On March 12, I participated in a webcast webinar with SC Magazine on how to guard against a data breach. The webinar content highlighted the results of SCMagazine's 6th annual data breach survey which polled IT security professionals in the US, UK and Australia, and also featured Stephen Fridakis, CISO at the Food and Agriculture Organization of the United Nations, who shared his interpretation of the results and discussed the various measures he and his peers intend to implement in order to keep data out of the wrong hands.
To keep the data that matters out of the hands of increasingly sophisticated attackers, it is important to put in place proactive, data-centric security measures that include strong access and control policies and it is absolutely vital to gather security intelligence on a continuous basis. In a world where the attack landscape is getting larger at the same time organizations are looking to move to the cloud, gain competitive advantage from Big Data, and ensure that they have crossed their "t's" and dotted their "i's" relative to emerging global compliance requirements, the need for data-centric security is a top priority. Perimeter security is failing, and the consequences of that can be dire.
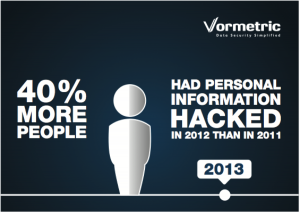 It's clear from the SC Magazine data breach survey results that data breaches are continuing to escalate, and that both the financial and brand reputation costs are rising as well. While many cited plenty of challenges with which they must contend, and fully 85% of the survey respondents agree that the threat of a breach, loss or exposure is greatly influencing their organization's security initiatives, the majority of survey respondents said they are optimistic about the steps they are taking to safeguard critical data from getting lost or stolen. I find that interesting because a bright spotlight is clearly on them and the business risks of misplaced confidence are high. The survey found that security concerns are now coming down from the board level because directors want to understand the overall risk and security posture of the company. I think it's safe to say that at least some of the respondents who expressed a great deal of optimism about their overall readiness will end up with egg on their faces at best, and more likely in the unemployment line. The need for robust information security plans and data control mechanisms is now being acknowledged by executive leaders across all major industries; it is no time for IT professionals to get complacent.
It's clear from the SC Magazine data breach survey results that data breaches are continuing to escalate, and that both the financial and brand reputation costs are rising as well. While many cited plenty of challenges with which they must contend, and fully 85% of the survey respondents agree that the threat of a breach, loss or exposure is greatly influencing their organization's security initiatives, the majority of survey respondents said they are optimistic about the steps they are taking to safeguard critical data from getting lost or stolen. I find that interesting because a bright spotlight is clearly on them and the business risks of misplaced confidence are high. The survey found that security concerns are now coming down from the board level because directors want to understand the overall risk and security posture of the company. I think it's safe to say that at least some of the respondents who expressed a great deal of optimism about their overall readiness will end up with egg on their faces at best, and more likely in the unemployment line. The need for robust information security plans and data control mechanisms is now being acknowledged by executive leaders across all major industries; it is no time for IT professionals to get complacent.
Some of our webinar participants were curious to better understand how they could put in place an effective security intelligence solution, and exactly how Data-Centric solutions like ours work with Security Intelligence and Event Monitoring (SIEM) solutions. Others wanted to know how better access policies might help them stop ATPs/data breaches. Still other participants (who were obviously feeling the pressure to get a solution in place as soon as practical) wanted to know how long it would take to deploy an effective data-centric security solution.
Cyber attacks have been going on for decades – as we've seen in both the real world and in Hollywood. Do you think most organizations prepared to thwart today's cyber attacks? Are they being lulled into a false sense of security since they've managed to check off the compliance box and put perimeter security in place? What are the pressing security questions floating around your organization?
Tina Stewart is Vormetric’s VP marketing. Follow her on Twitter @SocialTIS.

 Tina Stewart | VP, Global Market Strategy
Tina Stewart | VP, Global Market Strategy