 Lynne Murray | Director of Product Marketing for Data Security
More About This Author >
Lynne Murray | Director of Product Marketing for Data Security
More About This Author >
 Lynne Murray | Director of Product Marketing for Data Security
More About This Author >
Lynne Murray | Director of Product Marketing for Data Security
More About This Author >
Multi-cloud data security threats are escalating at an unprecedented rate. According to Forrester and the 2025 Thales Global Cloud Data Security Study, the primary drivers of multi-cloud risks are: growing complexity, insufficient access controls, and the rapid rise of AI. As organizations expand across multiple cloud platforms, they face growing challenges related to shadow data, regulatory compliance, and inconsistent access controls in disparate clouds.
Collectively, these challenges create a significant data security vulnerability. Nearly 89% of organizations struggle for clarity about what data exists, where, and how to safeguard it. AI further exacerbates vulnerabilities by expanding data creation, access, and usage, rendering many traditional data security tools inadequate. As a result, multi-cloud data security has become a Board of Directors’ priority.
In a recent webinar, guest speaker Heidi Shey, Principal Analyst, Forrester, and Todd Moore, Global VP/GM of Data Security Products, Thales, discussed critical data security strategies, focusing on the role of Data Security Posture Management (DSPM) in tracking and protecting data throughout its lifecycle. They answered the five most pressing questions and highlighted the essential need for automated, centralized security approaches for addressing the visibility and compliance challenges inherent in complex hybrid, and multi-cloud environments.
1. Where are the biggest blind spots in multi-cloud data protection?
Limited visibility remains one of the most persistent challenges in multi-cloud environments. Siloed cloud platforms, each with its own cloud-native data tools, restrict an organization’s ability to gain a comprehensive understanding of its data landscape. Without unified visibility, classification, and protection and enforcement controls, sensitive data becomes increasingly difficult to manage at scale.
2. Which data security use case should be prioritized?
The most fundamental question organizations need to answer is: “What data needs to be protected?” Regulated data, such as PII and PCI, requires protection. Beyond that, intellectual property, sensitive corporate information, and organizational secrets that may be embedded in code also need to be secured. All data must be protected throughout its entire lifecycle, including secure disposal.
3. How do you track risk to risk?
Equally important is recognizing the risks that must be addressed. While compliance risk has traditionally been the main priority for security programs, two emerging forces are rapidly amplifying data risk—and accelerating the need for stronger mitigation strategies:
It’s important to understand the types of data risk because, as Heidi Shey says, “Different types of data risks require different types of controls and mitigation.”
The three types of data risks are:
- Risks to data, which stem from:
- External cyber threats, such as bad actors that try to steal your data
- Resiliency concerns from internal practices, like back-up data sources that have not been tested, and cannot reliably and rapidly restore data in the case of a breach
- Asset disposal, such as decommissioning equipment containing data not removed from the device
- Quantum computing can break today’s encryption methods. Post-quantum cryptography (PQC) is needed to future-proof data security
- Risks from data, arising from how you are using the data
- Unethical use of data, such as biased algorithms in AI
- Data sprawl, for example, customer data in local spreadsheets, CRM, and data warehouses
