CipherTrust Security Intelligence – Product Brief
CipherTrust Security Intelligence efficiently tracks and investigates suspicious activities. Learn more.
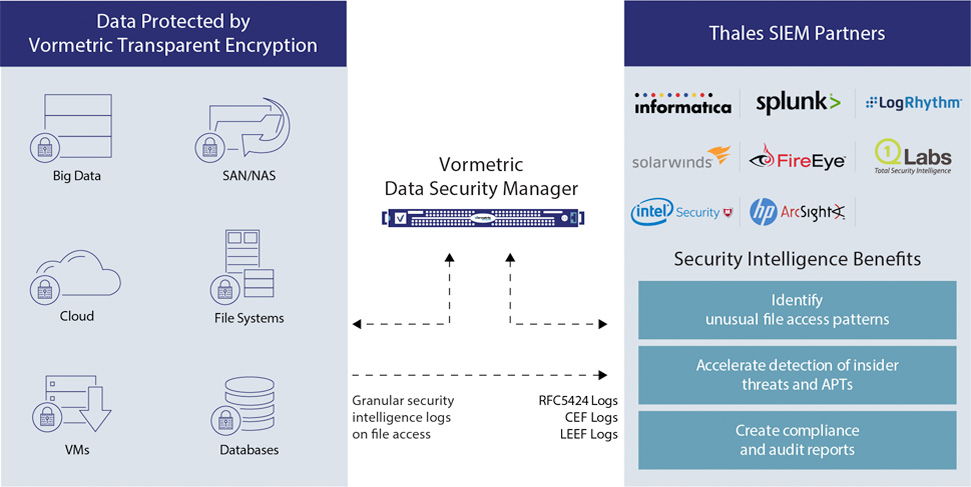
Detailed data access audit logs delivered by Vormetric Transparent Encryption are useful not only for compliance, but also for the identification of unauthorized access attempts, as well as to build baselines of authorized user access patterns. Vormetric Security Intelligence completes the picture with pre-built integration to leading Security Information and Event Management (SIEM) systems that make this information actionable. The solution allows immediate automated escalation and response to unauthorized access attempts, and all the data need to build behavioral patterns required for identification of suspicious usage by authorized users.

CipherTrust Security Intelligence efficiently tracks and investigates suspicious activities. Learn more.
Leverage immediate alerts that fuel the fastest, most efficient response when issues arise.
Produces an auditable trail of permitted and denied access attempts from users and processes.
Uncover anomalous process and user access patterns that could point to an APT attack or malicious insider activities.
Collected at the system level, Vormetric Transparent Encryption logs report authorized and unauthorized access attempts to encrypted files and volumes- including user, time, process and more. Vormetric Security Intelligence includes pre-built integration to leading SIEM systems that makes these logs actionable. Available dashboards immediately highlight unauthorized access attempts. Authorized user access data is available to create baselines for user's data usage, and can also be integrated with other security data such as user location and access points for pinpoint threat identification.
Vormetric Security Intelligence logs produce an auditable trail of permitted and denied access attempts from users and processes. The solution’s detailed logs can be reviewed to specify when users and processes accessed data, under which policies, and if access requests were allowed or denied.
In order to adhere to many compliance mandates and regulations, organizations must prove that data security is in place meets required standards. Vormetric Security Intelligence integration to SIEM systems and pre-built dashboards can be used to easily demonstrate to an auditor that encryption, key management, and access policies are effective and appropriate. With its detailed visibility and integration capabilities, Vormetric Security Intelligence helps streamline the effort associated with audits and ongoing compliance reporting.
RFC5425, CEF, LEEF

To avoid merely recognizing data security events, such as breaches, after they occur, IT managers require a simple way to identify and correlate all relevant data about potential security events, so they can mitigate threats quickly and in real time. Some of the most effective...