 Hello, IT decision maker. It’s likely your enterprise is experiencing some pain points with its data security strategy. From meeting compliance standards to scheduled windows of maintenance, juggling priorities in IT security operations can be both costly and disruptive.
Hello, IT decision maker. It’s likely your enterprise is experiencing some pain points with its data security strategy. From meeting compliance standards to scheduled windows of maintenance, juggling priorities in IT security operations can be both costly and disruptive.
On average, businesses lose between $84,000 and $108,000 for every hour of IT system downtime. While these numbers seem immense, the true cost of system outages go beyond monetary figures. System outages hinder employee productivity, impact brand reputation and can lead to revenue loss.
ClickToTweet: Now #Encrypt without taking down Critical Apps! @Vormetric bit.ly/20OX3nY pic.twitter.com/HaK2UH7RrV
When it comes to securing personal information, data can fall victim to downtime, especially when deploying tools like encryption. According to our recent Data Threat Report, across nearly all geographies, “complexity” was the number-one barrier to adopting data security tools and techniques more widely. While encrypting data is becoming more popular with organizations, challenges still remain on how to protect it.
Don’t worry, we have your back: encryption deployment is about to get much easier.
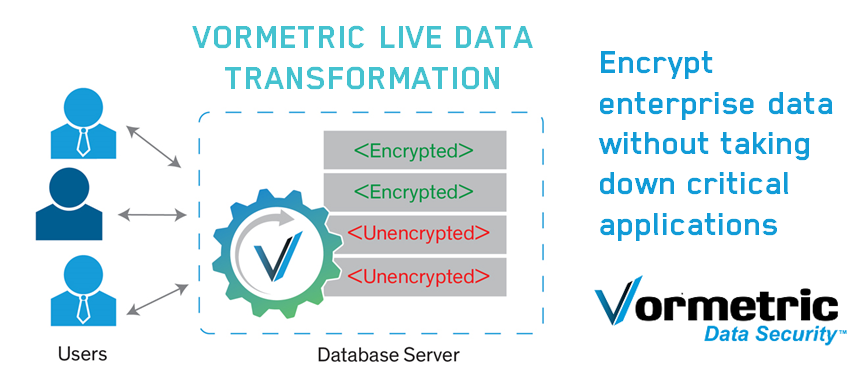
Today, we’re excited to announce new products for The Vormetric Data Security Platform, including Live Data Transformation, a patented solution that streamlines the process of encryption deployment for enterprises. The new features help organizations drive security initiatives, ensuring maximum compliance and flexibility without getting in the way of business operations.
Leveraging format-preserving encryption, the solution eliminates unnecessary downtime. Here’s the 411 on Live Data Transformation:
- Transparent encryption deployment: Seamlessly migrate data from clear-text to an encrypted state while the data is in use, without any disruption to users, applications or business workflows.
- Online key-rotation: Meet compliance practices that mandate periodic changes to data encryption keys. With Vormetric Live Data Transformation, applications remain online during the data encryption rekey process.
- Intelligent CPU management: To ensure the data transformation process does not impact production applications, encryption and rekey operations are scheduled to use less CPU resources during hours when the data is heavily used and more CPU resources during low data processing hours.
In addition to Live Data Transformation, we also announced expanded platform capabilities, offering customers more options than ever. Vormetric now offers Vaultless Tokenization and compatibility in Caringo environments for users of The Vormetric Cloud Encryption Gateway.
Vaultless Tokenization
Adrian Lane, analyst at Securosis, describes the benefits of tokenization as follows: “Technologies like tokenization reduce compliance scope by replacing sensitive data with a non-sensitive token that looks and acts like the original.”
In order to meet stringent industry requirements like PCI DSS, Vormetric Vaultless Tokenization provides all of the same benefits of our tokenization offering, but without the requirement for a token vault. This effectively reduces deployment and maintenance overhead, while enhancing performance.
Cloud Encryption Gateway
As mentioned in my recent blog post, enterprises can take control of their data by protecting it before it enters a cloud storage solution (Amazon S3, Box, etc.). Vormetric’s Cloud Encryption Gateway provides encryption, key management and access controls for data in cloud storage environments.
Through the Cloud Encryption Gateway, Vormetric now offers even more “security blades” which secure sensitive data residing in Amazon Web Services (AWS) Simple Storage Service (S3), Box and now also in Caringo environments.
More Information
For more details on the announcement see the press release here – and our web page here.
Interested in chatting with Vormetric or hearing more? Tweet to me @tumulak.
Love your data? We do too. You can also follow @Vormetric online using the hashtag, #DataFirst.
