The Cyber Security Agency of Singapore (CSA) has published the Codes of Practice or Standards of Performance issued by the Commissioner of Cybersecurity for the regulation of owners of Critical Information Infrastructure (CII), in accordance with the Cybersecurity Act. The Cybersecurity Code of Practice for Critical Information Infrastructure – Second Edition (CCoP2.0) comes into effect from Jul. 4, 2022, superseding previous versions of the Code.

Overview of The Cybersecurity Code of Practice For Critical Information Infrastructure (CCoP) Purpose of CCoP2.0
The CCoP2.0 is intended to specify the minimum requirements that the critical information infrastructure owner (CIIO) shall implement to ensure the cybersecurity of the CII. The CIIO is expected to implement measures beyond those stipulated in this Code to further strengthen the cybersecurity of the CII based on the cybersecurity risk profile of the CII.
- Bolster the cybersecurity defenses of CII against advanced and sophisticated cyber-attacks.
- Provide a framework for CII to tackle new challenges presented by technologies like cloud computing, Artificial Intelligence (AI), and 5G.
- Increase the ability of CII to respond to rapidly evolving cybersecurity risks and incidents.
- Promote better collaboration and information sharing between the government and the private sector to quickly identify and respond to cyber threats.
- Improve the overall resilience of Singapore's CII against disruptive cyber events.
The Cybersecurity Act provides a framework for the designation of Critical Information Infrastructure (CII), and CII Owners across the 11 critical sectors are required to comply with the mandatory cyber hygiene practices within the CCoP2.0 to ensure a strong cybersecurity foundation for the CII sectors.
- 11 critical sectors: energy, info-communications, water, healthcare, banking and finance, security and emergency services, aviation, land transport, maritime, government, and media.
- A set of mandatory Operational Technology (OT)-specific cybersecurity practices was introduced as an addendum to the CCoP2.0 with the aim of elevating the state of cybersecurity for OT CII.
Compliance Brief
Complying with The Cybersecurity Code of Practice For Critical Information Infrastructure (CCoP2.0) in Singapore
Discover how CII complies with the CCoP2.0 through our comprehensive cybersecurity solutions and learn more about the requirements.
How Thales Helps with the CCoP2.0 in Singapore
Thales’ solutions can help CII address the CCoP2.0 requirements, focusing on Protection and Detection Clauses, by simplifying compliance and automating security with visibility and control, thereby reducing the burden on security and compliance teams.
CCoP2.0 in Singapore Compliance Solutions
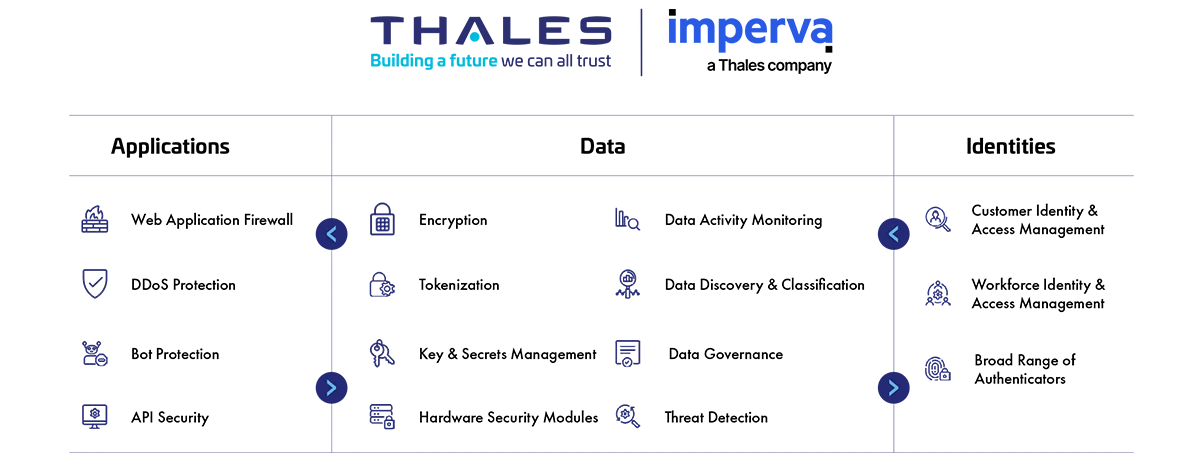
Application Security
Protect applications and APIs at scale in the cloud, on-premises, or in a hybrid model. Our market leading product suite includes Web Application Firewall (WAF), protection against Distributed Denial of Service (DDoS) and malicious BOT attacks, security for APIs, and a secure Content Delivery Network (CDN)
Data Security
Discover and classify sensitive data across hybrid IT and automatically protect it anywhere, whether at rest, in motion, or in use, using encryption tokenization and key management. Thales solutions also identify, evaluate, and prioritize potential risks for accurate risk assessment as well as identify anomalous behavior, and monitor activity to verify compliance, allowing organizations to prioritize where to spend their efforts.
