Protezione di file non strutturati
Da qualche anno il volume di dati non strutturati all’interno delle aziende è in crescita esponenziale. La quantità di dati archiviati in cartelle condivise, dispositivi, portali per la collaborazione, caselle di posta e piattaforme cloud è in aumento, ma mettere in sicurezza questi dati strutturati è difficile. Per proteggere adeguatamente i dati strutturati occorre sapere dove si trovano.
Per stabilire una protezione assoluta, le squadre IT hanno bisogno di una soluzione centralizzata di data discovery e protezione dei dati in grado di identificare e mettere in sicurezza i dati sensibili ovunque si trovino. È per questo che molte aziende si affidano a CipherTrust Data Discovery and Classification e CipherTrust Transparent Encryption per scoprire, classificare e proteggere file non strutturati.
- Sfide
- Soluzioni
- Vantaggi
Determinazione della posizione dei dati sensibili non strutturati.
Prima di poter impedire che i dati vengano compromessi, estratti o distrutti, e prima di potersi allineare agli svariati requisiti legati a privacy e sicurezza, occorre sapere quali dati sensibili si possiedono, dove si trovano e in quale contesto. I sistemi distribuiti e i compartimenti isolati di dati rendono difficile l’individuazione e la classificazione di dati non strutturati. Individuare e classificare i dati in base a sensibilità, rischio, conformità o altre categorie è un passo fondamentale per proteggerli.
Protezione di file non strutturati
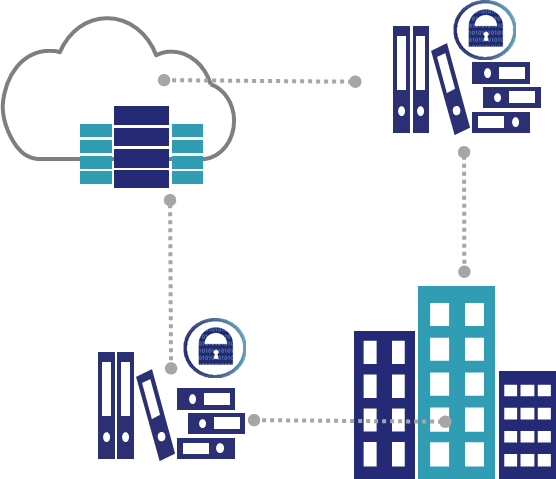
I file non strutturati rappresentano una sfida unica per le squadre IT, poiché contengono spesso dati sensibili che hanno bisogno della stessa protezione di quelli presenti in database strutturati. Questi file possono trovarsi in svariati database a seconda delle necessità aziendali.
Individuazione di chi deve avere accesso ai dati non strutturati
I dati non strutturati che sono distribuiti in tutta l’azienda, suddivisi in scomparti di archiviazione isolati e controllati da diversi sistemi di controllo degli accessi rendono difficile determinare gli utenti e i gruppi che possono accedere ai dati sensibili. Un controllo degli accessi decentrato non consente di implementare criteri di sicurezza uniformi e coerenti che controllino gli accessi a dati non strutturati.
CipherTrust Data Discovery and Classification
Tra le sfide più importanti che gli architetti della sicurezza e i professionisti IT devono affrontare vi è l’individuazione della posizione dei dati sensibili, del loro formato e di ciò che li rende sensibili. Essere in grado di accedere a tutti i data store nell’azienda e identificare e classificare i dati sensibili a seconda del tipo e del rischio ti permette di pianificare la protezione più adeguata.
CipherTrust Data Discovery and Classification di Thales permette alla tua azienda di ottenere visibilità completa sui dati sensibili grazie a discovery, classificazione e analisi dei rischi efficienti in cloud, big data e ambienti tradizionali.
CipherTrust Transparent Encryption
Con CipherTrust Transparent Encryption, la tua azienda può proteggere dati non strutturati ovunque si trovino, internamente o nel cloud. Il sistema di crittografia dei file ti permette di proteggere i dati sensibili in fogli di calcolo, documenti, presentazioni, immagini e molto altro. Al contrario di altre soluzioni di crittografia dei file, CipherTrust Transparent Encryption permette alle squadre incaricate della sicurezza di implementare una crittografia a livello di file senza dover apportare cambiamenti alle applicazioni, infrastrutture o pratiche commerciali dell’azienda. Inoltre, i controlli degli accessi e le registrazioni del controllo degli accessi ai dati sono disponibili senza dover modificare applicazioni, infrastrutture o flussi di lavoro: ne risulta il massimo controllo con costi e risorse minimi.
CipherTrust Data Discovery and Classification
CipherTrust Data Discovery and Classification semplifica l’individuazione e la classificazione di dati sensibili nell’azienda localizzando con efficacia i dati sensibili strutturati e non in cloud, big data e data store tradizionali. Classifica i dati sensibili per formato, livello di rischio, requisito di conformità (ad es. GDPR, CI DSS, ecc.) e altro, facilitando la determinazione e l’applicazione della forma più adeguata di risanamento.
CipherTrust Transparent Encryption
Controlli persistenti e granulari
La protezione crittografica a livello di file di CipherTrust Transparent Encryption non si limita alla crittografia. L’agente di crittografia dei file continua a registrare gli accessi e ad applicare criteri di controllo granulare degli stessi per impedire accessi non autorizzati da parte di utenti e processi. È possibile applicare i criteri a seconda dell’utente, del processo, del tipo di file, dell’ora del giorno e di altri parametri. Grazie a queste funzionalità, le squadre incaricate della sicurezza possono garantire una protezione e un controllo continuo dei dati strutturati e non dell’azienda.
Ampio supporto all’ambiente
CipherTrust Transparent Encryption protegge i dati strutturati e i file non strutturati in data center, cloud, container e ambienti big data su Linux, Windows e AIX con un’unica infrastruttura e un solo ambiente di gestione. La soluzione può proteggere i dati sensibili in database come IBM DB2, Oracle, Microsoft SQL Server, MySQL, NoSQL e Sybase.
Separazione di utenti privilegiati e dati sensibili degli utenti
Il sistema di crittografia dei file permette alle organizzazioni di creare una separazione completa delle responsabilità tra gli amministratori privilegiati e i titolari dei dati. CipherTrust Transparent Encryption crittografa i file lasciando liberi i loro metadati. In questo modo le squadre IT (inclusi gli amministratori di hypervisor, cloud, archivi e server) possono eseguire le proprie attività di amministrazione del sistema senza ottenere l’accesso ai dati sensibili che si trovano nei sistemi che gestiscono.