 In testimony to the US Congress this week, Director of National Intelligence James Clapper highlighted the threat of foreign agents penetrating US computer networks to steal secrets. His commentary highlighted state actors (suggestion: read the Mandiant report), hactivists, and cybercriminals as being at the top of his list of potential threats.
In testimony to the US Congress this week, Director of National Intelligence James Clapper highlighted the threat of foreign agents penetrating US computer networks to steal secrets. His commentary highlighted state actors (suggestion: read the Mandiant report), hactivists, and cybercriminals as being at the top of his list of potential threats.
No matter where in the world your enterprise or government is located, such external and internal threats put your sensitive data at increasing risk. It could be cardholder information, personally identifiable information (PII), intellectual property (IP), or employee personal health information. All such data has value to bad guys and when they succeed in getting it, the situation becomes extremely costly to the organization involved, both financially and from a brand reputation standpoint.
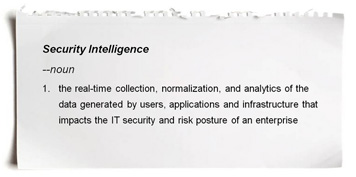
The best tools for combating these attacks are the threat and security intelligence capabilities found in Security Information and Event Management (SIEM) solutions. SIEM tools can monitor real-time events as well as consume the mountains of long-term data to find anomalous patterns of usage, evaluate possible threats to reduce false positives, and alert organizations to potential threats. Typical Vormetric Data Security deployments use SIEM tools by feeding log data from the Vormetric Data Security platform into those solutions. This gives our customers near real-time security intelligence about exactly who is accessing what information on which server so that they can take appropriate actions against both internal (privileged user exploitation) and external (APT) threats.
The best strategy to lower your risk profile involves taking a data-centric approach to security; you must be in the data path, have strong policies in place, and be able to quickly gather rich security intelligence so that you can get ahead of the bad guys and thwart their attack plans. Flying under the radar is no longer an option. Make sure you protect what matters.
Todd Thiemann is Vormetric’s senior director of product marketing. Follow him on Twitter @CrypTodd.

 Tina Stewart | VP, Global Market Strategy
Tina Stewart | VP, Global Market Strategy