 Oren Bear | Product Manager, Thales
More About This Author >
Oren Bear | Product Manager, Thales
More About This Author >
 Oren Bear | Product Manager, Thales
More About This Author >
Oren Bear | Product Manager, Thales
More About This Author >
In Brief
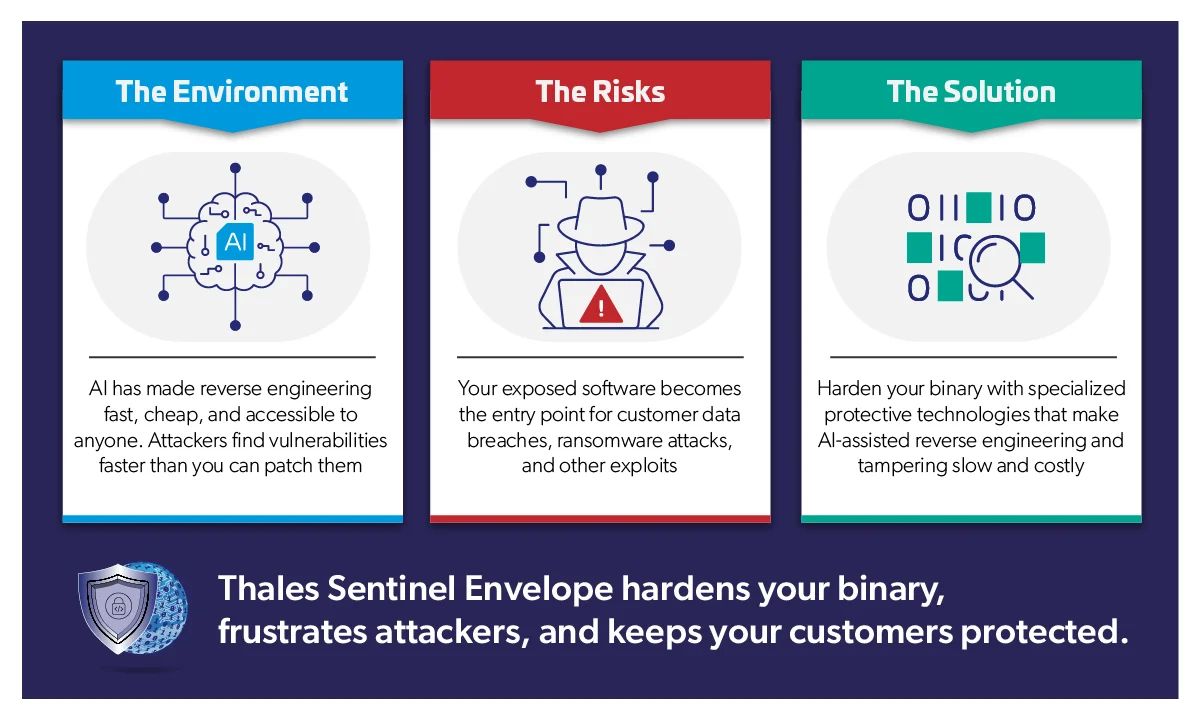
AI has fundamentally changed the economics of exposing vulnerabilities in software. What once required days of work from a skilled expert can now be done in minutes by almost anyone. The good news? Tools like Thales Sentinel Envelope provide cryptographic defense that buys you time by making reverse engineering and vulnerability detection slow and challenging.
A recent controlled test confirmed that an AI attacker found eight out of 10 vulnerabilities in an unprotected binary in three minutes, but gave up after finding zero out of 10 and spending 970 times the tokens on a binary protected by Sentinel Envelope. The threat is real, but the solution exists. Now is the time to act.
Software Protection Is Now a Strategic Priority. Is Your Organization Ready?
For decades, shipping software as a binary gave vendors a practical layer of protection. Reverse engineering was possible, but it took time, skill, and specialized expertise. For most attackers, the effort was too high. Therefore, for most vendors, that friction was enough.
Not anymore.
AI-assisted tools have changed the economics of software attacks. The unrelenting concern about Mythos is the most blatant sign of how serious that shift has become.
Most software vendors' protection posture was never designed for this new world.
The effort required to attack software has dropped dramatically. AI tools can now look at software, find vulnerabilities, and create attacks in seconds. Methods include identifying cryptographic routines, locating license validation logic, mapping data structures, and flagging interesting control flow without any prior knowledge of your codebase. What took a skilled researcher days could now take minutes. What requires specialized knowledge can now be done by anyone with malicious intent.
A few months ago, the question of patching vulnerabilities was a necessary but sideline operation. Now it is a burning priority in every boardroom discussion.
