What is the PDPL in Vietnam?
Vietnam's Personal Data Protection Law 2025 (PDPL), enacted as Law No. 91/2025/QH15 on June 26, 2025, and effective from January 1, 2026, represents an upgrade from Decree 13/2023/ND-CP, establishing a comprehensive legal framework for the collection, use, disclosure, storage, transfer, and protection of personal data in Vietnam.

The core purposes of PDPL are as follows:
- Protect individual privacy and interests with clear rules on data collection, processing, storage, sharing, and transfer.
- Limit data use to specific, lawful purposes with consent or legal basis.
- Prevent misuse like unauthorized disclosure, sale, loss, or harmful processing.
- Boost accountability via duties, impact assessments, breach notices, and enforcement.
- Balance data protection with Vietnam’s digital, economic, and security goals.
The PDPL applies broadly to all personal data processing activities within Vietnam, covering the following:
- Vietnamese agencies, organizations, and individuals.
- Foreign agencies, organizations, and individuals in Vietnam.
- Foreign agencies, organizations, and individuals directly engaged in or related to personal data processing of Vietnamese citizens and certain persons of Vietnamese origin residing in Vietnam.
Article 8 of the PDPL introduces a tiered framework for maximum administrative penalties on personal data violations.
Key Penalty Highlights
- Illegal data trading: Up to 10x gains or VND 3 billion.
- Cross-border transfer violations: Up to 5% revenue or VND 3 billion.
- Other violations: Max VND 3 billion fine; half for individuals.
- Enforcement: Administrative sanctions, plus criminal penalties if severe.
COMPLIANCE BRIEF
Vietnam Personal Data Protection Law Compliance
Learn how Thales helps organizations comply with Vietnam’s PDPL through encryption, IAM, data monitoring, and compliance controls.
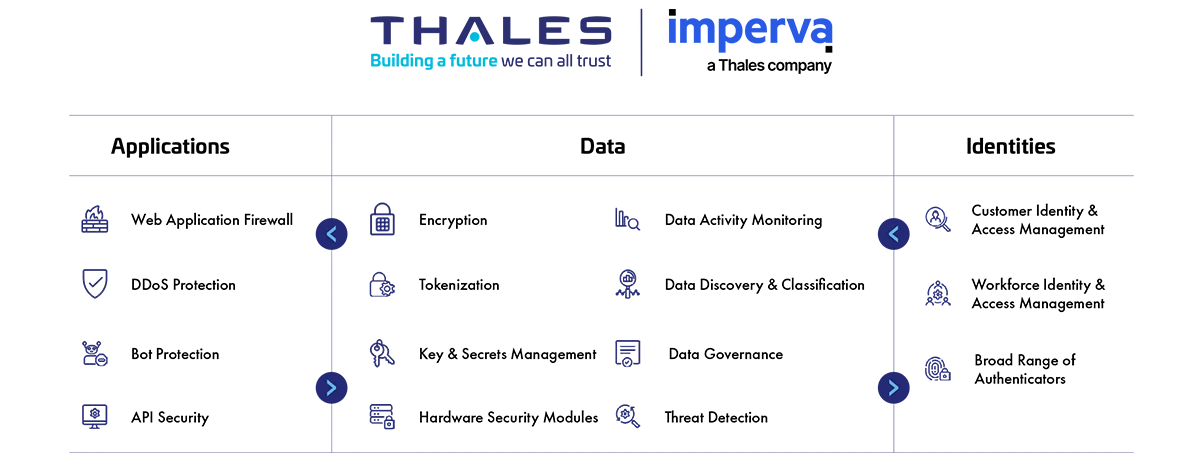
How Thales Helps with the Vietnam Personal Data Protection Law (PDPL) Compliance
Thales’ solutions enable organisations in Vietnam to comply with PDPL, particularly Chapters I, II, and III, by enhancing governance over data protection with comprehensive visibility, control, and automation. Building on the PDPL’s foundational requirements, Decree No. 356/2025/ND-CP – released on December 31, 2025 – provides further details on personal data classification and cross-border data transfer. Thales supports organisations in aligning with both the PDPL and Decree 356, helping streamline compliance processes and ensure adherence to Vietnam’s evolving regulatory framework for data protection. These capabilities also support organisations in meeting the security and data governance expectations introduced by Vietnam’s Law on Artificial Intelligence (No. 134/2025/QH15), by protecting sensitive data used in AI systems through strong encryption, access controls, and data activity monitoring.
