The Vormetric Data Security Platform
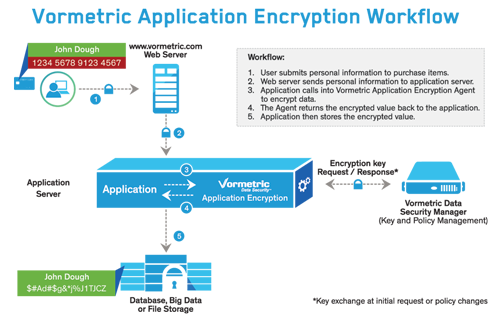
Yesterday was a big day for Vormetric, the culmination of the long process of creating a new product – Vormetric Application Encryption. This offering is a major extension of our Data Security Platform, giving our customers powerful capabilities for granularly encrypting field, column and file data within enterprise and web applications, as well as cloud and big data environments.
With the addition of Vormetric Application Encryption to the Vormetric Data Protection Platform, we have created a single, flexible, centralized capability for organizations to meet legal and industry governance requirements that mandate protection of data-at-rest. This platform approach results in greater efficiency and lower costs. Instead of multiple infrastructure sets, integrations, vendors, maintenance requirements, training, deployment and resource allocations, organizations can easily use Vormetric’s single platform to meet multiple encryption use cases for data, saving both time and money.
Click to Tweet: Save Money and Time @Vormetric w/single #DataSecurity Platform for Application and File Encryption http://bit.ly/1bJlGZc
A few use cases for this Vormetric Application Encryption include:
- Enterprises with compliance and regulatory requirements for data protection can build data encryption capabilities directly into their cloud and in-house applications.
- Cloud providers can extend and secure their offerings with new compliance and data security capabilities to protect customer data with encryption.
- When implemented for use with a big data environment, organizations can now encrypt both source and output data to meet regulatory mandates, compliance and data security requirements.
As you might guess from the capabilities discussed, this is a developer level product, designed for organizations and partners who have a direct need for data-at-rest encryption as they create and customize their own applications and environments. Included are key management, sample code sets in Java, Microsoft .NET, C++, API documentation, our standard Vormetric Data Security Manager management environment and more.
We’ve created this new product as a direct response to the needs of our customers and partners – Finding that:
- More than 80% have a significant need to design encryption directly into their in-house applications and environments
- They see significant value in having this capability from a single platform with our other offerings.
- Just as with our other products, customers and partners see great time to value – getting up and running quickly and with minimal effort
- Our high performance encryption architecture is a real advantage - leveraging Intel AES NI hardware based encryption from Intel’s current set of CPUs
It just makes sense – One infrastructure set, management environment and integration, deployment model and vendor to meet multiple needs enhances efficiency and reduces costs.