When it comes to data security, identifying what you consider your crown jewels is the first step in the data security recovery program. Legacy products can be expensive and negatively impact performance. Organizations need to realize that the complexity and fear of access control is a thing of the past.
ClickToTweet: Why a Data Security Platform is an Enterprise Priority #DefenderOfData http://bit.ly/1uLLONG
Before we get started on recovery, here are a few things you need to ask yourself:
- How much privacy do employees warrant?
- What level of control do I need to monitor activity?
Organizations’ scope and goals come down to one thing: 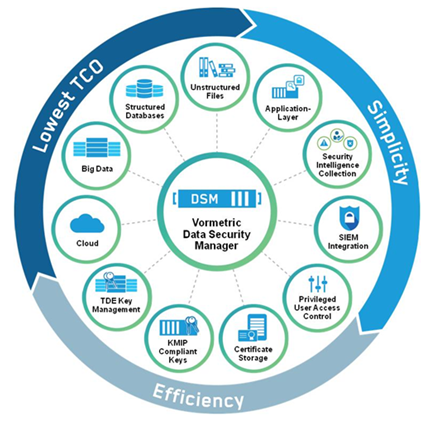 simplify the data breach strategy. While seemingly simple, IT environments are complicated, sophisticated and frankly, just all over the place. On top of that, it’s usually a very large organization that needs protecting and IT infrastructure is not always as clean as you would think.
simplify the data breach strategy. While seemingly simple, IT environments are complicated, sophisticated and frankly, just all over the place. On top of that, it’s usually a very large organization that needs protecting and IT infrastructure is not always as clean as you would think.
Fear not, there are three ways to tackle this problem:
- Invest in a platform that gives you the most coverage.
- Simplify your infrastructure.
- Educate yourself – Optimized solutions can be multiple vendors across the environment.
Another major problem is that organizations are continuing to focus on the perimeter. Usually encryption boils down to self-encrypting drives. With that, comes full access to the system. If you remove admins from the equation, this type of security can be very successful. But there are techniques and tools out there to mitigate that risk.
Give the least amount of visibility needed to do the job. It really comes down to reducing the risk (the attack surface that the adversary can attack and pursue). I typically see three types of accounts: HR where security professionals understand necessary IT privileges, third parties like cloud providers and admins. Quite often, by default admins get access to everything because that is the nature of the beast. But everyone does not need that elevated level of privilege.
In a bank vault, employees have to come in and clean the floors, so they have access. If you are going to let them in the bank vault you don’t want them to have access to secure systems. In this instance, the employee should only have access to what’s needed for their job. It works similarly with IT departments: admins should only have access to certain information. Eduard Snowden is a perfect example. He had broad administrative privileges but someone should never be able to have access to all data.
An insider traditionally is well obfuscated. They are hard to find and are touching all your sensitive data which in turn means that they have the opportunity to expose all your information. They have a lot of risk that comes with them. We’ve identified a few data security best practices to help eliminate that risk:
- Identify what runs your data – i.e. what are the crown jewels?
- Once you identify those assets, find out where they are. Is it data that is actually collaborated on through multiple end users? Identify where it is.
- What controls will I put in place to mitigate the risk? Am I going to use controls like encryption, tokenization and the PCI use-case?
Individuals can’t steal what they don’t have access to. Once you understand the information you mitigate that risk from potential advisories. Data security platforms that offer encryption and tokenization are all great techniques to help mitigate that risk.