PDPL Compliance Solutions
Application Security
Protect applications and APIs at scale in the cloud, on-premises, or in a hybrid model. Our market leading product suite includes Web Application Firewall (WAF), protection against Distributed Denial of Service (DDoS) and malicious BOT attacks, security for APIs, and a secure Content Delivery Network (CDN).
Data Security
Discover and classify sensitive data across hybrid IT and automatically protect it anywhere, whether at rest, in motion, or in use, using encryption tokenization and key management. Thales solutions also identify, evaluate, and prioritize potential risks for accurate risk assessment as well as identify anomalous behavior, and monitor activity to verify compliance, allowing organizations to prioritize where to spend their efforts.
Identity & Access Management
Provide seamless, secure and trusted access to applications and digital services for customers, employees and partners. Our solutions limit the access of internal and external users based on their roles and context with granular access policies and Multi-Factor Authentication that help ensure that the right user is granted access to the right resource at the right time.
Address the Vietnam PDPL 2025
How Thales helps:
- Identify structured and unstructured sensitive data at risk on premises and in the cloud.
- Discover all your data and categorize it based on sensitivity and value, allowing you to uncover hidden data risks.
- Identify the current state of compliance, document gaps, and provide a path to full compliance.
- Gain full sensitive data activity visibility, track who has access, audit what they are doing and document.
How Thales helps:
- Uncover hidden risks with data discovery, classification, and vulnerability assessments.
- Pseudonymize sensitive information in databases.
- Gain full sensitive data activity visibility, track who has access, audit what they are doing and document.
How Thales helps:
- Encrypt data at rest on-premises, across clouds, and in big data or container environments.
- Pseudonymize sensitive information in databases.
- Gain full sensitive data activity visibility, track who has access, audit what they are doing and document.
- Protect the root-of-trust of a cryptographic system within a highly secure environment.
- Limit the access of internal and external users to systems and data based on roles and context with policies.
- Apply contextual security measures based on risk scoring.
How Thales helps:
- Pinpoint sensitive data and ensure the proper user access rights are in place.
- Employ data activity monitoring for structured and unstructured data across cloud and on-premises systems.
- Pseudonymize sensitive data once it is created and make sure cleartext data will not be processed or stored by unauthorized and to prevent exposure of real data applications and personnel.
- Protect sensitive data with real-time alerting or user access blocking of policy violations.
- Remove keys from CipherTrust Manager can ensure secure deletion, digitally shredding all instances of the data.
- Enable Multi-factor Authentication (MFA) with the broadest range of hardware and software methods and form factors.
- Build and deploy adaptive authentication policies based on the sensitivity of the data.
How Thales helps:
- Provide data activity monitoring for structured and unstructured data across cloud and on-prem systems.
- Identify abnormal user behavior and provide a complete threat description with actionable intelligence for remediation.
- Support fine-grained authorization decisions on who may access specific resources and what actions they may perform.
Solutions:
Data Security
Identity & Access Management
How Thales helps:
- Encrypt data at rest on-premises, across clouds, and in big data or container environments.
- Pseudonymize sensitive information in databases.
- Alert or block database attacks and abnormal access requests in real time.
- Monitor file activity overtime to set up alerts on activity that can put the organization at risk.
- Reduce third-party risk by maintaining on-premises control over encryption keys.
- Ensure complete separation of roles between third party and your organization, restrict access to sensitive data.
- Enable relationship management with suppliers, partners or any third-party user; with clear delegation of access rights.
- Protect the root-of-trust of a cryptographic system within a highly secure environment.
- Streamline reporting and analysis of user access rights to sensitive data.
- Enable multi-factor authentication (MFA) with the broadest range of hardware and software methods.
- Build and deploy adaptive authentication policies based on the sensitivity of the data/application.
- Protect against phishing and man-in-the-middle attacks.
- Secure data in transit at Layers 2, 3, and/or 4 without slowing down the network.
- Offer stronger identity and access governance for third-party, supplier, or cross-organization access scenarios related to transferred data.
- Support conditional access for higher-risk or external access journeys.
How Thales helps:
- Locate structured and unstructured regulated data across hybrid IT.
- Pseudonymize sensitive information in databases.
- Encrypt data at rest on-premises, across clouds, and in big data or container environments.
- Manage and monitor access controls to enterprise-wide systems effectively.
- Log all user access and authentication activities.
