Schrems II
Thales enables organizations to maintain GDPR compliance in light of Schrems II ruling
The General Data Protection Regulation (GDPR) laid down the requirements on securing personal data within the European Union (EU) or European Economic Area (EEA). However, it did not adequately address securing personal data of EU citizens when it is processed outside the EU by other countries, such as the transatlantic data flows that account for more than half of Europe’s transactions.
The recent Court of Justice of the European Union (CJEU) decision in the Schrems II ruling invalidated the EU-US Privacy Shield framework, since it did not adequately enforce EU’s GDPR regulations to protect personal data as it moved between EU and the US. With the nullification of Privacy Shield, and before that, Safe Harbor, companies are no longer protected from liability over those data transfers and they are looking for data protection solutions that can adequately protect global commerce.
The European Data Protection Board (EDPB) is an independent European body, which contributes to the consistent application of data protection rules throughout EU, and promotes cooperation between data protection authorities in each EU country. To address Schrems II ruling, EDPB recently adopted recommendations on supplementary measures along with a second document on EU essential guarantees, which gives guidance to non-EU countries on ensuring compliance with the EU-level of data protection of personal data. The new recommendations from EDPB allow organizations to build a trusted privacy framework to enhance transatlantic data flows
Thales enables organizations to maintain GDPR compliance and adhere to the Schrems II ruling, using a trusted privacy framework for protecting transatlantic data flows that follow these overarching principles.
The Schrems II ruling underscores the need to ensure personal and sensitive data is protected under GDPR, when it is transferred to/from EU and other non-EU countries. As a result of the ruling European Data Protection Board (EDPB) recommends a six-step plan for continually assessing and protecting global data flows in-line with EU data privacy regulations.
Step 1: Know your data transfers
The first step is to ensure that you have a record of all data transfers with other countries outside the EU logging the series of processors and sub-processors. You must verify that the data you transfer is adequate, relevant and limited to what is necessary to be processed in the third country.
Step 2: Identify the transfer tools you are relying on
The second step is to identify the data transfer tools you are relying on among those listed in Chapter V of GDPR, and take decisions relating to some or all of the third countries to which you are transferring data, that they offer adequate level of protection of personal data.
Step 3: Assess whether the transfer tool is sufficient to meet GDPR (article 46) requirements
The transfer tool must ensure that the level of protection guaranteed by GDPR within the EU countries is as good in the third country outside the EU. Your assessment should take into consideration all the actors participating in the data transfer (e.g. controllers, processors and sub-processors) processing the data in third-countries.
Step 4: Adopt supplementary measures
If the assessment in step 3 has revealed that the transfer tool is not effective, then you will need to consider supplementary measures which, when added to the safeguards could ensure the same level of safeguards guaranteed within the EU are enforced for external data transfers.
Step 5: Procedural steps if you have identified supplementary measures
You may have to take these supplementary measures, if the primary measures used by the data transfer tools are not sufficient to protect the data.
Step 6: Re-evaluate at appropriate intervals
You must monitor on an ongoing basis, and where appropriate in collaboration with data importers in the third countries to which you have transferred data, put in sufficient mechanisms to promptly suspend data transfers, if the data importer breached the contract.
Thales enables organizations to maintain compliance with GDPR and adhere to the European Data Protection Board (EDPB) recommendations for adopting Schrems II ruling using the six-step plan for continually assessing and protecting global data flows.
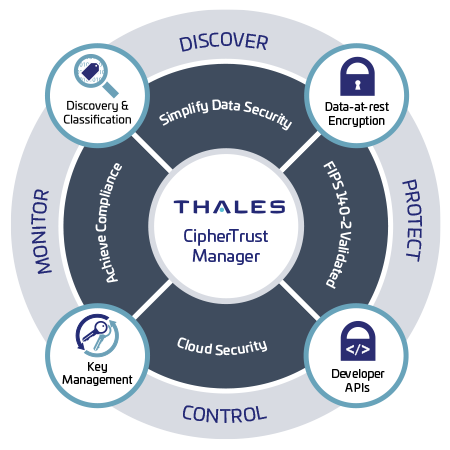
The CipherTrust Data Security Platform unifies data discovery, classification, data protection, and unprecedented granular access controls with centralized key management under your control – all on a single platform. It enables organizations to deploy bring your own encryption (BYOE) and tokenization policies to protect sensitive data at rest in both EU (data exporter) and non-EU countries (data processors).

This white paper describes how companies can adhere to the European Data Protection Board’s recommendations to address the Schrems II ruling, using the digital privacy framework provided by Thales’ data protection and trusted access management solutions.

The GDPR, which went into effect in May 2018, aims to protect the privacy of EU citizens. Any such data that you hold across your cloud environment(s) is ultimately your responsibility and under your ownership, leaving you subject to potential scrutiny under the new mandates. ...
GDPR mandates the procedures and dictates the consequences regarding data breaches and notification.

In July of 2020 the Court of Justice of the European Union issued the Schrems II decision in the case Data Protection Commission v. Facebook Ireland. That decision invalidated the EU-U.S. Privacy Shield Framework, on which more than 5,000 U.S. companies rely to conduct...

The Schrems II decision will have a great impact on international commerce among companies doing business with the European Union (EU). The consequence of not paying attention to Schrems II could literally mean a partial or complete shut-down of data transfers between EU and...

Perhaps the most comprehensive data privacy standard to date, GDPR affects any organization that processes the personal data of EU citizens - regardless of where the organization is headquartered.

Any organization that plays a role in processing credit and debit card payments must comply with the strict PCI DSS compliance requirements for the processing, storage and transmission of account data.

Data breach notification requirements following loss of personal information have been enacted by nations around the globe. They vary by jurisdiction but almost universally include a “safe harbor” clause.