
Vormetric Data Security Manager and its agents
reached End of Support on June 30, 2024
Customers can easily migrate to CipherTrust Manager and the CipherTrust Data Security Platform Connector product family.
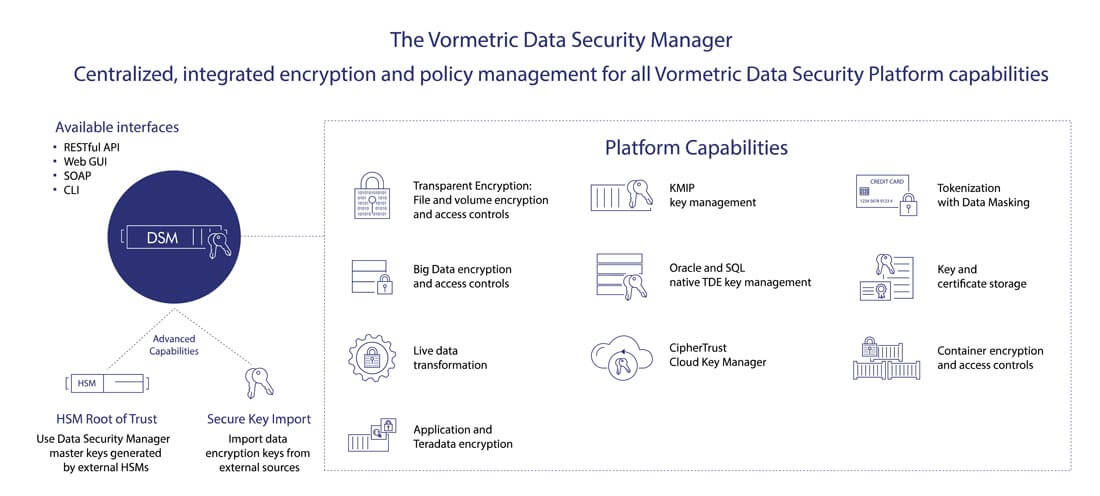
Centrally manage your organization's data security environment
The Vormetric Data Security Manager (DSM) is the central management point for all Vormetric Data Security Platform products. The DSM not only creates, stores and manages the encryption keys that protect data, it also enables organizations to manage every aspect of their Vormetric data security platform implementation. The Data Security Manager allows administrators to specify data access policies, administer DSM users and logical domains, generate usage reports, register new hosts, access security logs, manage third-party keys, digital certificates and more. Moreover, as enterprises and service providers need data security management in concert with their other infrastructure, the DSM also provides integration capabilities with multiple APIs and a command line interface as well as a simple graphical user interface (GUI) operation.

- Benefits
- Features
- Specifications
Unified, Simplified Management
The Data Security Manager (DSM) enables centralized management of data security policies and key management, simplifying training, deployment and operations.
Flexible Form Factors
The Data Security Manager is available in different form factors and FIPS 140-2 levels. Deploy virtual appliances on-premises, in private and public clouds or select high-assurance hardware with the data security management tool.
Centralize Key and Policy Management
Provision and manage encryption keys for all Vormetric Data Security platform products from Thales, as well as KMIP and other third-party encryption keys and digital certificates.
Flexible Deployment Form Factors
The Data Security Manager (DSM) is offered as a FIPS 140-2 Level 1 virtual appliance, as well as two hardware appliances: The V6000, which is FIPS 140-2 Level 2 certified, and the V6100, which is FIPS 140-2 Level 3 certified. The virtual appliance is available in VMware, HyperV, KVM, Amazon Web Services, and Azure compatible formats.
Unified Management and Administration
The DSM provides central management and secure storage of encryption keys, including those generated by Thales products, KMIP-compliant devices, Microsoft SQL Server TDE, Oracle TDE and IBM Guardium Data Encryption. The data security manager has an intuitive Web-based console, CLI, or APIs for managing encryption keys and policies.
Maximum Security and Reliability
To maximize uptime and security, the DSM features redundant components and the ability to cluster appliances for fault tolerance and high availability. Strong separation-of-duties policies can be enforced to ensure that one administrator does not have complete control over data security activities, encryption keys or administration. In addition, the DSM supports two-factor authentications for administrative access as well as remote HSM administration with smart card access for v6100 DSMs.
HSM integration for FIPS 140-2 Level 3 root of trust
Three DSM appliances are available: virtual, v6000 and v6100. V6100 DSMs are already equipped with an embedded FIPS 140-2 Level 3 HSM for a secure internal root of trust. For virtual and v6000 appliances, integration with external HSMs is available to provide this same capability.
Secure key import for data encryption keys
Import data encryption keys from external HSMs or other key sources using RESTful APIs or the DSM management console. These key import capabilities offer flexibility and give organizations more control of data security across cloud services, big data, container, and on-premises environments.
| Chassis | 1U rack-mountable; 17” wide x 20.5” long x1.75” high (43.18 cm x 52.07cm x 4.5 cm) |
| Weight | V6000: 21.5 lbs (9.8 kg); V6100: 22 lbs (10 kg) |
| Memory | 16GB |
| Hard Disk | Dual SAS RAID 1 configured with FIPS tamper-evident seals |
| Serial Port | 1 |
| Ethernet | 2x1Gb |
| IPMI | 1x10/100Mb |
| Power Supplies | 2 removable 80+certified (100VAC-240VAC/50-60Hz) 400W |
| Chassis Intrusion Detection | Yes. Also includes FIPS tamper-evident seal on the top cover. |
| Maximum BTU | 410 BTU max |
| Operating Temperature | 10° to 35° C (50° to 95° F) |
| Non-Operating Temperature | -40° to 70° C (-40° to 158° F) |
| Operating Relative Humidity | 8% to 90% (non-condensing) |
| Non-Operating Relative Humidity | 5% to 95% (non-condensing) |
| Safety Agency Approval | FCC, UL, BIS certifications |
| FIPS 140-2 Level 3 | V6100 model is equipped with an integrated HSM; FIP140-2 Level 3 root of trust available for V6100 & virtual DSMs with an external HSM integration |
| HSM Remote Administration | V6100 only; requires optional Remote Administration kit |
| Administrative Interfaces | Secure Web, CLI, SOAP, REST |
| Number of Management Domains | 1,000+ |
| API Support | PKCS #11, Microsoft Extensible Key Management (EKM), SOAP, REST |
| Security Authentication | Username/Password, RSA multi-factor authentication (optional) |
| Cluster Support | Yes |
| Backup | Manual and scheduled secure backups. M of N key restoration. |
| Network Management | SNMP, NTP, Syslog-TCP |
| Syslog Formats | CEF, LEEF, RFC 5424 |
| Certifications and Validations | FIPS 140-2 Level 1, FIPS 140-2 Level 2, FIPS 140-2 Level 3 Common Criteria (ESM PP PM V2.1) |
| Number of CPUs | 2 |
| RAM (GB) | 4 |
| Hard Disk (GB) | 100GB |
| Support Thin Provisioning | Yes |
