What are the MAS TRM Guidelines?
The Monetary Authority of Singapore (MAS) Technology Risk Management (TRM) Guidelines was introduced in 2001 and revised in January 2021, provide a framework of best practices for Financial Institutions (FIs) in Singapore to identify, assess, and manage technology and cyber risks, ensuring the security, reliability, and resiliency of their systems.

The MAS TRM guidelines aim to help FIs proactively manage technology-related risks, safeguard against sophisticated cyber threats, ensure operational continuity, and maintain the integrity of Singapore's financial sector. The 2021 update strengthened the focus on cyber threats and on senior management's accountability for ensuring robust technology risk controls.
The TRM Guidelines apply to all FIs regulated by MAS, including, but not limited to:
- Banks (local and foreign, wholesale, and merchant).
- Insurance companies and intermediaries.
- Capital Markets Services (CMS) Licensees (fund managers, brokers).
- Payment Service Providers and Fintechs (including digital token providers).
The key requirements cover Risk Governance, Cybersecurity Controls, Third-Party Management, Operational Resilience, Systems Development and Incident Reporting.
COMPLIANCE BRIEF
Complying with the MAS TRM Guidelines in Singapore
Learn how to meet MAS TRM guidelines in Singapore with data security, encryption, and access controls for financial institutions.
How Thales Helps with the MAS TRM Guidelines Compliance
Thales’ solutions can help Financial Institutions (FIs) in Singapore address the TRM Guidelines across 11 key requirements by simplifying compliance and automating security with visibility and control, thereby reducing the burden on security and compliance teams.
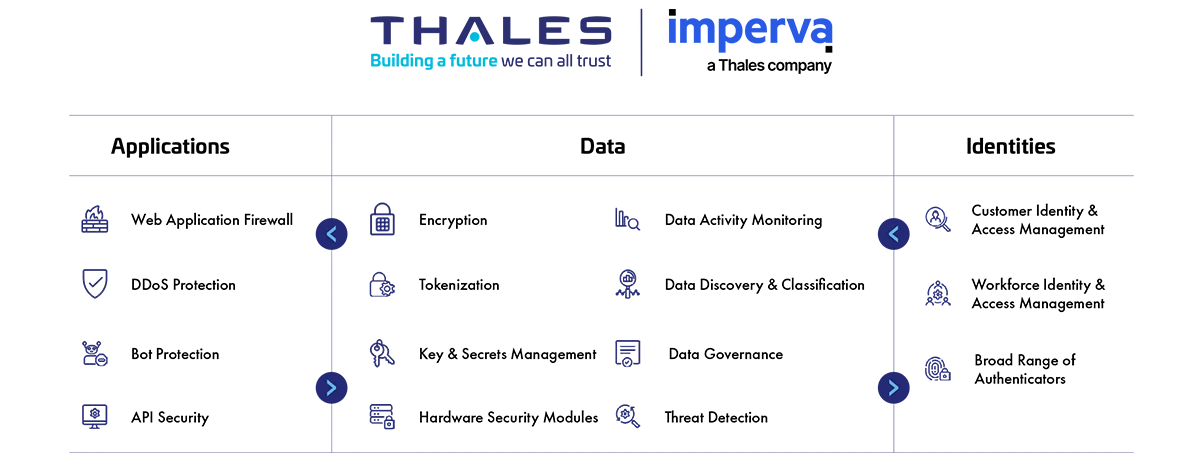
MAS TRM Compliance Solutions
Application Security
Protect applications and APIs at scale in the cloud, on-premises, or in a hybrid model. Our market leading product suite includes Web Application Firewall (WAF), protection against Distributed Denial of Service (DDoS) and malicious BOT attacks, security for APIs and a secure Content Delivery Network (CDN).
Data Security
Discover and classify sensitive data across hybrid IT and automatically protect it anywhere, whether at rest, in motion, or in use, using encryption tokenization and key management. Thales solutions also identify, evaluate, and prioritize potential risks for accurate risk assessment as well as identify anomalous behavior, and monitor activity to verify compliance, allowing organizations to prioritize where to spend their efforts.
Identity & Access Management
Provide seamless, secure and trusted access to applications and digital services for customers, employees and partners. Our solutions limit the access of internal and external users based on their roles and context with granular access policies and Multi-Factor Authentication that help ensure that the right user is granted access to the right resource at the right time.
Address the MAS TRM Guidelines
How Thales helps:
- Manage encryption keys centrally, provide granular access control, and configure security policies.
