How SafeNet Trusted Access Powers Zero Trust Security
As organizations shift to hybrid work and multi-cloud environments, the traditional network perimeter no longer exists. SafeNet Trusted Access (STA) delivers identity-centric security that continuously verifies trust and enforces least-privilege access across your digital ecosystem.
With SafeNet Trusted Access, you can:
- Implement identity-based access controls aligned with Zero Trust principles.
- Continuously verify users and devices before granting access.
- Enforce adaptive authentication to respond to risk in real time.
- Integrate seamlessly with your existing Zero Trust architecture and cloud services.
- Simplify policy management through centralized, context-aware access control.
Whereas other ‘adaptive’ or risk-based authentication or single-sign-on (SSO) offerings focus on the login and pre-authentication process, STA is intended to provide visibility into users’ post-authentication activity, a glaring blind spot in many Identity-as-a-Service (IDaaS) offerings."
The need for Zero Trust security
When all transactions in the enterprises are untrusted, and there is no defined security boundary, encrypting data and protecting apps at the access point by continuously validating identities is core to enterprise security.
Work securely and conveniently from home
Offer employees, contractors and consultants an easy and convenient login experience no matter where they are or what device they're using.
Expand Securely in the Cloud
Overcomes the limitations of legacy security schemes by securing cloud apps at the access point from the cloud.
Prevent Breaches and Protect your Data
Protect apps by encrypting data and continuously validating identities.
Key principles of Zero Trust security models
- Trust no one – verify everywhere
- Adopt a ‘default deny’ stance’
- Secure applications at the access point
Zero Trust Security Architectures
NIST describes three approaches to building an effective Zero Trust security architecture.
Identity-centric
The identity-centric approach of Zero Trust architecture places identity of users, services, and devices at the heart of policy creation. Enterprise resource access policies are based on identity and assigned attributes. The primary requirement to access corporate resources is based on the access privileges granted to a given user, service or device. To cater for a more adaptive authentication, the policy enforcement may consider other factors as well, such as device used, asset status, and environmental factors.
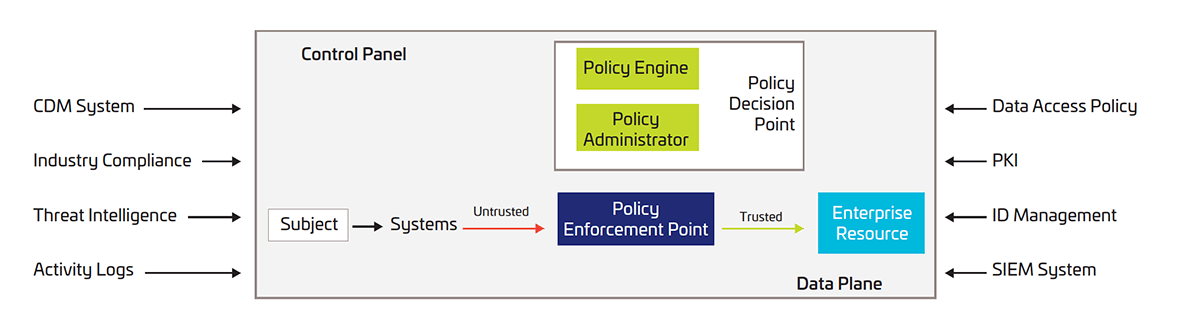
Network-centric
The network-centric approach of Zero Trust architecture is based on network micro-segmentation of corporate resources protected by a gateway security component. To implement this approach, the enterprise should use infrastructure devices such as intelligent switches (or routers), Next Generation Firewalls (NGFW) or Software Defined Networks (SDN) to act as policy enforcement protecting each resource or group of related resources.
Combination approaches
A cloud-based combined Zero Trust architecture approach leverages cloud-based Access Management and Software at the Service Edge (SASE). The cloud-based Access Management solution protects and enforces the identities of cloud applications and services, while SASE components, such as Software Defined Networks (SDNs) or Next Generation Firewalls (NGFW) protect on-premise resources.
Protect more users and apps with SafeNet Trusted Access
SafeNet Trusted Access is an access management and authentication service that enables quick deployment of multiple authentication journeys to expand your MFA coverage, allowing you to reduce insider and outsider threats.
Control access across your apps with policy-based authentication, simplify identity management, eliminate password hassles, and gain a single-pane view of access events – driving seamless security at scale.

Strong, Intelligent Authentication
Deliver adaptive, secure access experiences that scale with your organization.
- Modern and Passwordless Authentication Options
Support for FIDO, Windows Hello, and other methods enables broad user adoption and reduces help desk overhead. - Context-Aware Single Sign-On
Smart SSO with conditional access allows users to re-authenticate only when access context presents a risk. - Advanced Policy Control and Risk-Based Access
Enforce intelligent authentication decisions with granular policies, risk scoring, and endpoint posture checks.
Broad Integration and Seamless Delivery
Easily secure any app, any user, anywhere—with minimal disruption.
- Broad integration methods
Protect a broad range of applications with technologies including SAML, OIDC, WS-Fed, cloud-based RADIUS, agents, APIs, and gateways. - Flexible and resilient delivery architecture
Ensure uninterrupted access with the Access Continuum, our reliable fallback mechanism.


Fast Adoption and Operational Insight
Accelerate deployment, reduce IT overhead, and maintain full visibility.
- Fast time-to-value
Users can self-enroll with step-by-step guidance, reducing the burden on IT and increasing MFA adoption. - Data-driven insights
Full audit trails, automated log exports, and SIEM integrations enable continuous monitoring and compliance.