Simply put: encryption is the most effective way for security professionals to protect their data. But, once you decide to encrypt, the question stops becoming “why” and becomes “how.” There are many different use cases in which sensitive data can reside, and thus there are seemingly endless ways to protect your data. These techniques include: full disk encryption, database encryption, file-level encryption, tokenization, dynamic data masking, and static data masking. And this is just naming a few.
Confused? Don’t worry, all of these choices can be overwhelming. If you are just getting started with your encryption program, I recommend reading Cracking the Confusion: Encryption and Tokenization for Data Centers, Servers, and Applications, by leading security analyst firm, Securosis. If you’re looking for a summary, please check out our Selecting the Right Encryption Approach web page.
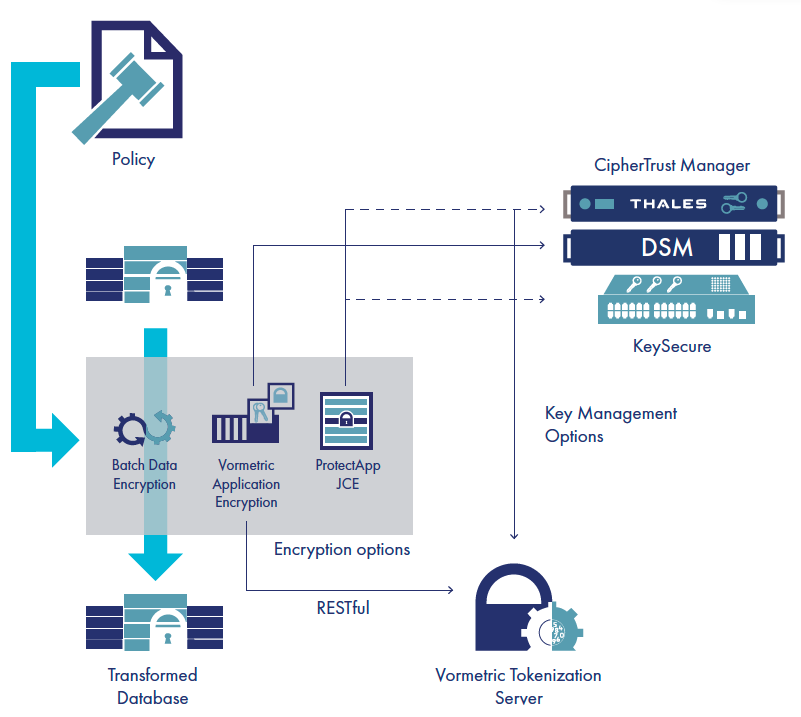
In my experience, I have found that most organizations will require a mix of technologies and solutions to meet all the use cases they support. Unfortunately, applying multiple homegrown and vendor tools can quickly become a complex, inefficient and expensive scenario. This is the exact problem Thales addresses with our Vormetric Data Security Platform. The platform delivers a comprehensive selection of encryption, tokenization and masking capabilities to meet the broadest sets of data security and compliance use cases. Ultimately, the Vormetric Data Security Platform removes the complexity that leads to operational inefficiencies and high-costs for data security.
We recently announced new enhancements and features to the Thales Vormetric product line, including a new product: Vormetric Batch Data Transformation. This new product is incredibly flexible and delivers several important functions for efficient encryption, tokenization and masking deployment.
So what are these functions? Let’s break them down…
Accelerate Encryption and Tokenization Adoption
Vormetric offers products that make it easy to add encryption to existing applications. Many companies use both the tokenization and encryption products from Thales. For example, Vormetric Tokenization is often used with applications that handle credit cards. By tokenizing the credit cards at the application, our customers can remove much of the network, servers, and databases that handle these credit cards numbers from their PCI DSS audit scope, which saves them a lot of time and money.
Similarly, customers use our products when they want to add encryption capabilities to their applications. One way to do this is to use Vormetric Application Encryption, which is a set of libraries that makes it very easy to integrate both NIST standard format preserving encryption (FPE) and AES encryption into applications. For example, you may deploy this product to remove of ePHI data from healthcare records.
However, there is typically an existing database that stores customer information, including their credit card and ePHI data. So the following question arises: “How do we transform the existing sensitive data so it will work in our new highly secure environment?” The answer from Thales is: “Easily and quickly by using Vormetric Batch Data Transformation with your Vormetric Token Server and Vormetric Application Encryption deployments.”
Quick and Easy Batch Data Transformation for Everyone
Whether you are using either or both Vormetric products to add tokenization with dynamic data masking or encryption to your organization’s applications, you can utilize the same Batch Data Transformation utility.
Batch Data Transformation is a virtual appliance that leverages existing Vormetric infrastructure. For example, it uses the Vormetric Data Security Manager for encryption key management and works with both Vormetric Token Server and Application Encryption libraries. All you need to do is simply deploy the method(s) that you want to use, set the encryption or tokenization policies to match what you will be deploying in production, and select what database columns need to be transformed into encrypted or tokenized data.
And voila! You now have a production database with your sensitive data protected and ready to work with your applications.
Static Data Masking
You don’t exist in a vacuum. There may be situations where your organization wants/needs to share a database with a 3rd party, such as a testing group or analytics company, or you may be required to share data with a big data analytics team. Now, you need to remove the sensitive data before sharing the database, however, you want to keep data integrity.
Static data masking is one effective method to keep data accurate, consistent and safe. Plus, this process is another important job that Batch Data Transformation can assist with. In fact, our solution will even support tokenizing dates within your defined date range.
Batch Data Transformation is new, but it will soon be a cornerstone solution in the Vormetric product line. This product offers simplicity of deployment and flexibility in capabilities. With one tool, you have the ability to accelerate the data security deployments and quickly deploy static data masking services for your organization. Batch Data Transformation demonstrates Thales commitment to provide companies with security and trust they need to protect their data in any environment, while maintaining the agility their business requires.

 Charles Goldberg | VP, product marketing
Charles Goldberg | VP, product marketing