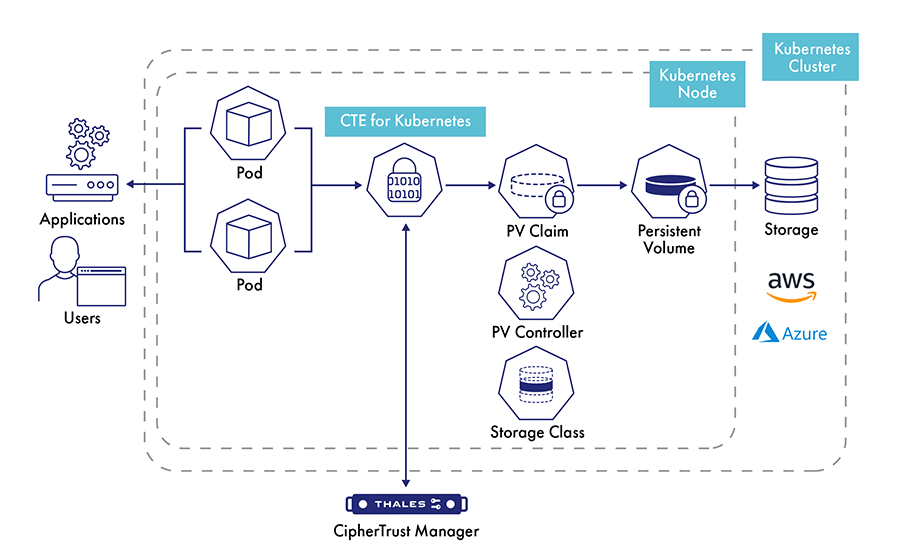
O CipherTrust Transparent Encryption for Kubernetes permite a proteção de dados confidenciais em volumes persistentes por meio de criptografia, controles de acesso baseados em processos e usuários e registro de acesso a dados. Esta solução permite que os desenvolvedores estabeleçam controles de segurança dentro de containers. Com esta extensão para o CipherTrust Transparent Encryption, a proteção de dados pode ser aplicada por container, tanto aos dados dentro dos containers quanto ao armazenamento externo acessível a partir de containers.
- Vantagens
- Características
Conformidade
O CipherTrust Transparent Encryption para Kubernetes atende aos requisitos de conformidade e aos requisitos regulatórios para proteger dados confidenciais, como cartões de pagamento, registros de atendimento médico e outros dados confidenciais.
Proteção contra ameaças de usuários privilegiados
A solução oferece criptografia com controle de acesso a dados. Isso permite que usuários privilegiados, como administradores de cluster da Kubernetes, operem como usuários regulares sem obter acesso não autorizado a dados confidenciais.
Obtenha segurança forte
O CipherTrust Transparent Encryption para Kubernetes aplica políticas de segurança de dados onde quer que os dados sejam armazenados ou usados, incluindo data centers, ambientes virtualizados e até mesmo em implementações de nuvem. Sua empresa pode implantar e usar com segurança aplicativos Kubernetes quando necessário para custo-benefício, controle ou desempenho sem precisar fazer alterações em aplicativos, containers ou infraestrutura.
Proteção abrangente para segurança de dados
O CipherTrust Transparent Encryption para Kubernetes amplia a CipherTrust Transparent Encryption para que as equipes de segurança estabeleçam controles de segurança de dados dentro dos containers. As empresas podem aplicar criptografia, controle de acesso e registro de acesso a dados por container. A criptografia é aplicada a volumes persistentes conectados a aplicativos em containers com a capacidade de restringir o acesso a dados a um grupo selecionado de usuários e processos.
Criptografia transparente
O Transparent Encryption permite aos usuários estabelecer controles de segurança de dados sem ter que fazer nenhuma alteração em aplicativos, containers ou infraestruturas. A solução oferece suporte a modelos comuns de implantação de microsserviços de container. Isso permite implantar as mesmas políticas de proteção para todos os volumes persistentes conectados a um pod de aplicativo ou ter criptografia e controle de acesso exclusivos para cada volume persistente em um cluster do Kubernetes.
Controles de acesso e visibilidade granulares
A solução CipherTrust Transparent Encryption para Kubernetes oferece a visibilidade detalhada e o controle necessário para cumprir com as mais rigorosas leis, políticas e mandatos de segurança de dados. As empresas podem estabelecer políticas de acesso granulares baseadas em usuários, processos e conjuntos de recursos específicos dentro de containers. Além disso, esta solução pode estabelecer isolamento entre contêineres, para que apenas contêineres autorizados possam acessar informações confidenciais.

CipherTrust Transparent Encryption for Kubernetes
Modern applications are increasingly built using containers, which are microservices packaged with their configurations and dependencies. Kubernetes is an open-source software for deploying and managing these containers. Containerized applications can be delivered, deployed and managed faster with Kubernetes to provide improved efficiency through re-usable modular components, cost savings through optimized resource utilization and reduced licensing expenses.