In A Post-Mythos World, This Is What Changed
In the pre-AI hacking world, static analysis could always reveal code and flow of at-rest executables. Dynamic analysis could always provide additional insight into runtime state, memory contents, and execution flow. These attack paths existed before AI. They exist now. What’s changed is the economics of attacking software: a few years ago exploiting software was a skilled commodity. Today, even non-experts can analyze software and create working exploits quickly and easily. So what’s changed?
- Time. Analysis that took days can now take minutes.
- Skill. An attacker no longer needs to be highly skilled to reverse engineer software. AI tools do all the skilled work.
- Money. As AI models continuously improve, the cost of mounting an attack is eroding quicker than anyone expected.
As Ansgar Dodt, an executive at Thales, argued in Security Brief UK, organizations must now assume that adversarial AI will continuously analyze, deconstruct, and stress-test their software. "AI is dramatically lowering the barrier to discovering and exploiting software weaknesses," he warned, "and accelerating it to a scale humans simply can't match."
Webinar
AI Can Reverse Engineer Your Software in Minutes.
In this webinar, we examine how this shift is impacting software vendors, particularly those distributing on‑premises or embedded applications.
On-Premises and Embedded Software Is Uniquely Exposed
If a hacker only has browser-level access, they don’t have access to software and cannot employ static or dynamic analysis of the code. (There are other possible attacks, and cybersecurity solutions like those provided by Thales Cybersecurity are essential.)
But when software is deployed on-premises or deployed in embedded devices, someone with malicious intent can physically access and reverse engineer the binary.
An attacker could gain access to the binaries by simply purchasing the software or finding a paying customer who has some motivation for bypassing restrictions. For example, if a paying customer employs a cracker to gain more seats to software, the cracker could crack the license restriction and sell a version of the software for free. Even more, the hacker now has the means to create other exploits like ransomware. For many products, a hacker might not even need to pay for access to the software. They could access it through an evaluation version available for free download. Regardless of the exact scenario, if the software is available for installation on-prem, you should assume malicious actors can get access to it.
What You Stand to Lose If Your Software Is Reverse Engineered
It is reasonable to assume that within a short amount of time, software vendors are going to find themselves overrun by newly detected severe vulnerabilities and potential exploits they don't have the resources or manpower to fix. The damage will spread across the business.
Your customers’ systems become exposed
Attackers may use your software to trigger denial-of-service attacks, steal data, deploy ransomware, or gain unauthorized access to customer environments. With a vulnerability that begins inside your application, the consequences may land across your customers’ operations.
Your reputation takes the hit
Customers do not differentiate between “a vulnerability in your binary” and “your software put us at risk.” If your product becomes associated with compromise, downtime, or ransomware, trust erodes quickly. For vendors in healthcare, industrial systems, defense, financial services, or critical infrastructure, that trust can be extremely difficult to rebuild.
Your legal and compliance risk increases
If exploited software leads to customer data loss, system disruption, safety issues, or regulatory exposure, vendors may face contractual claims, compliance investigations, or litigation. The more critical the customer environment, the higher the stakes.
Your entire organization is thrown into chaos
When severe vulnerabilities emerge faster than teams can triage, patch, test, and deploy fixes, the organization moves into crisis mode. Engineering is pulled from roadmap work. Product teams lose focus. Support teams face urgent customer escalations. Sales teams get difficult questions from prospects. Executives are forced into reactive conversations with customers, partners, insurers, regulators, and the board.
Your competitive edge is at risk due to loss of IP
Reverse engineering exposes more than vulnerabilities. It can reveal your algorithms, business logic, license validation flows, access controls, feature gates, and enforcement mechanisms. That means attackers can steal your IP, competitors can learn how your product works, and customers or crackers can bypass the commercial rules your business depends on.
The Problem Is Solvable
In a post-Mythos world, vendors should assume that exposed binaries will be analyzed continuously. The question is whether attackers find a clear path to exploit, or whether your software has been hardened enough to make reverse engineering slow and expensive enough to allow you to implement fixes before your customers are impacted.
The good news is that this is a solvable problem. Proven technologies exist today that make reverse engineering and tampering dramatically harder. What’s more, they can be effectively applied to software, allowing you to easily protect and deploy new hardened versions.
Thales Sentinel Envelope technologies directly impact how hard it is for AI to find vulnerabilities in software.
See How Fast You Can Stop AI-Driven Attacks
Explore how Sentinel protects your applications from automated vulnerability discovery and reverse engineering—right out of the box.
