Tokenization Choices
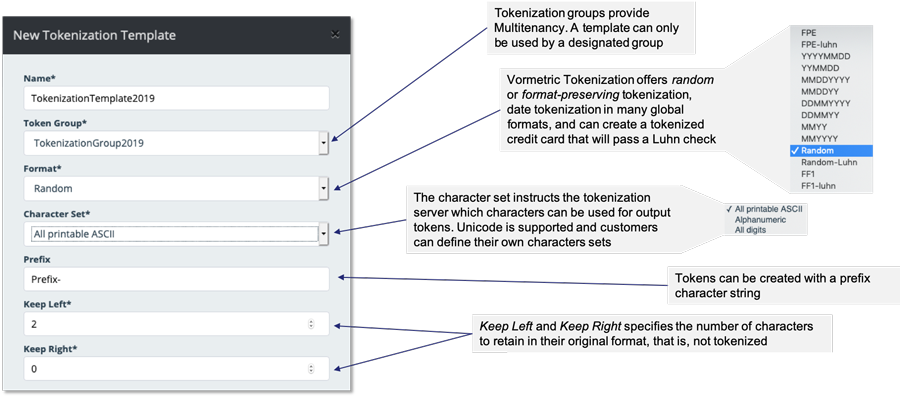
Vormetric Tokenization combines the scalability and availability benefits of a vaultless solution with business-centric options for protecting data: both format-preserving and random tokenization. Format-preserving tokenization enables data protection without changing database schemas and offers irreversible tokens. Random tokenization offers high performance, convenient data protection. Date-specific tokenization supporting the full range of international date formats helps ensure PII and transaction security.
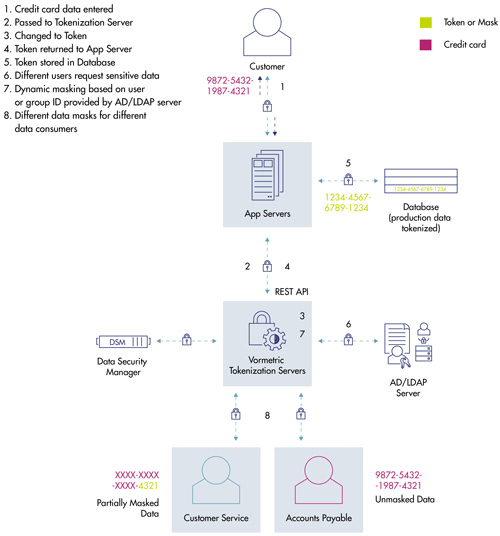
Dynamic Data Masking
Administrators can establish policies to return an entire field tokenized or dynamically mask parts of a field. For example, a security team could establish policies so that a user with customer service representative credentials would only receive a credit card number with the last four digits visible, while a customer service supervisor could access the full credit card number in the clear. Looking for static data masking? Vormetric Tokenization offers static data masking, but, for the broad range of static data masking use cases, consider Vormetric Batch Data Transformation.
Multi-tenancy Support
The Tokenization Server supports multi-tenancy with Tokenization groups. Tokenization groups ensure that data tokenized by one group cannot be detokenized by another, and are centrally managed.
Centralized Tokenization Templates
At the core of the programming simplicity of Vormetric Tokenization is the tokenization template.
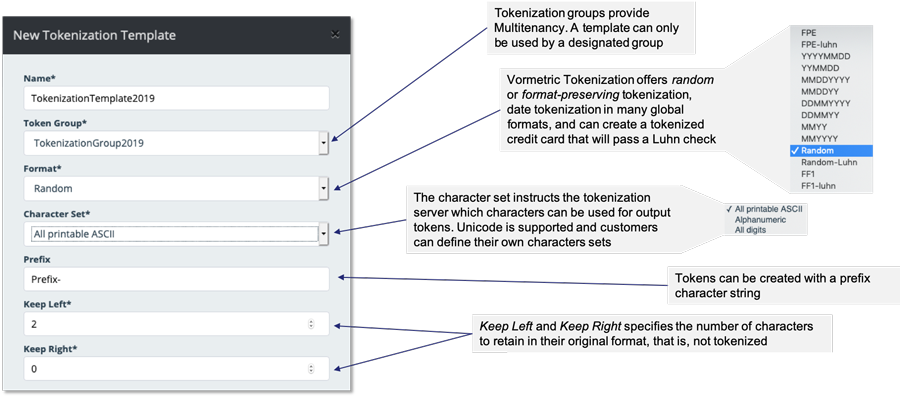
The centralization of tokenization configuration enables a tokenization request to contain, simply, the tokenization group name, template name and the data to tokenize (along with username and password and the URL of the Tokenization Server). From there, all tokenization work is performed centrally on behalf of the software engineer.
