 We just released this week the summary of findings for U.S. financial services and retail (find the research briefs about half way down the linked page) respondents to the survey used for our 2015 Insider Threat Report. Research was performed by Nielsen and included responses from 102 IT decision makers in each category.
We just released this week the summary of findings for U.S. financial services and retail (find the research briefs about half way down the linked page) respondents to the survey used for our 2015 Insider Threat Report. Research was performed by Nielsen and included responses from 102 IT decision makers in each category.
We learned some pretty surprising things as a result. The first came as a result of the question “Has your organization experienced a data breach or failed a compliance audit in the last year?”
<ClickToTweet>: 3 Surprising Insider Threat results for Financial & Retail @akicklighter #DefenderOfData http://bit.ly/1E0Anos
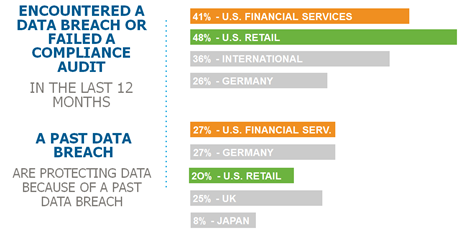 The surprise was in the sheer number of organizations that had experienced a data breach or failed a compliance audit in the last year – 48% for Retail and 41% for Financial Services. We’ve seen many high-profile retail and financial organizations reporting that their security has been breached, including data theft by employees and the compromise of insider credentials – but this documents that nearly half have been failing to protect their data in serious ways.
The surprise was in the sheer number of organizations that had experienced a data breach or failed a compliance audit in the last year – 48% for Retail and 41% for Financial Services. We’ve seen many high-profile retail and financial organizations reporting that their security has been breached, including data theft by employees and the compromise of insider credentials – but this documents that nearly half have been failing to protect their data in serious ways.
- Retail – 48%
- Financial – 44%
- Global: Over 40% experienced a data breach or failed a compliance audit
- US: 44%
Along with this – the total rate of past data breaches for financial services – typically among the best at protecting their data assets) was also a surprise – 27%, the highest rate of any category measured.
The second item was the dramatic change in the priorities for IT Security spending over the last two years for compliance and data breach prevention. The question asked was “Rank highest to lowest in terms of the impact on your organization’s decisions for IT security spending (1-5)”.
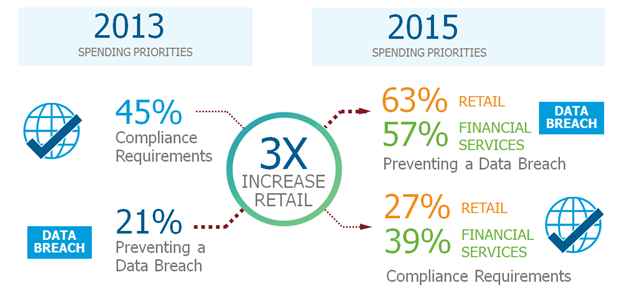 Versus our results from 3 years ago there’s a dramatic change – for retailers the rate is 3X greater than our overall rate from 2013 (63% vs. 21%), and financial services just a shade less (57%).
Versus our results from 3 years ago there’s a dramatic change – for retailers the rate is 3X greater than our overall rate from 2013 (63% vs. 21%), and financial services just a shade less (57%).
This year, preventing data breaches, contractual requirements, and protecting intellectual property all scored better than in previous surveys and significantly “achieving compliance” now drops down the priority list. The reasons why are clear. The last 12 months have seen a continuous flow of high-profile organizations reporting that their security has been breached, including data theft by employees and via compromised insider credentials.
Last these are the organizations that I’d most expect to have a plan about how to prevent these types of breaches and compliance problems. In my mind I’d expected these organizations to be ahead of the curve in what they need to do - The continuous drumbeat of news, and especially for financial services, the priority to protect customer and corporate assets seem strong reasons for them to fully understand the problem set and grapple with how to protect against the threats.
I was wrong. We asked two questions with identical category selections around the effectiveness of defenses and spending plans:
- In your opinion, how effective are each of the following defenses in protecting sensitive data-at-rest from insider threats?
- Twelve months from now, how will your organization’s spending to offset threats to data compare to its current level?
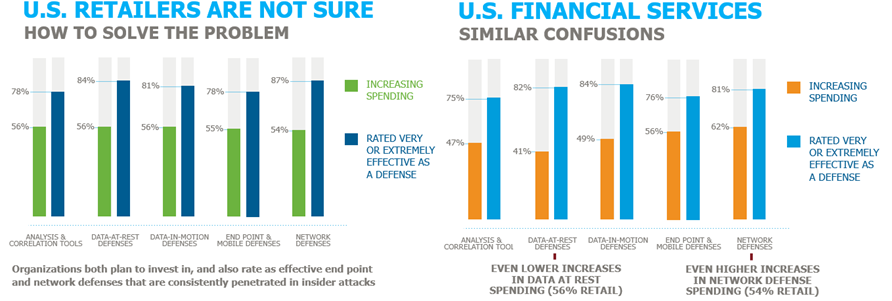 But what we found was that organizations really appear to not understand what security controls will help them most to offset these threats.
But what we found was that organizations really appear to not understand what security controls will help them most to offset these threats.
- Retail plans to both rate as effective, and plan to invest in, end point (55%) and network defenses (54%) that are consistently penetrated in insider attacks. Further – they were investing evenly in all categories of defenses, rather than shifting investment to data related defenses that are most effective.
- Financial Services had similar confusions – investing most heavily in network (62%) and end point ( 56%) defenses that have consistently failed – and investing at the lowest rates in data at rest protection (41%). This even though it was rated as one of the two most effective defenses
It’s time for retailers and financial services firms to take a good hard look at their IT Security investments to protection from insider related risks – The addition to the mix of stronger data security controls is required.
Here’s what I mean by that. At both the OS and application levels:
- Data protection techniques that make sensitive data inaccessible (encryption, tokenization, data masking)
- Access control to that ensures “need to know” access to that data
- Monitoring of the access patterns for those with a “need to know”
The combination of these techniques cuts down on the attack surface available once an insider “goes rogue” or when an account is “compromised” by an outside attack, and provides the visibility that highlights anomalous data access patterns that indicate an attack is in progress – so that it can be shut down before significant data is compromised.

 Andy Kicklighter | Director of Product Marketing
Andy Kicklighter | Director of Product Marketing