- Noncompliant data or poorly governed data can produce flawed or risky outcomes when used, especially in AI-driven decision-making
- Risks in data, resulting from data management gaps
- Data integrity can be incomplete, inaccurate, invalid, inconsistent, or even poisoned data
- Data lifecycle management must properly handle redundant, obsolete, and trivial (ROT) data, so that, for example, stale data is not fed into AI algorithms
There are different types of data risks, requiring different controls and mitigations
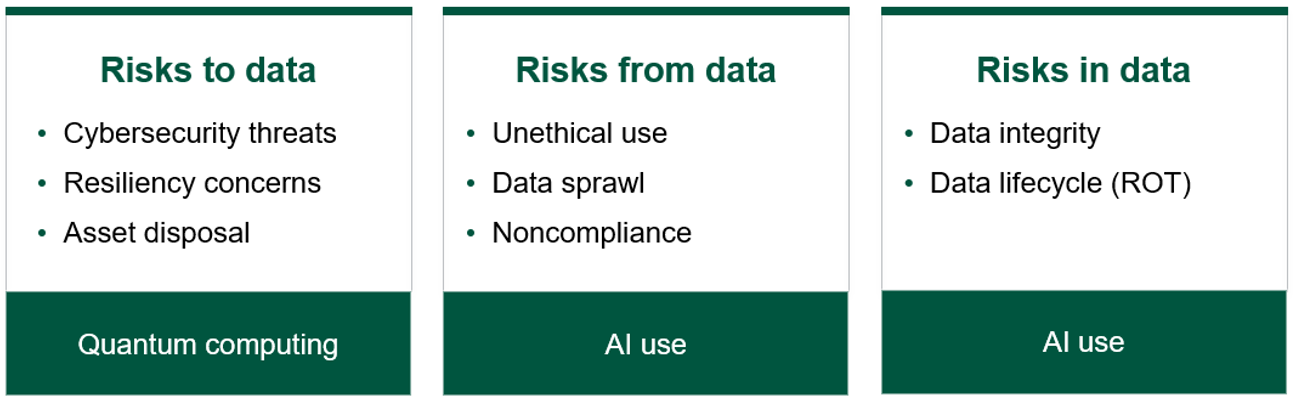
Source: Forrester Research
4. How does AI impact sensitive data?
Moving at the speed of AI: As AI adoption surges, so does AI’s access to sensitive data. Organizations must evolve their risk planning and threat models accordingly, and use AI to enhance defensive tactics such as threat and gap analysis, detection validation, and automated remediation.
In parallel, AI-driven attacks, exploitation of vulnerabilities, and system malfunctions introduce additional layers of complexity that security teams must be prepared to navigate.
Transition to quantum-safe security: Organizations should begin preparing for post quantum cryptography by conducting an inventory of where encryption is used across the organization today and building a clear roadmap to upgrade to modern, quantum resilient standards as they emerge.
Per Todd Moore, “While AI and quantum computing introduce new risks, preparing for them simultaneously requires organizations to discover, classify, cleanse, and protect their data—using techniques such as masking and tokenization—before that data is put to use.”
5. Why there is a need to fortify cloud-native controls with DSPM?
Cloud service providers (CSPs) offer cloud-native data security tools designed to protect data in their individual platforms. However, relying solely on cloud-native security features introduces several risk deficiencies. These deficiencies stem from variances in visibility, capabilities, configurability, and inter-platform coordination.
Each CSP implements distinct security controls, APIs, and configuration standards such as AWS GuardDuty, Azure Security Center, and GCP Security Command Center. Differences in firewall capabilities, intrusion prevention, and threat intelligence integration may leave workloads inconsistently protected because a vulnerability addressed in one cloud platform may remain exposed in another.
In short, cloud-native tools alone cannot deliver consistent or comprehensive data protection in multi-cloud environments. Overreliance on these tools often increases operational complexity, fragments security controls, and creates blind spots that elevate overall risk.
Summary: The end goal is to reduce risk in multi-cloud environments
To address these challenges, organizations are increasingly adopting data security posture management (DSPM) as a dedicated security discipline for multi-cloud environments. DSPM-based tools enable a data-first approach by automating data discovery, classification, risk assessment, and encryption protection across hybrid and multi-cloud infrastructures.
A unified approach to securing data must span all states of —data creation, data in motion, data at rest, and data in use. In multi-cloud environments, where risk continues to rise, traditional tools leave critical data exposed and limit the ability to safely leverage AI and prepare for a post-quantum future.
As Todd Moore explains, “By consolidating discovery, monitoring, protection, and control into a single, unified platform across clouds, organizations can reduce blind spots, simplify operations, and regain control over their data. DSPM illuminates a clear path forward—bringing visibility and resilience to multi-cloud data security and enabling a safer, more secure data future.”
Listen to the full Thales and Forrester webinar here
Learn more about Thales Data Security Posture Management
Learn more about Thales CipherTrust Data Security Platform