Zero-Downtime Encryption and Key Rotation
Enables administrators to encrypt entire file systems or databases and do key rotation—with minimal disruption.

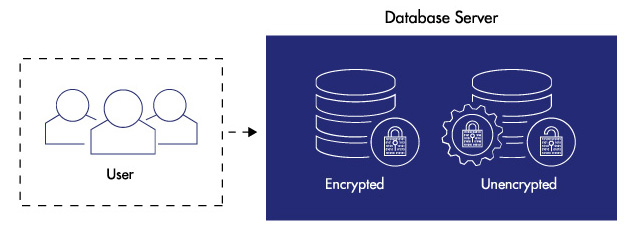
A database protected with Vormetric Transparent Encryption and Live Data Transformation enables non-disruptive initial encryption and simplified, more-compliant encryption key rotations. Users continue to work as usual while encryption is in process.
Deployment and management of data-at-rest encryption can present challenges when transforming clear-text to cipher-text, or when rekeying data that has already been encrypted. Traditionally, these efforts required planned downtime, or they required labor-intensive data cloning and synchronization efforts. Vormetric Transparent Encryption Live Data Transformation, with zero downtime encryption deployments, eliminates these hurdles, enabling encrypt and rekey with unprecedented uptime and efficiency.
Vormetric Transparent Encryption Live Data Transformation, with zero downtime encryption deployments, allows for encrypting and re-keying data without taking applications offline. This allows for deployment of data security controls to applications along with business continuity and high availability.
In the past, critical applications had to be taken offline for initial encryption of data and encryption maintenance, with substantial operational costs - Not any more with Live Data Transformation zero-downtime encryption.
Compliance requirements and best practices demand periodic encryption key changes. With Live Data Transformation, maintaining standards no longer requires downtime - applications and users continue to work as usual during rekey operations.
With key versioning management, Live Data Transformation offers efficient backup and archive recovery that enable more immediate access. In a data recovery operation, archived encryption keys recovered from the Vormetric Data Security Manager are automatically applied to an older data set. Restored data is encrypted with the current cryptographic keys.
Live Data Transformation enables your administrators to encrypt data with zero downtime or any disruption to users, applications, or workflows. While encryption is underway, users and processes can continue to interact with databases or file systems as normal.
To align with security best practices and many regulatory mandates, it is vital to rotate cryptographic keys on a periodic basis. Live Data Transformation makes it fast and efficient to address these requirements. With the solution, you can perform key rotation without having to duplicate data or take associated applications off line.
Requires Vormetric Transparent Encryption as a prerequisite.
Microsoft—Windows Server 2008 and 2012; Linux—Red Hat Enterprise Linux (RHEL) 6 and 7, SuSE Linux Enterprise Server 11 and 12
Veritas Cluster Server Active/Passive; Microsoft Cluster—File Cluster, SQL Server Cluster
Cassandra, CouchBase, Hadoop, MongoDB, SAP HANA
DB2 backup, NetBackup, NetWorker, NTBackup, Oracle Recovery Manager (RMAN), Windows Server Volume Shadow Copy Service (VSS)

보안 위협과 규정 준수 요구 사항이 날로 증가함에 따라 데이터 암호화는 IT 보안 전략의 계층화에 필수적인 요소가 되었습니다. 많게는 다음과 같은 두 가지 문제가 기존의 데이터베이스, 파일 및 빅데이터 환경에 암호화 기술을 도입하는 데 중대한 걸림돌로 작용합니다.