Vormetric Protection for Teradata Database
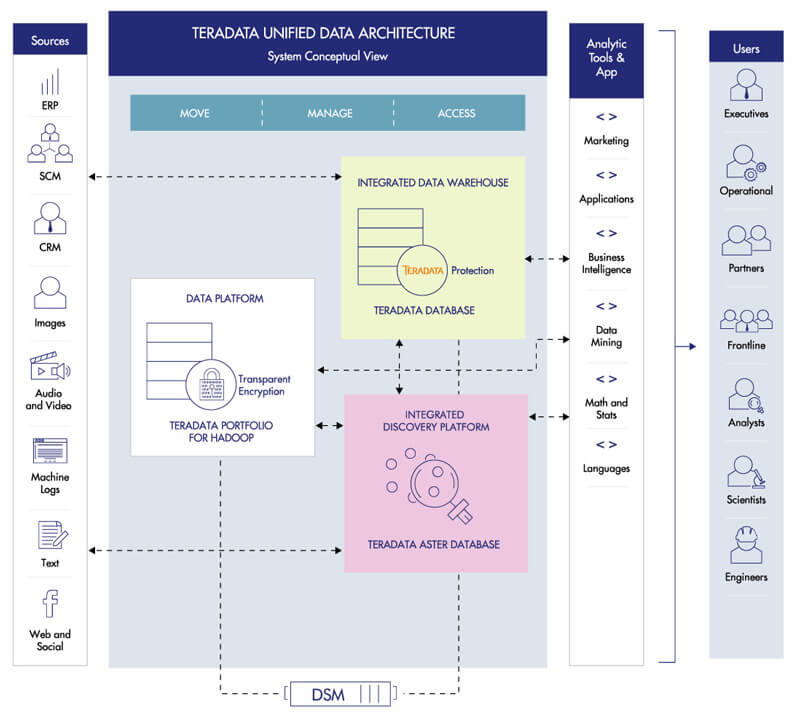
Teradata leverages all of the data, all of the time, so you can analyze anything, deploy anywhere, and deliver analytics that matter. But the aggregation of data can also present risks. Thales enables your organization to guard against such security risks. Vormetric Protection for Teradata Database makes it fast and efficient to employ robust data-at-rest security capabilities in your Teradata environments, on premises, in the cloud, or anywhere in between
- Benefits
- Features
- Specifications
Simplifies Encryption Deployments
Vormetric Protection for Teradata Database enables efficient encryption of specific fields and columns in Teradata databases, and can encrypt sensitive records without altering their format or field schemas.
Centralizes Key and Policy Management
Vormetric Protection for Teradata Database works seamlessly with the Vormetric Data Security Manager, so you can centrally manage keys and access policies for encryption products from Thales and other vendors.
Reduces Development Complexity
Vormetric Protection for Teradata Database reduces complexity for developers by offering standards-based application programming interfaces (APIs) and user-defined functions (UDFs) that can perform cryptographic and key management operations.
Robust Security
The solution offers granular protection, enabling encryption of specific fields and columns in Teradata environments. With the solution, you can apply unique keys to different columns. As a result, you can enforce granular controls so administrators can perform operational tasks, without accessing sensitive data in the clear. Further, the solution features a hardened, FIPS-certified appliance for administration and key storage.
High Performance
With Vormetric Protection for Teradata Database, you can harness the high performance required to support your processing-intensive big data environments. The big data security solution efficiently scales with the number of Teradata nodes in your environment.
Non-Disruptive Implementation
The solution offers format-preserving encryption capabilities that minimize the storage increase and disruption associated with encryption. The solution's UDFs for encryption and decryption can easily integrate into existing SQL code. With the solution, Teradata users can set up their own easily configurable profiles for submitting encryption and decryption requests, including choosing from standard AES encryption and format-preserving encryption.
Teradata database minimum version 14.0
SUSE Linux Enterprise Server (SLES) minimum versions 10
Maximum column widths
ASCII—16KB, Unicode UDFs—8KB
Separation of duties
Administrators manage infrastructure without clear-text data access
Column-level protection
Schema preserving encryption
Centralized key management
Teradata database, Hadoop, and other environments