 Randy Hildebrandt | Product Marketing, Data Protection
More About This Author >
Randy Hildebrandt | Product Marketing, Data Protection
More About This Author >
 Randy Hildebrandt | Product Marketing, Data Protection
More About This Author >
Randy Hildebrandt | Product Marketing, Data Protection
More About This Author >
The Nightmare of the Elevated Attacker
In traditional Linux security, we have long operated under a grim binary: you are either protected, or the attacker has root. We’ve been taught that once an adversary achieves that # prompt, the game is over. They own the memory, the binaries, and every byte of data on the disk.
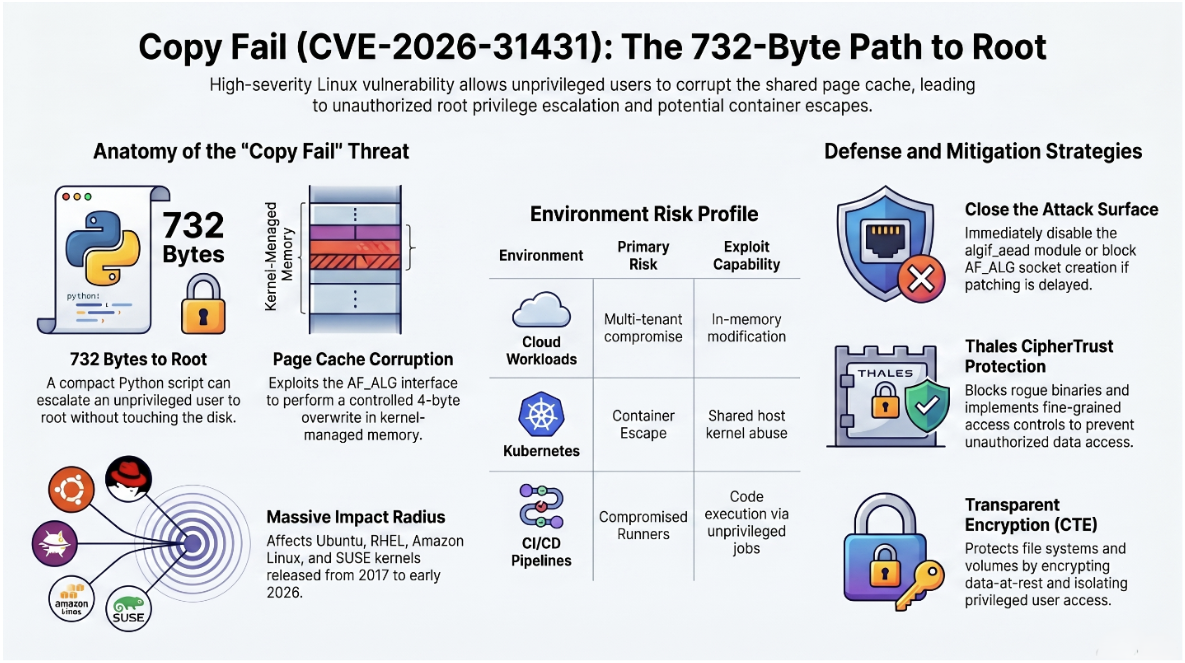
But the most dangerous threats today don’t announce themselves with the "noise" of a system crash or a memory corruption segment fault. Enter the CopyFail vulnerability (CVE-2026-31431). Unlike traditional exploits that break the system to gain entry, CopyFail is a silent logic flaw. It doesn't bypass the system's rules; it uses the system’s own logic to "convince" the kernel to hand over the keys. It is clean, it is insidious, and it shatters the illusion of the OS trust boundary.
Why It Is Important to Address This Threat
This threat is critical because time is fundamentally on the attacker's side. Today, the average time it takes an attacker to move laterally from an initial compromised endpoint is just 34 minutes, with data exfiltration happening in as little as six minutes. Conversely, traditional security detection pipelines take 10 to 30 minutes just to generate an alert, and organizations take an average of two weeks to contain an incident. By the time a security analyst reviews an alert, the attacker has already moved, escalated privileges, and achieved their objective.
How Such Vulnerabilities Are Typically Addressed
Most organizations attempt to combat this by relying heavily on detection-first architecture such as EDR, NDR, SIEM, and XDR tools which analyze logs and flag behavioral anomalies. However, this approach consistently fails against modern threats because attackers rely on "living-off-the-land" techniques, using legitimate system tools (such as SSH, RDP, or PowerShell) that blend in with routine administrative traffic. Detection systems struggle to distinguish between a legitimate sysadmin and an attacker holding stolen credentials, leading to alert fatigue and structural delays.
As a security strategist, CopyFail forces us to ask a revolutionary question: What if "Root" wasn't the final authority on data access? What if we could decouple data authority from system authority?
Takeaway 1: The Identity-Over-Privilege Paradigm
The fundamental weakness in legacy security is the assumption that privilege equals permission. In modern Zero Trust architecture, we must pivot to a model where security is rooted in identity, not privilege level.