- Protect cryptographic keys in a tamper-resistant FIPS 140-3 Level 3 validated environment for securing the key lifecycle.
- Detect and pinpoint critical threats to data, prioritize what matters most, and provide actionable insights to accelerate threat investigation and response.
How Thales helps:
- Provide data activity monitoring for structured and unstructured data across cloud and on-prem systems.
- Monitor data access activity over time to set up alerts on activity that can put FIs at risk.
- Offer advanced multi-cloud Bring Your Own Encryption (BYOE) solutions to ensure data mobility to efficiently secure data across multiple cloud vendors with centralized and independent encryption key management.
- Centralize key lifecycle management, including generation, rotation, destruction, import, and export.
- Enforce access controls, including the use of passphrases or key encryption keys. Private keys stored in the HSM remain encrypted and require proper authentication to access.
- Enforce separation of duty between your data and external party as well as your cloud service provider (CSP) by securely storing encryption keys outside of the corresponding cloud.
How Thales helps:
- Run assessment tests on data stores such as MySQL or so to scan for known vulnerabilities.
- Scan your databases with over 1,500 predefined vulnerability tests based on CIS and PCI-DSS benchmarks to help you keep your databases covered for the latest threats.
- Detect and virtually patch database software vulnerabilities.
How Thales helps:
- Classify and assign specific sensitivity levels for data when you are defining your data stores and your classification profiles for different types of data sets.
- Enable continuous monitoring to capture and analyze all data store activity, providing detailed audit trails that show who accesses what data, when, and what was done to the data.
How Thales helps:
- Enforce security-by-design by ensuring sensitive data is protected during system development and modification.
- Provide developers with accessible data protection tools such as encryption and key management to integrate security early in the development lifecycle and foster DevSecOps practices.
- Shift Data Security operations to Data Security Admins, enabling better segregation of duties and change control for system modifications.
- Deploy data protection controls in hybrid and multi-cloud applications to protect DevSecOps.
- Easily access data security solutions through online marketplaces.
- Protect and automate access to secrets across DevOps tools.
- Secure change management by enabling integration tools for versioning, traceability, and rollback capabilities.
How Thales helps:
- Provide continuous discovery and classification potential risk of all public, private, and shadow APIs.
- Monitor API activity, track usage, detect anomalies, and identify potential unauthorized access attempts.
- Offer advanced API Verification capabilities to strengthen your defenses against potential vulnerabilities.
- Safeguard your login endpoints from credential stuffing, brute force attacks, and account fraud.
- Detect and prevent cyber threats with web application firewall, ensuring seamless operations and peace of mind.
- Enable complete visibility and help in singling out enterprise-wide attack campaigns.
- Safeguard critical network assets from DDoS attacks and Bad Bots while continuing to allow legitimate traffic.
- Protect against both volumetric and application-layer DDoS attacks in one scalable solution at ease.
- Deploy data protection controls in hybrid and multi-cloud applications to protect DevSecOps.
- Protect and automate access to secrets across DevOps tools.
- Enable comprehensive secrets management of credentials, certificates and keys, including static secrets, dynamic secrets, SSH keys, API keys and tokens.
- Offer FIPS 140-2 Level 3 root of trust for credentials and keys.
Solutions:
Application Security
Data Security
How Thales helps:
- Run assessment tests on data stores such as MySQL or so to scan for known vulnerabilities.
- Scan your databases with over 1,500 predefined vulnerability tests based on CIS and PCI-DSS benchmarks to help you keep your databases covered for the latest threats.
- Detect and virtually patch database software vulnerabilities.
How Thales helps:
- Leverage smart cards for implementing physical access to sensitive facilities.
- Limit access to systems and data based on roles and context with policies.
How Thales helps:
- Limit access to systems and data based on roles and context with policies.
- Apply contextual security measures based on risk scoring.
- Enable continuous monitoring to capture and analyze all data store activity, providing detailed audit trails that show who accesses what data, when, and what was done to the data.
- Enable the separation of duties between the security administrator and the system administrator inside servers, ensuring the system admins or privileged accounts do not have access to sensitive encryption keys, while the security administrators do not have access to the data.
- Centralize access policies and enforcement to multiple hybrid environments in a single pane of glass.
- Offer “least privilege” access rights where minimum sufficient permissions are granted to legitimate users and adhere to a “deny all” access control policy for users by default.
- Deploy time-bound access which restricts access to a specific period based on the nature of work.
- Adopt robust user authorization and authentication based on the criticality of IT assets by defining the right access policies, step-up authentication, and enforcing phishing-resistant authenticators.