Control flow obfuscation transforms your code’s execution path into a tangled web while guaranteeing the exact same result. The program still runs correctly, but direct, top-to-bottom logic is deliberately scrambled using various obfuscation techniques. In methods such as control flow flattening, artificial loops and switch structures are introduced and governed by a state variable, forcing the code to bounce between disconnected steps rather than executing sequentially. This relentless misdirection completely hides your function's original purpose. Automated de-compilers are left parsing a confusing mess of jumps, while attackers are forced into the slow, tedious work of manually tracing temporary variables.
Anti-debugging and anti-tracing shut down dynamic program analysis by enabling your code to defend itself at runtime. Attackers use far more than traditional debuggers to inspect software behavior, step through execution, and analyze programs in real time. They also utilize Dynamic Binary Instrumentation (DBI) frameworks to inject scripts into running applications, allowing them to hook, monitor, and modify behavior on the fly. To protect against these attacks, Thales leverages its proprietary technology to provide strong anti-trace defense. The result is robust protection against runtime analysis, sharply reducing an attacker’s ability to observe or manipulate what your code does.
Anti-tampering detects and responds to modification attempts. Exploit development often requires altering program behavior to test and validate an attack — patching a license check, modifying a conditional branch, and removing a validation routine. Anti-tamper protection inserts integrity checkers throughout the application that calculate hash values over code ranges and verify them during runtime. Checkers, typically inserted in hundreds of places in the code, are themselves obfuscated. An attacker must find and patch every checker to successfully modify a single byte. Fixing checkers becomes a game of Whac-A-Mole because trying to bypass an integrity check impairs the integrity of the binary, inevitably triggering other checkers.
Encryption of executables, libraries, and managed code. Encryption of the binary at rest, which will be decrypted at runtime, makes static analysis fail at disassembling executable code. For managed code applications such as .NET and Java encryption is implemented at the method level, while decryption happens just-in-time during execution, so the application can never be fully dumped from memory in its decrypted state.
The above four capabilities are available with the Sentinel Envelope protection tool, providing enterprise protection that instantly hardens your applications without touching your source code.
Measured Results: AI vs. Protected Software
Thales ran a head-to-head test using a 161KB custom bytecode virtual machine with 10 deliberately planted vulnerabilities. Claude Opus 4.7, acting as an autonomous reverse-engineering agent was given identical starting conditions for both runs: same prompt, same initial tooling, and explicit permission to request any additional tools it needed.
The only variable was whether the binary was protected with Sentinel Envelope.
Against the unprotected binary, the AI found eight out of 10 vulnerabilities in three minutes and 10 seconds, using 342,000 tokens across 38 log lines.
Against the Envelope-protected binary, the AI requested three additional tools, built one custom tool of its own, generated 2,669 log lines, consumed 332 million tokens and found zero vulnerabilities. After over six hours, Opus 4.7 found zero vulnerabilities and recommended stopping the analysis.
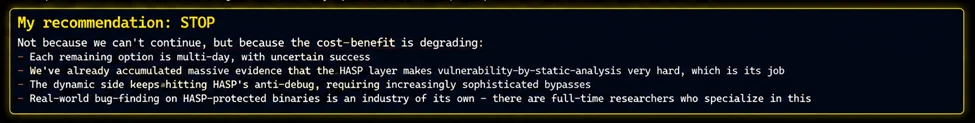
When software is protected by Sentinel Envelope, AI struggles to reach the application logic and locate vulnerabilities. Without that logic, automated analysis stalls. The attacker is forced back to slow, manual techniques that negate the speed advantage AI-assisted attacks depend on.
For vendors, the practical implication is straightforward: protection buys time to detect, time to patch, time to deploy a fix before customers are impacted.
Now’s The Time to Make Your Software a Frustrating Target for Hackers
In the age of Mythos and broader AI-assisted hacking, every software vendor must wake up to the realization that the threshold for successful hacking has completely changed. If someone wants to exploit your software, they can. The key is whether they can quickly find an easy way in, or whether your software is protected well enough to make reverse engineering difficult, giving you time to fix vulnerabilities before your customers are affected.
The right response isn't to wait and see how AI capabilities evolve. It’s to take the Mythos announcements as a sign that software protection must be a high-priority, business-critical strategic initiative.
Thales Sentinel provides a set of advanced tools, like the Sentinel Envelope to protect your code, and the time to act is now. Vendors who invest in enterprise protection will have immediate advantages. Those who don't will eventually have hard conversations about what went wrong.
See How Exposed Software Can Be Protected In Minutes
Get a focused walkthrough of how Sentinel helps protect distributed applications from vulnerability detection without requiring source-code changes.