CipherTrust Transparent Encryption (CTE) mandates this model by enforcing what we call "Identity Persistence." It effectively "remembers" the pre-escalation identity of a user. If a standard user utilizes a logic flaw like CopyFail or a standard sudo command to become root, CTE does not see a new, all-powerful entity; it sees the original user now wearing a root mask.
CTE enforces access control based on the original user identity, even after privilege escalation (e.g., via sudo or su).
This is a strategic game-changer. By maintaining the "true" user identity across execution contexts, CTE ensures that a compromised root account never inherits data permissions if it wasn't explicitly granted.
Takeaway 2: Understanding the "CopyFail" Logic Flaw
To defend against CopyFail, you must understand why it is so difficult to detect. Because it is a logic flaw rather than a memory corruption issue (like a buffer overflow), it is essentially "invisible" to standard exploit mitigations like ASLR or DEP. It doesn't break the rules of physics within the kernel; it exploits flawed reasoning in the system's design.
Key characteristics of CVE-2026-31431:
Local exploit: Requires an attacker to already have an initial foothold on the system.
Privilege escalation: Allows a low-privilege actor to seize root or other high-level identities.
Logic flaw: Exploits flawed system logic, making it functional across various kernel versions.
Wide Impact: Demonstrated to affect nearly every major Linux distribution.
Takeaway 3: GuardPoints, The Digital Vaults That Don't Care Who You Are
In a standard Linux environment, the root user is a god, there is no mechanism to stop them from reading /etc/ or your primary customer database. CTE upends this by implementing GuardPoints. These are protected directories where encryption and access policies are enforced at the filesystem level, independent of OS-level permissions.
Imagine an attacker uses CopyFail to gain root. They immediately navigate to your sensitive financial records.
- The Expected Result (Traditional): Root access is detected; the OS grants full read/write permissions.
- The Actual Result (With CTE): Access Denied.
This result feels like a violation of traditional Linux physics. Even though the attacker "is" root, CTE’s policy engine sees that the pre-escalation identity lacks the specific key to the GuardPoint. The vault stays locked because the system has successfully decoupled data authority from the compromised system authority.
Takeaway 4: Why "Process-Awareness" is the Secret Weapon
If an attacker gains root, their first move is often lateral movement or data exfiltration using standard system tools like cat, grep, or scp. This is where Process-Aware Access Control serves as the ultimate trap.
CTE allows administrators to tie data access not just to a user, but to a specific authorized binary. In a hardened environment, you can set a policy that stipulates only the production database binary (e.g., /usr/) is allowed to decrypt and read the data files within a GuardPoint.
When the "root" attacker tries to use cat to dump the database, CTE blocks the attempt. The cat process is not the authorized mysqld process. By restricting access to the application context, you render the attacker’s elevated toolkit useless against your sensitive data.
Takeaway 5: Shifting from System-Level to Data-Level Security
The era of relying on the "OS trust boundary" is over. Vulnerabilities like CopyFail prove that the kernel is a massive attack surface that will inevitably be breached. Strategy leads must stop asking "Who has root?" and start asking, "Who and what process is allowed to access this specific data?"
This shift represents the dissolution of the perimeter. When security is data-centric, the state of the OS becomes secondary to the state of the data's encryption and policy enforcement.
System-level security is not sufficient. Data-level enforcement is essential.
Best Practices for the Modern Admin
Building a resilient Linux architecture requires moving beyond the "Root is God" mindset. Use this checklist to harden your environment against privilege escalation:
- Deploy CTE GuardPoints: Isolate all sensitive workloads in protected, encrypted directories.
- Enforce Identity-Based Policies: Ensure access is tied to the authenticated, pre-escalation user.
- Implement Process-Aware Rules: Restrict data access to specific, whitelisted application binaries.
- Eliminate Over-Permissive Assumptions: Audit your policies to ensure "root" is not a default allowed user for sensitive data.
- Monitor Unauthorized "Root" Attempts: Log every time a root user is denied access to a GuardPoint; this is a high-fidelity indicator of a CopyFail-style compromise.
Conclusion: Beyond the OS Trust Boundary
The emergence of CopyFail (CVE-2026-31431) is a stark reminder that in complex systems, privilege escalation is an inevitability. We cannot patch every logic flaw before it is discovered, but we can render those flaws irrelevant to our data security.
By adopting CipherTrust Transparent Encryption, organizations move into a post-OS trust model. Even when the kernel is lied to, and even when an attacker successfully impersonates the most powerful user on the system, the data remains silent and encrypted.
The core lesson for every security leader is simple: Protect the data, not just the system.
In your current architecture, if an attacker gained root today, what would stop them from seeing your most sensitive data? Secure your Linux workloads today. Don't wait for the next privilege escalation flaw to put your sensitive data at risk.
Three steps you can take now:
- Try self-guided CTE demo.
- Try CTEaaS for FREE on the award-winning Thales Data Protection on Demand (DPoD).
- Contact a Thales Data Security Specialist to learn how CipherTrust Transparent Encryption can fortify your enterprise.