 Towards the end of 2015, Vormetric, in conjunction with 451 Research, conducted a comprehensive global survey of security professionals to get a pulse on the state of the security industry’s level of preparedness to deal with threats to data, both from insiders as well as external threat actors. Overall, the results of the 2016 Global Data Threat Report contained a mix of both surprising and not-so-surprising results. At a high-level, however, one of the most notable aspects to come out of the report was the extent to which our thinking about security hasn’t changed much over the years, despite the drastic changes that have occurred in both the types of assets that we now need to protect – cloud, Big Data, IoT, etc. – as well as our adversaries.
Towards the end of 2015, Vormetric, in conjunction with 451 Research, conducted a comprehensive global survey of security professionals to get a pulse on the state of the security industry’s level of preparedness to deal with threats to data, both from insiders as well as external threat actors. Overall, the results of the 2016 Global Data Threat Report contained a mix of both surprising and not-so-surprising results. At a high-level, however, one of the most notable aspects to come out of the report was the extent to which our thinking about security hasn’t changed much over the years, despite the drastic changes that have occurred in both the types of assets that we now need to protect – cloud, Big Data, IoT, etc. – as well as our adversaries.
Click to Tweet: IT Security Pros @gabekker with @451Research says: We're buying tool to fight the last war bit.ly/2ckYpR0
As we noted in the various global, regional and vertical editions of the 2016 report, the findings bring to mind the old saying about military generals tending to focus on fighting the last war. The report also suggests some possible explanations for why the information security industry continues to set records in various categories year after year: VC funding, M&A activity, spending on security products and services, and – unfortunately – data breaches.
Notably, there were several observations that emerged from the survey that, in our minds at least, point to a few significant disconnects in our collective thinking that have helped to perpetuate the current state of the security industry, as well as our inabilities to effectively deal with evolving threats.
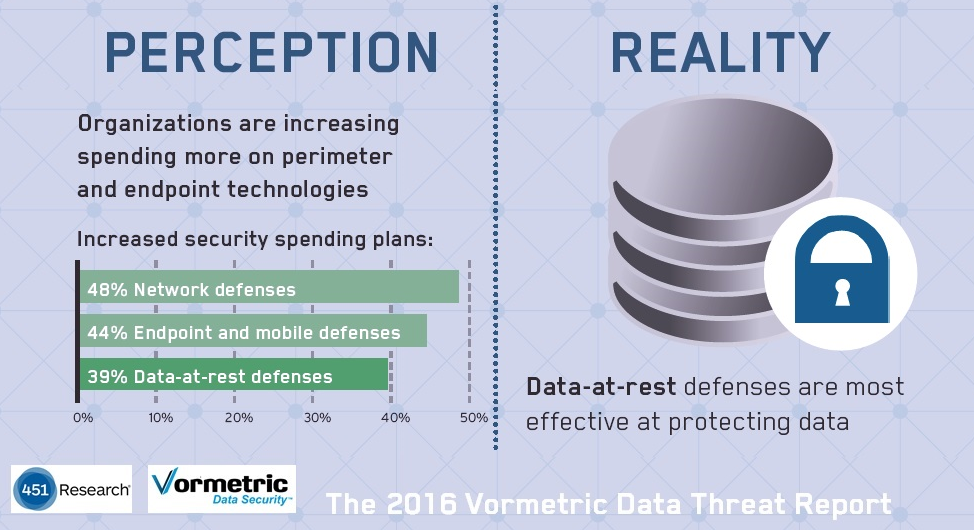
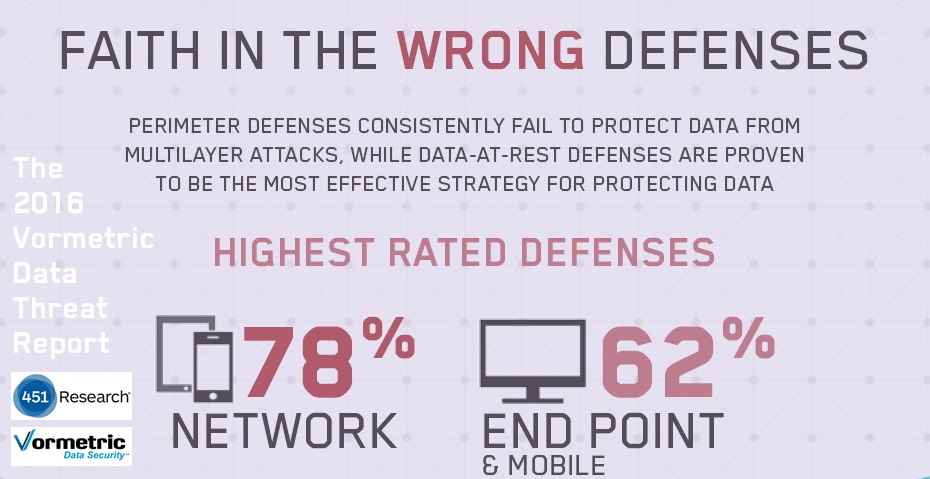
One of the main ones was evident in our attitudes towards what are the most effective ways to protect against data threats, contrasted with what we are spending our money on. As an industry, we are slowly coming around to the realization that network and endpoint security are no longer enough to make sure our resources are fully secure, to the point that vendor marketing pitches proclaiming the ‘perimeter is dead’ have become a cliche. Yet we still continue to spend more money on network security - 48% of global respondents planned to increase their spending on network security, significantly more than any other area of security.
