Ameaças persistentes avançadas (APTs)
Uma ameaça persistente avançada (APT) é um ataque cibernético sofisticado geralmente realizado por países ou por criminosos cibernéticos avançados que obtêm acesso não autorizado a sistemas/rede de computadores e permanecem sem serem detectados por um longo período de tempo. Esses ataques não são ideias repentinas. Eles são planejados deliberadamente por muito tempo, com objetivos específicos em mente.
As violações de dados continuam a ocorrer, apesar de todas as defesas de segurança de perímetro e endpoint que as empresas implantam para detectar e bloquear APTs sofisticadas. Estas medidas de proteção não têm sido suficientes para impedir que criminosos cibernéticos sofisticados roubem dados confidenciais. As empresas perceberam que proteger dados confidencias através de controles de acesso, criptografia e tokenização é a melhor linha de defesa para evitar a exposição de dados e reduzir riscos comerciais em geral.
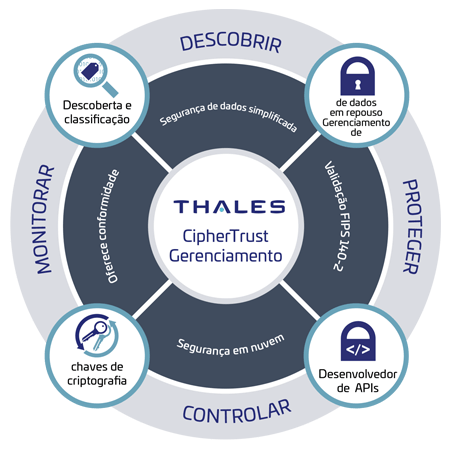
A CipherTrust Data Security Platform da Thales podem permite que as empresas protejam dados críticos e confidenciais de APTs. A CipherTrust Platform permite às empresas descobrir, proteger e controlar seus dados confidenciais com uma proteção de dados unificada e de última geração. Ela acaba com a complexidade da segurança dos dados, acelera o tempo de conformidade e protege a migração da nuvem, o que resulta em menos recursos dedicados às operações de segurança de dados, controles de conformidade onipresentes e redução significativa dos riscos em toda a sua empresa.
- Desafios
- Soluções
- Vantagens
As ameaças persistentes avançadas são ataques altamente sofisticados e personalizados, projetados para contornar o perímetro da rede tradicional e as medidas de segurança de endpoint usadas pelas empresas. Elas são difíceis de detectar e proteger quando são das maneiras a seguir.
- Sistemas Bypass baseados em assinatura: as soluções antivírus tradicionais são ineficazes na detecção e bloqueio de APTs, pois dependem de assinaturas que utilizam técnicas de correspondência de padrões. Já as APTs são de natureza polimórfica e frequentemente mudam características de identificação como nomes de arquivos, tamanho de arquivos e criptografia para tornar o malware irreconhecível.
- Geração de atividade inusitada de usuários: as APTs geram atividades incomuns de usuários, como o aumento de logins tarde da noite usando credenciais comprometidas, ou grande quantidade de fluxos de dados de sistemas internos para servidores externos de comando e controle operados por criminosos cibernéticos para roubar dados. Muito poucas soluções de segurança rastreiam as mudanças de comportamento dos usuários que levam a violações de dados.
- Vetores novos de ameaças por adoção da nuvem: a crescente adoção de infraestruturas híbridas de nuvem introduz uma série de vetores de ameaça, onde os controles de segurança atuais de uma empresa não se integram. Isso introduz falhas de segurança como a Shadow IT, onde aplicativos não autorizados de software como serviço (SaaS) são utilizados por linhas de negócios que colocam em risco dados confidenciais corporativos.