- Provide centralized user authentication before access to applications that process personal data.
- Support federated authentication, where applications trust a central identity provider for user authentication.
- Adjust access controls based on user behavior, device, and contextual risk at the time of access.
How Thales helps:
- Provide ongoing monitoring of database traffic, monitoring who the users are accessing them, and provide timely alerts.
- Protect personal data from unauthorized access, monitor what has been changed and who is accessing.
- Record access to the database system and detect login attempts on the database system.
- Produce audit trail and reports of all access events to all systems, stream logs to external SIEM systems.
- Manage authentication and access control by supporting Multi-Factor Authentication and Single Sign-On (SSO) and displaying access log reports.
- Detect and alert administrators if abnormal access attempts are found, and administrators can respond quickly.
- Detect and pinpoint critical threats to data, prioritizes what matters most, and provides actionable insights.
- Support the creation of audit trail reports of all accesses for auditing and investigation in the event of any incidents.
- Flag access anomalies for investigation by the security team, and integrate seamlessly with SIEM solutions for a more comprehensive approach to threat and anomaly detection.
- Dynamically evaluate the risk level of each access attempt and apply stronger controls where the risk is higher.
- Enforce multi-factor authentication to reduce the risk of unauthorized access across enterprise applications.
- Centralize authentication and policy enforcement for cloud access scenarios, helping organizations apply consistent access controls.
Solutions:
Data Security
Identity & Access Management
How Thales helps:
- Protect data with real-time alerting or user access blocking of policy violations.
- Identify abnormal user behavior and provide a complete threat description with actionable intelligence for remediation.
How Thales helps:
- Classify and assign specific sensitivity levels for data when you are defining your data stores and your classification profiles for different types of data sets.
- Encrypt sensitive data once it is created and make sure cleartext data will not be processed or stored by unauthorized applications and personnel in removable media.
- Provide data activity monitoring for structured and unstructured data across cloud and on-prem systems.
How Thales helps:
- Discover all of your data and categorize it based on sensitivity and value, allowing you to uncover hidden data risks.
- Deliver data-at-rest encryption with centralized key management, privileged user access control and detailed data access audit logging.
- Apply privileged access control to sensitive data.
- Pseudonymize sensitive information in databases.
- Gain visibility by monitoring and auditing all database activity.
- Detect and pinpoint critical threats to data, prioritizes what matters most, and provides actionable insights.
- Protect the root-of-trust of a cryptographic system within FIPS140-2 Level 3 - a highly secure environment.
- Leverage smart cards for implementing physical access to sensitive facilities.
- Record access to the database system and detect login attempts on the database system.
- Manage authentication and access control by supporting Multi-Factor Authentication and Single Sign-On (SSO) and displaying access log reports.
- Produce audit trails and reports of all access events to all systems, stream logs to external SIEM systems.
- Detect and alert administrators if abnormal access attempts are found, and administrators can respond quickly.
- Flag access anomalies for investigation by the security team, and integrate seamlessly with SIEM solutions for a more comprehensive approach to threat and anomaly detection.
- Offer multiple authentication methods suitable for different access scenarios and data sensitivity levels.
- Support passwordless access journeys that reduce dependency on passwords in modern digital environments.
- Employ certificate-based strong authentication for higher-assurance access scenarios.
- Provide on-premises authentication management for enterprise environments that require internal control over authentication infrastructure.
- Enforce strong user authentication before access to systems that handle biometric or other sensitive personal data.
- Apply contextual access policies to restrict who can reach sensitive systems and under what conditions.
- Enable stronger identity assurance using device-bound modern authenticators suitable for sensitive access journeys.
- Provide centralized access and authentication controls for sensitive applications.
Solutions:
Data Security
Data Discovery & Classification
Identity & Access Management
How Thales helps:
- Encrypt sensitive data once it is created and make sure cleartext data will not be processed or stored by unauthorized applications and personnel in removable media.
- Protect sensitive personal data whether it is in applications or databases and replace sensitive values with format-preserving tokens.
- Provide ongoing monitoring of database traffic, monitoring who the users are accessing them, and provide timely alerts.
- Protect personal data from unauthorized access, monitor what has been changed and who is accessing.
How Thales helps:
- Provide ongoing monitoring of database traffic, monitoring who the users are accessing them, and provide timely alerts.
- Protect personal data from unauthorized access, monitor what has been changed and who is accessing.
- Detect anomaly behavior and provide deeper insight.