.
- Detect system threats with Web Application Firewall, API Security and Database Security and stream logs to SIEM system.
- Monitor API activity, track usage, detect anomalies, and identify potential unauthorized access attempts.