Assureurs
L’industrie des assurances gère le risque, et les brèches de données des compagnies d’assurance prouvent que la cybersécurité est l’un des risques juridiques et réglementaires majeurs. Cependant, les assureurs doivent également réduire le risque de brèches de données pour conserver leur clientèle, maintenir leur profitabilité et protéger les directeurs.
- Défis
- Solutions
- Avantages
Les données d’assurance sont une cible très prisée
Les compagnies d’assurance sont une cible très prisée pour les pirates. Selon le Pittsburgh Post Gazette :
« La valeur des dossiers financiers et de santé personnels est deux ou trois fois supérieure [à la valeur des informations financières seules] car les opportunités de fraude sont bien plus nombreuses », explique David Dimond, directeur de la technologie chez EMC Healthcare, un fournisseur de technologie basé dans le Massachusetts. Avec un numéro de sécurité sociale, une date de naissance et un historique de santé, un voleur peut ouvrir des comptes de crédit et facturer les assureurs ou le gouvernement pour des soins médicaux fictifs, ajoute-t-il.
Plusieurs vulnérabilités
Les vulnérabilités des données pour les assureurs comprennent :
- Les portails client
- Les transactions par carte de crédit
- Les menaces en interne
- Les pirates extérieurs (acquisition des identifiants)
- L’entreposage de Big Data et les applications
- Le stockage des données dans le Cloud
- Les employés utilisant des solutions de gestion du contenu
- Le besoin de consolider les opérations et les données (les acquisitions, par exemple)
Conformité
Les assureurs ont plusieurs besoins de conformité, dont :
- PCI DSS
- HIPAA-HITECH
- Lois sur les notifications par les États américains de vols de données
- Sarbanes-Oxley
- GLBA
- Résidence/souveraineté des données
- Autres normes et réglementations à venir
Menaces avancées et protection obsolète
Les compagnies d’assurance actuelles utilisent des solutions de sécurité obsolètes et disparates tandis que les cybercriminels les attaquent avec les armes informatiques les plus avancées. Les compagnies d’assurance doivent mettre à jour la sécurité de leurs données avec une solution au niveau de l’entreprise de sorte à ce qu’elle satisfasse les contraintes de conformité les plus complexes tout en offrant une sécurité véritable contre la brèche. Elles ont besoin d’une solution qui fonctionne :
- Avec des données de toute sorte
- Sur plusieurs systèmes d’exploitation
- Dans plusieurs environnements
- Avec des ressources humaines, des fonds, un matériel et des logiciels limités.
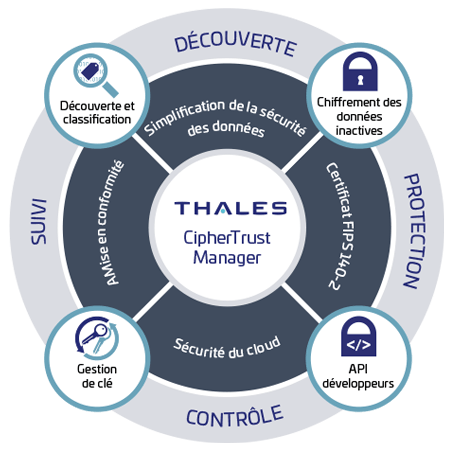
CipherTrust Data Security Platform
CipherTrust Data Security Platform est une infrastructure souple qui offre une gestion centralisée des clés et des politiques pour une suite de solutions de sécurité des données qui protège les données sensibles et réglementées de votre organisation, où qu’elles résident. Cela permet de garantir un coût total de possession faible ainsi qu’un déploiement et une exécution simples et efficaces.
CipherTrust Transparent Encryption
CipherTrust Transparent Encryption fournit un chiffrement des données au repos au niveau des fichiers ou des volumes, une gestion des clés et des contrôles d’accès sécurisés requis par les réglementations et les normes de conformité.
CipherTrust Security Intelligence
CipherTrust Security Intelligence fournit un autre niveau de protection contre les individus malveillants en interne, les utilisateurs privilégiés, les menaces persistantes avancées et autres attaques pouvant compromettre les données en fournissant les informations des comportements d’accès permettant d’identifier un incident en cours.
CipherTrust Application Data Protection
CipherTrust Application Data Protection permet aux entreprises d’intégrer des fonctionnalités de chiffrement à des applications internes au niveau du champ et de la colonne.
CipherTrust Key Management
CipherTrust Key Management permet une gestion centralisée des clés de chiffrement pour d’autres environnements et appareils, y compris le matériel compatible KMIP et les clés principales et les certificats numériques d’Oracle TDE et de SQL Server TDE.
CipherTrust Tokenization with Dynamic Masking
CipherTrust Tokenization with Dynamic Masking permet aux administrateurs d’établir des politiques pour renvoyer un champ entièrement tokénisé ou masquer dynamiquement des parties d’un champ. Grâce aux fonctionnalités de tokénisation avec conservation du format de la solution, les administrateurs peuvent limiter l’accès aux ressources sensibles tout en formattant en même temps les données protégées de sorte que les nombreux utilisateurs puissent faire leur travail.
Conformité
Les solutions de sécurité CipherTrust sont conçues pour vous aider à garantir votre conformité aux réglementations suivantes :
- Payment Card Industry Data Security Standard (PCI DSS)
- Lois sur les notifications par les États américains de brèches de données
- Lois de protection et de confidentialité des données nationales
- Sarbanes-Oxley, GLBA, Basel III
- Patriot Act américain
- Mandat du gouvernement fédéral américain pour le chiffrement
- Common Criteria
- Autres réglementations à venir
Installation rapide et facile, indépendamment de votre système d’exploitation
Thales peut collaborer avec vous pour installer les solutions CipherTrust Data Security en quelques semaines plutôt qu’en quelques mois. Les solutions de Thales sont compatibles avec la majorité des systèmes d’exploitation principaux, y compris les serveurs Linux, UNIX et Windows dans les environnements physiques, virtuels, Cloud et CDE (Cardholder Data Environments) de Big Data.
Facile à utiliser
CipherTrust Data Security de Thales permet de répondre aux préoccupations de sécurité et de conformité en toute simplicité en défendant simultanément les données dans les bases de données, les fichiers et les nœuds de Big Data sur les infrastructures Clouds publics, privés, hybrides et les infrastructures traditionnelles. La gestion centralisée d’une plateforme de sécurité des données dans son ensemble peut facilement s’étendre à la protection de la sécurité des données et respecter les exigences de conformité dans toute l’entreprise, augmentant ses capacités selon les besoins sans ajouter de matériel ou augmenter la charge opérationnelle.
Ne ralentit pas les performances du système
Les clients indiquent généralement ne subir aucun impact visible sur l’expérience de l’utilisateur final lorsqu’ils utilisent les solutions de Thales. CipherTrust Transparent Encryption réalise les opérations de chiffrement et de déchiffrement à l’endroit optimal dans le système de fichiers ou le gestionnaire de volumes, tirant parti des accélérateurs cryptographiques matériels, comme Intel® Advanced Encryption Standard-New Instructions (Intel® AES-NI) et SPARC Niagara Crypto, pour accélérer le chiffrement et le déchiffrement des données.