Identity & Access Management
Provide seamless, secure and trusted access to applications and digital services for customers, employees and partners. Our solutions limit the access of internal and external users based on their roles and context with granular access policies and Multi-Factor Authentication that help ensure that the right user is granted access to the right resource at the right time.
Address the CCoP2.0 Clause
How Thales helps:
- Limit the access of internal and external users to systems and data based on roles and context with policies.
- Apply contextual security measures based on risk scoring.
- Centralize access policies and enforcement to multiple hybrid environments in a single pane of glass.
- Unify key management operations with role-based access control.
- Protect and automate access to secrets across DevOps tools.
- Offer Multi-Factor Authentication (MFA) to ensure that those accessing the system are truly authorized.
- Employ Single Sign-On (SSO) to allow users to securely access multiple systems with a single authentication.
- Set up access policies based on user roles, responsibilities, and risks.
Solutions:
Data Security
Identity & Access Management
How Thales helps:
- Gain full sensitive data activity visibility, track who has access, audit what they are doing and document.
- Provide flexible authentication options for automated workflows to mitigate the reliance on passwords.
- Extend single-sign-on authentication to cloud applications, enabling centralized, secure access with a protected identity.
- Apply privileged access control to sensitive data.
- Enable comprehensive secrets management of credentials, certificates and keys, including static secrets, dynamic secrets, SSH keys, API keys and tokens that support just-in-time access (dynamic secrets) instead of static ones for privileged accounts across the technology stacks.
Solutions:
Identity & Access Management
Data Security
How Thales helps:
- Discover and classify potential risk for all public, private and shadow APIs.
- Safeguard critical network assets from DDoS attacks and Bad Bots while continuing to allow legitimate traffic.
- Monitor data traffic to spot data leakage risk.
- Protect against business logic attacks and many more of the OWASP API Top Ten threats.
- Detect and prevent cyber threats with web application firewall.
- Encrypt sensitive data once it is created and make sure cleartext data will not be processed or stored by unauthorized applications and personnel.
- Protect and automate access to secrets across DevOps tools.
Solutions:
Application Security
Data Security
How Thales helps:
- Enable privileged user access control for sensitive data and restrict access from unauthorized access with the least privileged design.
- Offer high-speed bulk tokenization/ encryption, such as PII on the column level from source to destination.
- Unify key and certificate management for the connectors and third-party devices, including a variety of KMIP Clients, TDE Agents and more.
- Gain full sensitive data activity visibility, track who has access, audit what they are doing and document.
- Alert or block database attacks and abnormal access requests in real time.
- Continuously monitor processes for abnormal I/O activity and alerts or blocks malicious activity.
- Monitor active processes to detect ransomware – identifying activities such as excessive data access, exfiltration, unauthorized encryption, or malicious impersonation of a user, and alerts/blocks when such an activity is detected.
How Thales helps:
- Run assessment tests on data stores such as MySQL or so to scan for known vulnerabilities.
- Scan your databases with over 1,500 predefined vulnerability tests based on CIS benchmarks to help you keep your databases covered for the latest threats.
How Thales helps:
- Protect cryptographic keys in a FIPS 140-3 Level 3 environment.
- Streamline key management in cloud and on-premises environments with key lifecycle management.
- Support a growing list of IaaS, PaaS and SaaS providers for Cloud Key Management. SaaS solutions include Microsoft Office365, Salesforce.com and Salesforce Sandbox as well as the SAP Data Custodian. Supported IaaS/PaaS solutions include Microsoft Azure, Microsoft Azure China National Cloud, Microsoft Azure Stack, IBM Cloud, Google Cloud Platform, and Amazon Web Services.
- Manage and protect all secrets and sensitive credentials.
- Store encrypted data and its encryption key in different places for the separation of duties principle.
- Adopt Post-Quantum Agility to deal with the threats from quantum computing.
- Support for BYOK and HYOK with full key lifecycle management of native cloud keys as well as keys generated by its key sources.
How Thales helps:
- Use signature, behavioral and reputational analysis to block all malware injection attacks.
- Detect and prevent cyber threats with web application firewall.
- Gain visibility by monitoring and auditing all database activity across cloud and on-prem systems.
- Protect data with real-time alerting or user access blocking of policy violations.
- Provide insights based upon the synthesis of user behaviors, application & API access patterns, and data source context.
- Monitor unstructured data access in real time across servers, cloud, and file shares.
- Detect threats and insider risks with deep visibility and AI-driven insights with intelligent and context-rich analysis.
Solutions:
Application Security
Data Security