Simple, Non-Disruptive Implementation
Tokenization mechanisms, methods and dynamic data masking rules are defined in a centralized, friendly graphical user interface (GUI). This dramatically reduces programming required for data protection. In addition, a range of format-preserving tokenization mechanisms are available to reduce requirements for changing the database schema. The Tokenization Server’s virtual appliance form factor enables fast scaling.
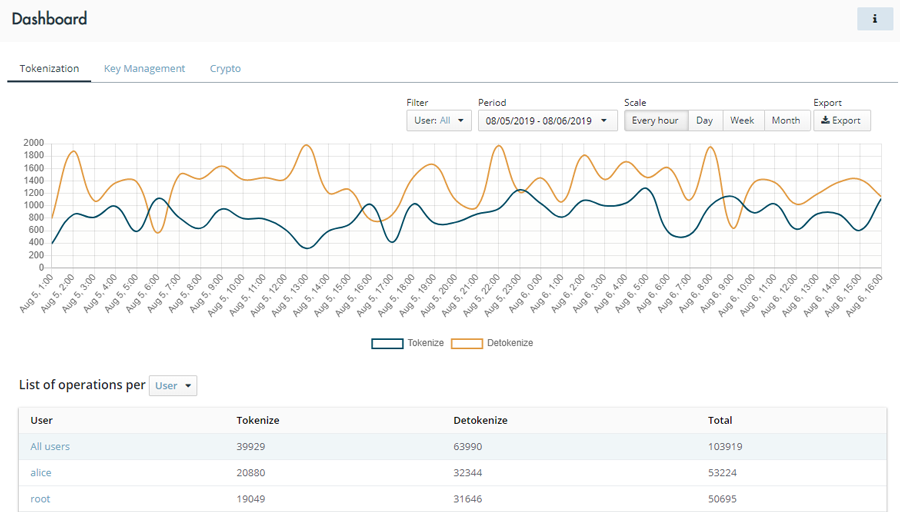
Tokenization Server Dashboard
Once deployed, the Vormetric Tokenization Server becomes a mission-critical part of the data security infrastructure. In support of that, the server presents an information-rich dashboard upon login, showing users and use of the server with exportable data.
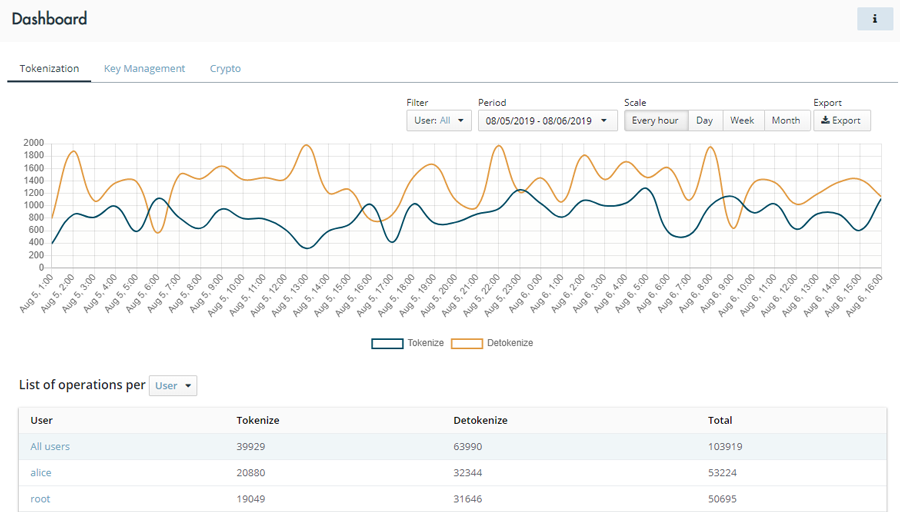
Tokenization Server Dashboard