- Manage authentication and access control by supporting Multi-Factor Authentication and Single Sign-On (SSO) and displaying access log reports.
How Thales helps:
- Enforce granular access control (separated from the OS access control) with transparent encryption for privileged users to prevent misuse or abuse.
- Manage system and data access rights (access control) by supporting role-based authorization (RBAC) and conditional authorization (ABAC).
- Control and manage privileged user accounts by supporting the enforcement of multi-factor authentication (MFA) for accessing critical systems.
- Design authorization and approval procedures (User Journey Orchestration) for privileged user accounts and store and display as a privileged user activity report for detailed auditing.
Solutions:
Data Security
Identity & Access Management
How Thales helps:
- Enable secure remote access for employees to all company resources on-premises or in the cloud with a seamless user experience.
- Enable MFA with the broadest range of hardware and software methods.
- Build and deploy adaptive authentication policies.
- Offer Remote Access Policies to control only pre-approved users.
- Store Remote Access Logs to support retrospective auditing.
- Encrypt data sent over remote connections (Data-in-Transit Encryption) to prevent data interception during communication.
Solutions:
Identity & Access Management
How Thales helps:
- Offer leading cryptographic solutions that are rigorously tested, validated, and compliant with internationally recognized standards, such as FIPS 140-3 and Common Criteria Certifications.
- Support algorithms such as AES, SHA-2 family, ECDH, RSA, and ECDSA, ensuring the use of strong and approved algorithms in cryptographic operations.
- Offer native support to NIST-Standardized PQC Algorithms: ML-KEM (FIPS 203) and ML-DSA (FIPS 204).
How Thales helps:
- Centralize key lifecycle management tasks including generation, rotation, destruction, import and export.
- Protect cryptographic keys in a tamper-resistant FIPS 140-3 Level 3 validated environment for securing the key lifecycle.
- Automate key lifecycle management across clouds and hybrid environments with processes and tools.
- Manage and protect all secrets and sensitive credentials.
- Protect cryptographic keys in a FIPS 140-3 Level 3 environment.
- Ensure secure deletion by removing keys from CipherTrust Manager, digitally shredding all instances of the data.
- Provide an additional layer of protection beyond the physical security controls with Secure Transport Mode – the logical control validation capability. Utilize 'Secure Transport Mode' to logically lock the HSM during shipment. Upon receipt, administrators can cryptographically verify that the device has not been tampered with or modified before deploying it into production.
- Establish secure, authenticated communication channels for key management and cryptographic operations, using protocols compliant with standards such as NIST SP 800-56A/B and RFCs for TLS, SSH, and IPsec.
- Offer key rotation that can assist in case of recovery where cryptographic keys are compromised. Keys can be rotated on demand to minimize the impact of any key compromises.
How Thales helps:
- Identify the current state of data compliance and document gaps.
- Encrypt data at rest on-premises, across clouds, and in big data or container environments.
- Monitor active processes to detect ransomware – identifying activities such as excessive data access, exfiltration, unauthorized encryption, or malicious impersonation of a user, and alerts/blocks when such an activity is detected.
- Provide on-premises solutions for data discovery, classification and protection to FIs to achieve “same security standards”.
- Pseudonymize sensitive data once it is created and make sure cleartext data will not be processed or stored by unauthorized and to prevent exposure of real data applications and personnel.
- Protect the root-of-trust of a cryptographic system within FIPS140-3 Level 3 - a highly secure environment.
- Protect data in motion with high-speed encryption.
- Protect data in use by leveraging confidential computing.
- Examine application and database traffic automatically to create a profile of baseline normal activity.
- Gain full sensitive data activity visibility, track who has access, audit what they are doing and document.
- Pinpoint risky data access activity for all users, including privileged users.
- Protect data with real-time alerting or user access blocking of policy violations.
How Thales helps:
- Limit access to systems and data based on roles and context with policies.
- Apply contextual security measures based on risk scoring.
- Enable continuous monitoring to capture and analyze all data store activity, providing detailed audit trails that show who accesses what data, when, and what was done to the data.
- Centralize access policies and enforcement to multiple hybrid environments in a single pane of glass.
- Provide a unified strategy for access control across all user populations.
- Enable a consistent and policy-driven approach to identification, authentication, and authorization of all users to their IT assets, data, and services.
- Manage all users, including the workforce, contractors, third-party users such as customers, suppliers, logistics, and B2B or B2C type users.
How Thales helps:
- Offer a highly available and distributed security architecture that eliminates single points of failure and protects critical systems from network faults and cyber threats, and supports reliable network service delivery.
