 For IT Security pros in Healthcare, it's a tough job right now. Not only do they have some of the strictest compliance requirements imposed as a minimum entry level for doing business, restrictive budgets and some of most valuable data on the planet to protect (Healthcare data is worth much more on the dark web than credit card data), they also have organizations that have trouble prioritizing the need to protect information - Whose priority has always been the physical well-being of their patents.
For IT Security pros in Healthcare, it's a tough job right now. Not only do they have some of the strictest compliance requirements imposed as a minimum entry level for doing business, restrictive budgets and some of most valuable data on the planet to protect (Healthcare data is worth much more on the dark web than credit card data), they also have organizations that have trouble prioritizing the need to protect information - Whose priority has always been the physical well-being of their patents.
Click To Tweet: Healthcare IT Security pros really feel the heat bit.ly/1ZyHvzA pic.twitter.com/14re25tE8o
What we learned in the survey that led to the Healthcare Edition of the 2016 Vormetric Data Threat Report, is that there are some real misunderstandings about what to do to protect their organizations and patients.
 The first problem is thinking being compliant will stop data breaches
The first problem is thinking being compliant will stop data breaches
Agreed, with meeting compliance requirements minimum table stakes in the game, healthcare organizations have to meet them. And in fact Healthcare organizations had Compliance as the top IT Security spending priority. The problem is that (in the words of 451 analyst Garrett Bekker)
- "... being compliant does not mean you won't be breached"
- And "Compliance does not ensure security"
The problem was that 69% of Healthcare IT Security professionals thought that being compliant was very or extremely effective at preventing data breaches. It's a good baseline, but it won't stop the pain.
 The next problem? Investing in the wrong defenses to stop data theft
The next problem? Investing in the wrong defenses to stop data theft
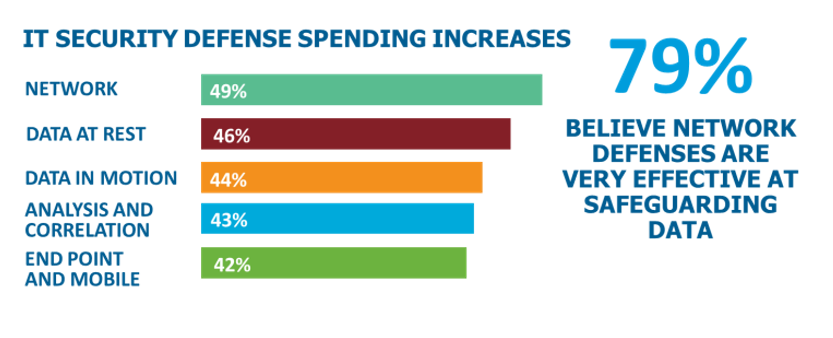
Lots of investment is going into network and end point protection, but with almost every analyst on the planet saying that “It isn’t if your defenses will be breached, it’s when” they should be looking harder at what it will take to protect critical information once the invaders are inside of the walls. It’s not that we don’t need network and end point defenses, but the priorities should shift to include data security. Sure, network defenses implemented correctly can help stop the pain, but they are no longer 100% effective.
