This year, DefCon’s theme was 1983, intending to represent the choices a society may face on the eve of full authoritarian control. We attended the show with our colleague Paul Cleary and sat in on many talks (and demos) ranging from attacking IoT devices over insecure Bluetooth connections, to exploiting publically available expired certificates. There were many security issues present in corporate AD implementations, and hacking commonly-used voting machines was discussed. And the tin-foil hat challenge was equally entertaining!

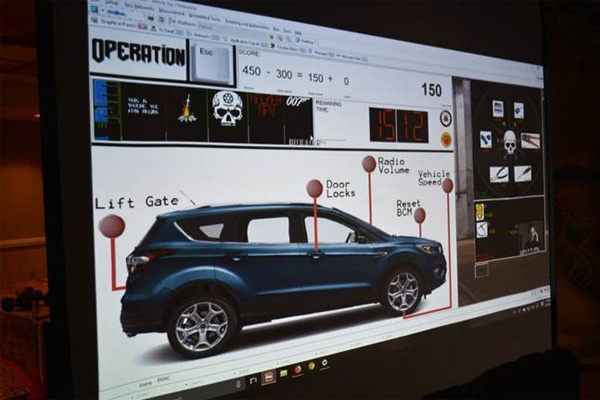
From L to R: the Tin-foil hat challenge; this year’s innovative DefCon badge; an attendee tries her best at the Car Hacking Village; Car Hacking Village challenge on display
Are You a Good or Bad Hacker?
This year’s DefCon badges were electronic and contained a hidden game that could only be completed by connecting to the board over a serial interface and by interacting with other badge holders at the conference. The player (the red character above) must navigate through the board and make decisions that either help hackers or hurt them. Good decisions lead to the individual letters in “DEFCON” turning green while bad decisions turn them red. The goal: become either a good hacker, or a bad hacker… the choice is yours!
Car Hacking
Another noteworthy part of the show was the Car Hacking Village where, this year, there were mobility scooters, a Ducati motorcycle and an SUV for CTF (Capture the Flag). The SUV was part of an escape-room like game. Although we didn’t see this part of the game, the village staff would blindfold and restrain a participant at random points in the day. The newly captured would have to work against the countdown clock to escape their bonds and hack the SUV to earn points. Overall, it was very impressive.
There were 28 villages this year and all of them were interactive. This is a clear sign that DefCon is growing and will continue to do so for the foreseeable future.
Keys at Scale
Our favorite presentation was a talk called “Reaping and Breaking Keys at Scale: When Crypto Meets Big Data.” The presenters gave a demonstration of breaking public keys and deriving the private key half using large amounts of computational power. The presenters collected over 300 million public keys from across the internet (X.509, SSH, PGP, etc.) and, by exploiting RSA modulus factorization using a 280 vCPU server cluster, they were able to derive the private keys from the public keys in less than an hour. At a time when public keys are virtually everywhere on the internet it is especially pertinent that organizations ensure that the keys they use are strong and unexpired. The presenters recommended that RSA should only be used with a minimum of 4,096 bits and are generated with strong primes. Elliptic Cryptographic Curve (ECC) keys are immune to this type of attack and, as such, are recommended where applicable.
We all enjoyed the convention and are looking forward to next year!
Author: Matthew Jochim and Matt Tycksen
