What is Post-Quantum Cryptography?
Post-quantum cryptography (PQC) comprises algorithms and protocols designed to resist quantum computer attacks. They remain compatible with current computing systems and support the transition from quantum-vulnerable algorithms such as RSA, Elliptic Curve Cryptography (ECC), and Diffie-Hellman.
The Quantum Threat: Why preparation can’t wait
Today’s widely used public-key cryptographic systems and protocols, including RSA, ECC and Diffie-Hellman, rely on mathematical problems that are hard for classical computers to solve. Future quantum machines are expected to solve these problems much more efficiently, putting current algorithms and the systems that depend on them at risk. Because attackers can “harvest now, decrypt later,” long-lived data is already exposed.
Organizations should begin PQC migration now by identifying quantum-vulnerable cryptography, prioritizing high-risk and long-lived data, and preparing for hybrid environments using both classical and NIST-standardized PQC algorithms (ML-KEM, ML-DSA, SLH-DSA).
61 %
of organizations identify harvest now, decrypt later as the #1 quantum-related risk.
59 %
of organizations are prototyping and evaluating post-quantum cryptographic algorithms.
Everything You Need to Know About Cryptographic Inventories
Cryptographic Inventory: Deriving Value Today, Preparing for Tomorrow
The strategic principle of establishing a cryptographic inventory is key to addressing today’s vulnerabilities and preparing for a post-quantum world.

Building a Future-Proof Post-Quantum Strategy
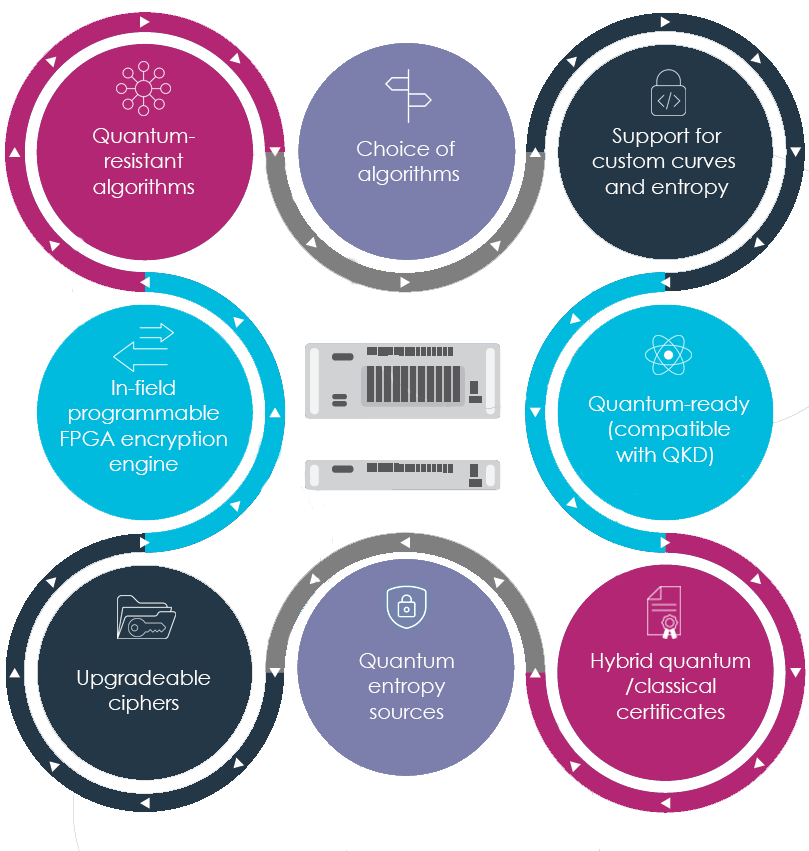
Securing an enterprise against quantum threats requires cybersecurity solutions that support Quantum Resistant Algorithms (QRA), and also offer options for Quantum Key Distribution (QKD) and Quantum Random Number Generation (QRNG). Thales is committed to delivering solutions that support a Post-Quantum crypto agile strategy.
Quantum Key Distribution
QKD distributes encryption keys between shared parties based on the principles of quantum physics and the properties of quantum mechanics
Quantum Resistant Algorithms
QRAs are fundamental to protecting against quantum attacks whether Lattice based, Multivariate, Hash based, or Code-based cryptography
Quantum Random Number Generation
QRNG is a high bit rate random number source harnessing the inherent randomness in quantum mechanics to create encryption keys
Post-Quantum Readiness Starts with Crypto-Agility
Crypto-agility is a business strategy that enables you to future-proof your organization by:
- Having the flexibility to quickly change protocols, keys, and algorithms
- Using flexible, upgradeable technology
- Reacting quickly to cryptographic threats, such as Quantum computing
- Adding to your tech stack with minimal to no disruption
Thales products have been purposely designed to help you be crypto-agile and Quantum-safe.
Post-quantum cryptography (PQC) modernizes quantum-vulnerable public-key cryptography such as RSA, ECC, Diffie-Hellman, and DSA with new algorithms designed to resist attacks from future quantum computers. Instead of relying on factorization or discrete logarithms, PQC uses different mathematical approaches that are intended to remain secure in a post-quantum world. NIST’s first finalized PQC standards are ML-KEM (FIPS 203), ML-DSA (FIPS 204), and SLH-DSA (FIPS 205).
PQC is mainly used to replace the public-key cryptography that protects TLS handshakes, PKI hierarchies, certificates, code signing, firmware signing, and machine identities. During migration, many organizations will use hybrid cryptography allowing classical and post-quantum algorithms to coexist to maintain interoperability during rollouts.
If your organization does not migrate to PQC, today’s public-key algorithms such as RSA and ECC will eventually become vulnerable to quantum attacks. This creates a “harvest now, decrypt later” (HNDL) risk, where encrypted data captured today can be decrypted in the future once cryptographically relevant quantum computers are available.
The risk is highest for long-lived systems and trust models, including PKI, root and intermediate certificate authorities, code signing, firmware signing, IoT, industrial control systems, and medical devices. Without a clear PQC migration strategy, organizations face long-term data exposure, broken trust chains, supply chain risk, and growing regulatory pressure.
Organizations need to start PQC migration now because the transition is already underway. NIST has finalized the first PQC standards, and its transition guidance is intended to help industry and government move away from quantum-vulnerable cryptography. NSA’s CNSA 2.0 guidance also gives organizations a clear signal to plan, budget, and prepare now rather than wait.
The bigger issue is time; PQC migration is not a simple algorithm swap. Certificates, firmware, applications, embedded systems, and cryptographic dependencies often live for years. Waiting too long compresses testing, rollout, vendor coordination, and compliance into a much riskier and more expensive project.
Start by identifying where quantum-vulnerable cryptography is used across applications, infrastructure, certificates, APIs, firmware, networks, and machine identities. Then prioritize high-risk assets such as long-lived sensitive data, external-facing systems, trust anchors, and signing environments. NIST’s migration guidance is specifically meant to inform timelines and transition planning for products, services, and infrastructure.
Next, build a crypto-agile migration plan. Most organizations will need phased, hybrid deployments so classical and PQC algorithms can coexist during the transition. Strong key management, certificate lifecycle management, governance, and testing are essential to make cryptographic change manageable over time.
Supporting PQC requires both new algorithms and modern cryptographic infrastructure. At a minimum, organizations should evaluate support for ML-KEM (FIPS 203), ML-DSA (FIPS 204), and SLH-DSA (FIPS 205), as well as hybrid cryptographic operations for transitional environments.
Hardware Security Modules (HSMs), key management systems, PKI platforms, certificate lifecycle tools, and cryptographic APIs all play a role. HSMs are especially important because they secure key generation, storage, and signing operations, and PQC-ready platforms increasingly need support for hybrid keys and certificates, crypto agility, and the new NIST algorithms.
Network encryption can also play an important role in PQC readiness, especially for protecting long-lived or high-value data in motion during multi-year migrations. High Speed Encryptors (HSE) help reduce exposure to “harvest now, decrypt later” risk on critical network links and backbones, and can provide a crypto-agile foundation that supports evolving standards and profiles over time. In some environments, organizations may also integrate complementary technologies such as quantum key distribution (QKD) or high-quality entropy sources (e.g., QRNG) alongside standards-based PQC approaches.
Preparing Your Organization for a Quantum Future
As quantum computing advances, the cryptographic algorithms protecting today’s systems will eventually become vulnerable. Preparing now means understanding where cryptography is applied throughout your systems, identifying long‑lived risks, and establishing a clear roadmap for transitioning to quantum‑safe protection.
There are three component parts of a quantum safe solution, which we’ve done in our work with Wells Fargo to take some risks off the table. It starts at the key generation stage: How do you create the keys that you're using in your system? What type of keys are they? Then there is the algorithms and how do you look after them? That's the management aspect. Finally on the generation front, we are looking to produce keys that are fundamentally unpredictable. These three items are the definition for a strong key.

