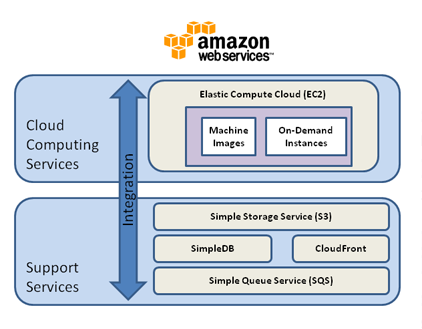
Recently reported in an Infoworld article was the fact that one in six Amazon S3 buckets have been left open for public access. S3 buckets (S3 stands for Simple Storage Service), for those of you who don’t regularly use Amazon Web Services infrastructure, are designed to store and serve static content for users of the Amazon cloud.
So what was in those 1, 951 buckets set to “public”? Sales records, account information, employee personally identifiable information (PII), database backups and passwords, source code, usernames/passwords, sales battle cards and more.
Why were they left “public” with confidential, protected data out in the open? Amazon even makes it clear that leaving access set to “public” results in insecure storage of your data. And their default is “private”. The fact is, that without security and policy infrastructure that extends to cloud implementations, people will make mistakes, and take shortcuts. In this case, resulting in a large amount of sensitive, compromised information.
The reality is, if you are using cloud resources, the liability for a data breach or for lack of regulatory compliance is up to you. No matter what the guarantees or service level commitments of your cloud provider.
For the organizations involved in this incident, making their S3 objects “private”, and using the Amazon specific encryption and access controls available with S3 would have avoided this exposure. However, to ensure a secure solution to using data within the cloud, this would just have been a starting point.
What’s really needed to move significant infrastructure into a public cloud IaaS environment is data-centric security.
What does that mean?
Put the protection for your data with your data. Recent exploits, as outlined in the Mandiant report come from advanced persistent threats (APTs). These types of exploits work their way past and through internal firewalls, network protections and AV implementations, and remain unobserved for months to years before discovery (usually by a third party). Even a virtual private cloud isn’t proof against these methods.
Cloud and virtual private cloud implementations have the added security risk of cloud administrators who may have access to your instances. Encryption, access controls and access logging at the system/instance level are required, but with centralized administration and management tied to your enterprise infrastructure.
Use strong encryption and key management. Encryption may be free, but management of that encryption to support enterprise needs is not. Cloud data protection implementations need the same recoverability, availability, key management and centralized control linked to your enterprise’s groups and users as you’d find in an on-premise only solution.
Protect data with access controls. Access controls should be flexible enough to allow the right combination of user and process access to protected data, while logging access attempts and preventing entree by un-authorized users and processes. This is what protects data in your cloud implementations from cloud administrators, your system administrators and others who need to only manage instances, not see data – while allowing your applications the usage they need for operation.
Security intelligence. These access controls should also provide the information you need to identify advanced persistent threats, malicious insiders and cloud administrators attempting access to protected data. Logs should be compatible with SIEM solutions that can analyze the data and help identify when an attack is underway.
Make sure the protection is transparent. If you need to redo a business process, re-write an application or change how users work, you have the wrong solution. Data protection in the cloud should allow what you have now to keep working.
Protect your cloud data with your local enterprise data. Your solution should use a single framework and management infrastructure to protect the data within both your local enterprise and cloud IaaS implementations. Multiple solutions and infrastructure sets will reduce the economic benefits you invested in cloud solutions to enable.
And “Yes” … If you are looking for a solution to these problems, Vormetric has it. We’ll protect what matters — your data within your enterprise, your cloud implementations, big data environments — anywhere that your critical information resides.
Andy Kicklighter is Vormetric’s director of product marketing. Follow him on Twitter @akicklighter.

 Andy Kicklighter | Director of Product Marketing
Andy Kicklighter | Director of Product Marketing