- Classify and assign specific sensitivity levels for data when you are defining your data stores and your classification profiles for different types of data sets.
- Provide instant protection against both volumetric and application-layer DDoS attacks in one solution.
- Leverage 60+ global PoPs to absorb large attacks, avoiding costly hardware or over-provisioning—elastic defense scales automatically.
Solutions:
Application Security
Data Security
How Thales helps:
- Control and manage access to IT systems from external networks (teleworking) by supporting Multi-Factor Authentication (MFA) and Risk-Based Authentication.
- Set policies for administrators to approve connections from external networks and display results as remote access activity reports.
- Manage access policies for mobile devices, such as checking security patch installations and device settings, and enforcing antivirus and malware policies.
- Check devices before granting access to IT systems in cases where employees are allowed to use BYOD, such as preventing connections from rooted or jailbroken devices and forcing the installation of updated anti-malware to prevent threats from personal devices.
Solutions:
Identity & Access Management
How Thales helps:
- Integrate key management with VMware to enable VM image encryption and VSAN encryption.
- Enable data inside VMs and containers to be secured via encryption and access control transparently without any changes to the application.
How Thales helps:
- Produce audit trail and reports of all access events to all systems, stream logs to external SIEM systems.
- Detect and alert administrators if abnormal access attempts are found, and administrators can respond quickly.
- Detect and pinpoint critical threats to data, prioritizes what matters most, and provides actionable insights.
- Support the creation of audit trail reports of all accesses for auditing and investigation in the event of any incidents.
- Flag access anomalies for investigation by the security team, and integrate seamlessly with SIEM solutions for a more comprehensive approach to threat and anomaly detection.
- Examine application and database traffic automatically using machine learning and behavioral analytics to create a profile of baseline normal activity, and detect and prioritize anomalous activity.
- Offer correlation with risk analytics that filters out false positives and enables security teams to act only on higher-risk incidents that need further investigation.
Solutions:
Data Security
Identity & Access Management
How Thales helps:
- Run assessment tests on data stores such as MySQL or so to scan for known vulnerabilities.
- Scan your databases with over 1,500 predefined vulnerability tests based on CIS and PCI-DSS benchmarks to help you keep your databases covered for the latest threats.
- Detect and virtually patch database software vulnerabilities.
How Thales helps:
- Encrypt all sensitive data at both client and host applications prior to transmission using AES-256 or equivalent encryption standards.
- Protect encryption keys associated with the digital signatures and secure cryptographic operations in a FIPS 140-3 Level
- 3 validated tamper-resistant device.
- Manage encryption keys centrally, provide granular access control, and configure security policies.
- Safeguard critical network assets from DDoS attacks and Bad Bots while continuing to allow legitimate traffic.
- Offer a guaranteed SLA of 3 seconds or less for DDoS attacks targeting Layers 3 and 4, and protect FIs against volumetric and protocol-based threats.
- Block threats such as SQL injection, XSS, and other OWASP Top 10 vulnerabilities – safeguarding web applications from threats.
- Offer proactive managed rules to assure FIs have the most-up-date protection against common attack vector threats.
How Thales helps:
- Leverage advanced algorithms and machine learning to analyze user behavior, device fingerprints, location, and transaction patterns during online sessions, identifying anomalies before fraud occurs and automatically blocking high-risk access or transactions.
- Provide dynamic risk scoring with >99% accuracy to distinguish legitimate users from threats and enabling automated actions.
- Support multi-channel (mobile, web, desktop) continuous monitoring compliant with standards like PSD2 SCA and FFIEC, with customizable rules for FIs to enforce policies tailored to their transaction types and risk thresholds.
- Use anonymized global intelligence from billions of events to flag devices/IPs linked to prior fraud, reducing manual reviews and ensuring proactive blocking of fraudulent online financial transactions.
How Thales helps:
- Provide audit trails of API calls, authentication attempts, and authorization decisions, ensuring accountability and facilitating compliance audits.
- Produce audit trail and reports of all access events to all systems, stream logs to external SIEM systems.
- Prevent unauthorized access and alteration to its internals, including the audit logs.
- Gain visibility by monitoring and auditing all database activity.
- Provide a clear audit trail for demonstrating cryptographic control from centralized key management systems, logging all key lifecycle events such as key creation, rotation, and access.
- Offer encryption logs, data access attempts, and encryption/decryption events, providing auditable proof of data protection without application modifications.
Solutions:
Application Security
Data Security
Identity & Access Management