Thales Quantum-Ready Solutions

Rely on Luna HSMs as the market-leading crypto agile foundation of digital trust to reduce risk, ensure flexibility, easily manage keys, and simplify integrations.
Protect Encryption Keys with Luna Hardware Security Modules
Luna HSMs help enable quantum-safe cryptographic workflows by incorporating NIST-standardized PQC algorithms, including ML-KEM (FIPS 203), ML-DSA (FIPS 204), and SLH-DSA (FIPS 205), directly into core firmware to protect keys and support post-quantum use cases.
Remain crypto agile with the capability to implement and evaluate emerging PQC algorithms as they become available and leverage an extensive ecosystem of PQC-ready Luna HSM partner integrations.
Inject quantum entropy with QRNG and Luna HSM’s secure key storage
Address critical applications where high-quality random numbers are vital
Secure Data in Transit with High Speed Encryptors (HSE)
Built on field-upgradable FPGAs, Thales High Speed Encryptors (HSEs) deliver crypto-agility for the PQC transition. They support ML-KEM (FIPS 203), ML-DSA (FIPS 204), and SLH-DSA (FIPS 205), alongside sovereign algorithms. Hybrid, in-field upgradable configurations strengthen key exchange and authentication while maintaining compatibility with existing infrastructure as standards and requirements evolve.
HSEs are integrated with Quantum Key Distribution (QKD) devices for ultra-secure key delivery over optical links, future-proofing backbone data transport against quantum-enabled interception. In addition, HSEs can incorporate Quantum Random Number Generation (QRNG) for high-entropy symmetric key derivation.
Transport Independent Mode (TIM) eliminates the need for public key exchange by enabling symmetric keys to be independently derived using out of band authenticated policy and approved key derivation methods. This prevents exposure of key material in transit, mitigates Harvest Now, Decrypt Later (HNDL) threats and supports long-term quantum resilience.

Thales HSEs deliver crypto-agile network encryption with a flexible FPGA-based architecture, enabling seamless migration to post-quantum security.
Kick-start your Post-Quantum Readiness
Test your applications, cryptographic workflows, and critical data flows across the network in a PQC-ready environment to assess impact, validate interoperability, and plan your migration.