What’s wrong with this picture? After a year or so of pondering this question, a few reasons come to mind. For starters, anyone who has been around the information security industry for any period of time likely cut their professional teeth on firewalls, and also maybe IPS or a WAF. After you’ve spent a bunch of years installing, tuning and getting certified on the latest Cisco or CheckPoint or Palo Alto gear, it’s a hard habit to break.
 Another advantage of firewalls is transparency - they are relatively easy to deploy, and also typically don’t have any noticeable impact on your employees or end users. Do all the basic configurations and rules offline during normal hours, then do the final cut over on the weekend when nobody’s around. When your employees come back to the office on Monday, they’re generally none the wiser that the latest whiz-bang next-gen firewall was installed while they were away at the beach.
Another advantage of firewalls is transparency - they are relatively easy to deploy, and also typically don’t have any noticeable impact on your employees or end users. Do all the basic configurations and rules offline during normal hours, then do the final cut over on the weekend when nobody’s around. When your employees come back to the office on Monday, they’re generally none the wiser that the latest whiz-bang next-gen firewall was installed while they were away at the beach.
Not necessarily so with other security tools – most areas outside of network and endpoint security place some sort of burden on end users. For example, the security industry has been called for the end of the password for at least fifteen years, but multi-factor authentication can require extra steps during the log-in process, and in the case of hardware tokens, can also introduce the problems of what to do with lost or stolen hardware tokens, dead batteries, etc.
Similar issues can arise with other security tools, including data security, which can impose additional requirements on end users as can be the case with data classification, or present performance or accuracy challenges like some DLP tools. But often the biggest challenge that we hear from customers with respect to more widespread adoption of data security is complexity. Not surprisingly, complexity was rated the number one adoption barrier for data security, selected by 57% of global respondents. The obvious message to data security vendors is to make their products easier to use if they want to grow their customer bases.
Compliance is another major disconnect that came up in our study. Again, the notion that ‘compliance does not equal security’ is an increasingly common phrase that has also arguably become a cliché, and some might suggest is overstated. Clearly, compliance can have several important security benefits, including establishing a framework for an overall security strategy, setting a baseline for future security efforts, and even making it easier to receive funding. But the point isn’t that compliance has no value to security efforts, but that compliance is just a starting point, not an end in itself. Unfortunately, our report suggests there are still an alarming number of folks in the industry who see as an end in itself - nearly two-thirds (64%) viewed compliance requirements as either “very effective” or “extremely effective” in preventing data breaches, despite the fact that we read about new breaches in the press nearly every week, many of them likely affecting firms that long ago checked off their compliance boxes.
To be sure, there were a number of positives to come out of our report. The number of respondents (39%) who indicated that their organization has either experienced a data breach or failed a compliance audit due to data security issues in the past year has held steady from our two prior surveys, we’re seeing encouraging signs that many organizations are moving towards implementing security best practices and not just checking compliance boxes, and the majority of respondents expect their spending on data security to increase (58%). But at the end of the day, the numbers don’t lie – we still have a lot of work to do, and noting Freud’s definition of insanity - if we keep on doing what we’ve been doing, we’ll keep getting the same results.

 Garrett Bekker |
Garrett Bekker |