What seems strange? How little concern there was about IoT data
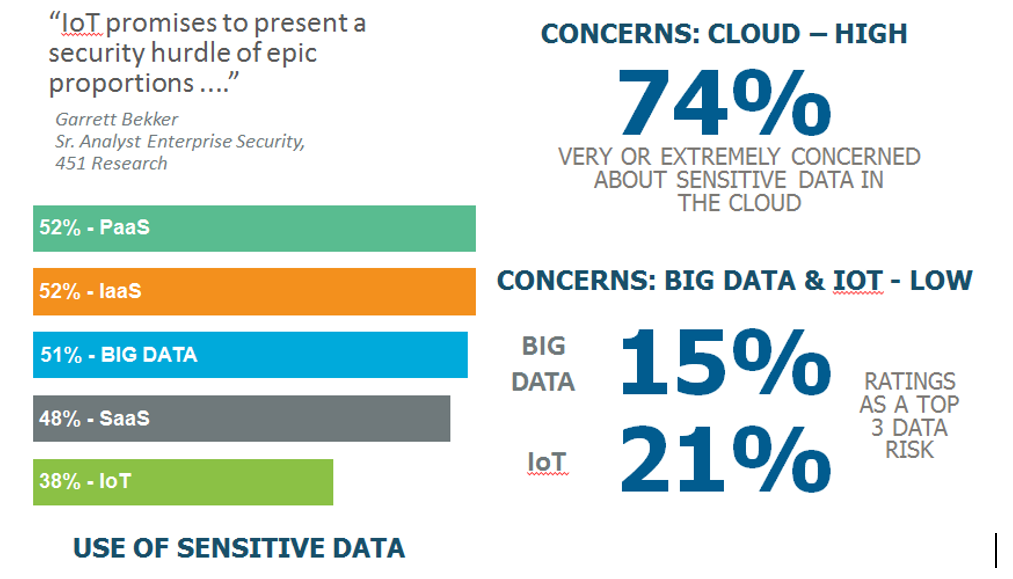 More than other verticals, Healthcare has a strong interest in IoT – medical devices for outpatient monitoring, as well as wellness/fitness monitoring are expanding exponentially – but there seems a low level of awareness of the risks of the data these devices collect. Only 21% thought that IoT data security concerns were high, and only 15% thought that the analysis environments most used on the back end were risky for data. Even more strange, only 38% thought that they'd have sensitive data within IoT .... when almost all the information is tied to patients and their medical status.
More than other verticals, Healthcare has a strong interest in IoT – medical devices for outpatient monitoring, as well as wellness/fitness monitoring are expanding exponentially – but there seems a low level of awareness of the risks of the data these devices collect. Only 21% thought that IoT data security concerns were high, and only 15% thought that the analysis environments most used on the back end were risky for data. Even more strange, only 38% thought that they'd have sensitive data within IoT .... when almost all the information is tied to patients and their medical status.
A surprise - Funding was not the reason they weren't implementing better data security.
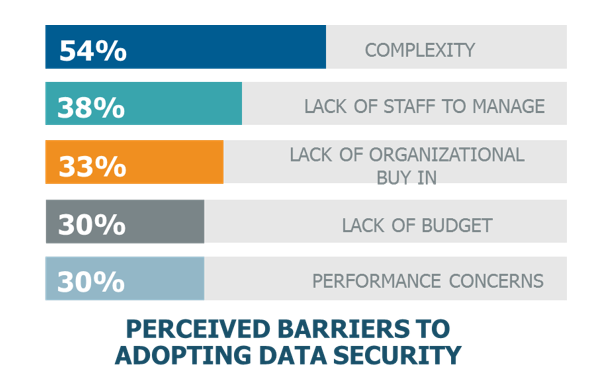 When thinking about Healthcare IT Security, I always have to consider whether they are getting enough funding given organizations laser focus on patient care and well-being. The surprise this time, was that funding wasn't the problem - it was the perception of complexity (54%) that kept most healthcare IT pros from implementing better data security, with lack of budget a distant 4th at 30%.
When thinking about Healthcare IT Security, I always have to consider whether they are getting enough funding given organizations laser focus on patient care and well-being. The surprise this time, was that funding wasn't the problem - it was the perception of complexity (54%) that kept most healthcare IT pros from implementing better data security, with lack of budget a distant 4th at 30%.
The perception of data security as too complex may well have it's roots in the past. At one point, (say 10 years ago) most encryption solutions didn't connect well to directory services and identity management systems, were hideously complicated to deploy (especially on end points) and imposed a high performance penalty of 15% to 30% overhead with software-based encryption. Fast forward today, and each of these difficulties is much reduced. Solutions play well with IAM tools, can even deploy without taking applications offline (like our Live Data Transformation solution at Vormetric), and use hardware-based encryption built into today's CPUs - making the overhead from encryption frankly difficult to even measure.
So IT Security pros in Healthcare - It's time to look up for a moment, reassess your IT security plans, and then think about what you should really be prioritizing.

 Andy Kicklighter | Director of Product Marketing
Andy Kicklighter | Director of Product Marketing