As empresas notaram que investir em uma segurança de dados abrangente é a melhor forma de defesa contra APTs. Com uma solução robusta de segurança de dados, que inclui descoberta e proteção de dados, controle de acesso de granulação fina e solução centralizada de gerenciamento de chaves, qualquer empresa pode criptografar/tokenizar dados confidenciais como informações pessoais identificáveis (PII), informações pessoais de saúde (PHI) e dados financeiros (números de cartão de crédito, números de conta). Desta maneira, esses dados são tornados ilegíveis e não têm valor para o criminoso cibernético.
A CipherTrust Data Security Platform unifica a descoberta, classificação e proteção de dados e tem controles de acesso granulares sem precedentes com gerenciamento centralizado de chaves - tudo em uma única plataforma.
- Descoberta e classificação de dados: a descoberta e a classificação de seus dados confidenciais é o primeiro passo crítico neste processo. Saber onde residem os dados confidenciais de sua empresa residem e que tipo de risco eles representam em relação à privacidade e conformidade dos dados é um primeiro passo importante.
- Proteção de dados confidenciais: a implementação de formas apropriadas de controles de acesso e políticas de criptografia ou tokenização para ocultar dados impede que dados confidenciais sejam expostos a usuários não autorizados ou a criminosos cibernéticos avançados.
- Controle de chaves criptográficas: qualquer solução criptográfica robusta depende da segurança das chaves criptográficas usadas para criptografar dados. À medida que as empresas implantam um número cada vez maior de repositórios de dados em silo, elas precisam ser capazes de gerenciar políticas de segurança em silo de dados diferentes com gerenciamento centralizado do ciclo de vida das chaves e controle de acesso finamente granulado para chaves e dados.
A CipherTrust Data Security Platform oferece às empresas as seguintes vantagens para defesa contra APTs.
• Segurança de dados simplificada: descubra, proteja e controle dados confidenciais em qualquer lugar com nossa proteção de dados unificada de última geração. A CipherTrust Data Security Platform simplifica a administração da segurança de dados com um console de gerenciamento centralizado de "painel único" que equipa as empresas com ferramentas poderosas para descobrir e classificar dados confidenciais, combater ameaças persistentes avançadas, proteger contra abuso de informações privilegiadas e estabelecer controles persistentes, mesmo quando os dados são armazenados em nuvem ou em uma infraestrutura de um provedor externo. As empresas podem facilmente descobrir e resolver problemas de privacidade, priorizar a proteção e tomar decisões informadas sobre mandatos de privacidade e segurança antes de realizar uma transformação digital.
• Conformidade mais rápida: órgãos reguladores e de auditoria exigem que as empresas tenham controle de dados confidencias regulamentados e relatórios para provar isso. Recursos da CipherTrust Data Security Platform como descoberta e classificação de dados, criptografia, controle de acesso, registros de auditoria, tokenização e gerenciamento de chaves suportam os requisitos onipresentes de segurança e privacidade de dados. Esses controles podem ser rapidamente adicionados a novas implantações ou em resposta à evolução dos requisitos de conformidade. A natureza centralizada e extensível da plataforma permite que novos controles sejam acrescentados rapidamente através da adição de licenças e da implementação dos conectores necessários em resposta a novos requisitos de proteção de dados.
• Migração segura para a nuvem: a plataforma oferece soluções avançadas de criptografia e gerenciamento centralizado de chaves que permitem às empresas armazenar com segurança dados confidenciais na nuvem. A plataforma oferece soluções avançadas de criptografia de nuvens múltiplas com a tecnologia Bring Your Own Encryption (BYOE) para evitar o bloqueio de criptografia por provedores de nuvens e garantir a mobilidade dos dados para ter uma segurança eficiente em vários provedores de nuvem com gerenciamento centralizado e independente de chaves de criptografia. As empresas que não podem ter sua própria criptografia ainda podem seguir as melhores práticas do setor gerenciando chaves externamente usando o CipherTrust Cloud Key Manager. O CipherTrust Cloud Key Manager suporta casos de uso da tecnologia Bring Your Own Key (BYOK) em múltiplas infraestruturas de nuvem e aplicativos SaaS.
