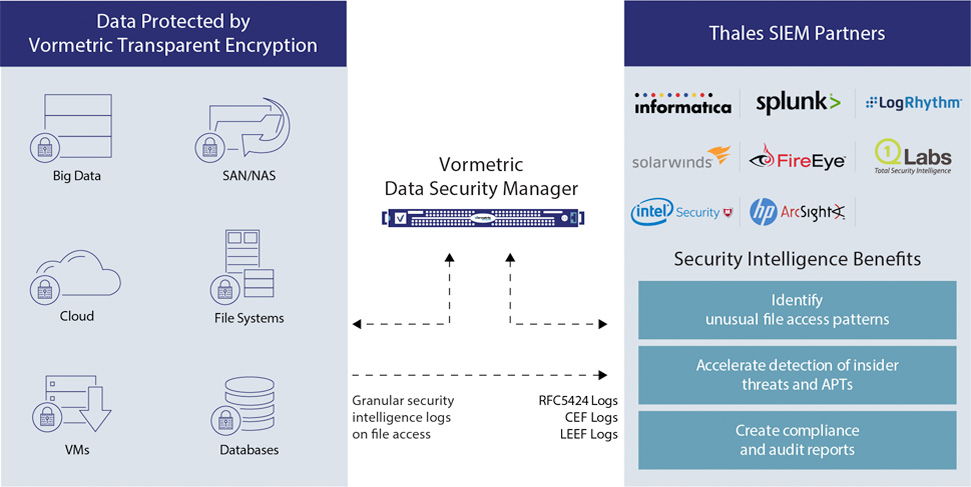
Pre-built SIEM Integrations
Collected at the system level, Vormetric Transparent Encryption logs report authorized and unauthorized access attempts to encrypted files and volumes- including user, time, process and more. Vormetric Security Intelligence includes pre-built integration to leading SIEM systems that makes these logs actionable. Available dashboards immediately highlight unauthorized access attempts. Authorized user access data is available to create baselines for user's data usage, and can also be integrated with other security data such as user location and access points for pinpoint threat identification.
Granular, Actionable Security Intelligence
Vormetric Security Intelligence logs produce an auditable trail of permitted and denied access attempts from users and processes. The solution’s detailed logs can be reviewed to specify when users and processes accessed data, under which policies, and if access requests were allowed or denied.
Streamlined Compliance and Auditing Reporting
In order to adhere to many compliance mandates and regulations, organizations must prove that data security is in place meets required standards. Vormetric Security Intelligence integration to SIEM systems and pre-built dashboards can be used to easily demonstrate to an auditor that encryption, key management, and access policies are effective and appropriate. With its detailed visibility and integration capabilities, Vormetric Security Intelligence helps streamline the effort associated with audits and ongoing compliance reporting.