Yesterday, we issued the latest installment of our 2016 Vormetric Data Threat Report (DTR), highlighting results from IT security executives at large enterprises in Mexico and Brazil. And while this edition did indeed offer some unexpected findings, the 2016 Vormetric DTR has thus far revealed a resounding and unified theme – data breaches are an epidemic of global proportions.
Yesterday, we issued the latest installment of our 2016 Vormetric Data Threat Report (DTR), highlighting results from IT security executives at large enterprises in Mexico and Brazil. And while this edition did indeed offer some unexpected findings, the 2016 Vormetric DTR has thus far revealed a resounding and unified theme – data breaches are an epidemic of global proportions.
Click To Tweet: Data Breaches Gone Global #2016DataThreat Mexico and Brazil Edition bit.ly/1TmyqpQ pic.twitter.com/vKkqFxJcZS
This overarching message has also been demonstrated by recent international cyberattacks. Take, for example, the recent cyberattacks against Bangladesh, in which thieves stole $81 million from the Bangladesh central bank’s account at the Federal Reserve Bank of New York. Vietnam’s Tien Phong Bank also suffered a cyberattack, as well as The Turkish Citizenship Database. Closer to home for our customers and partners in the Latin America region, a massive data breach exposed the personal information of 93.4 million Mexicans. With this steady drumbeat of international breaches, it’s clear that the threat of cyberattacks is continuing to grow across the globe.
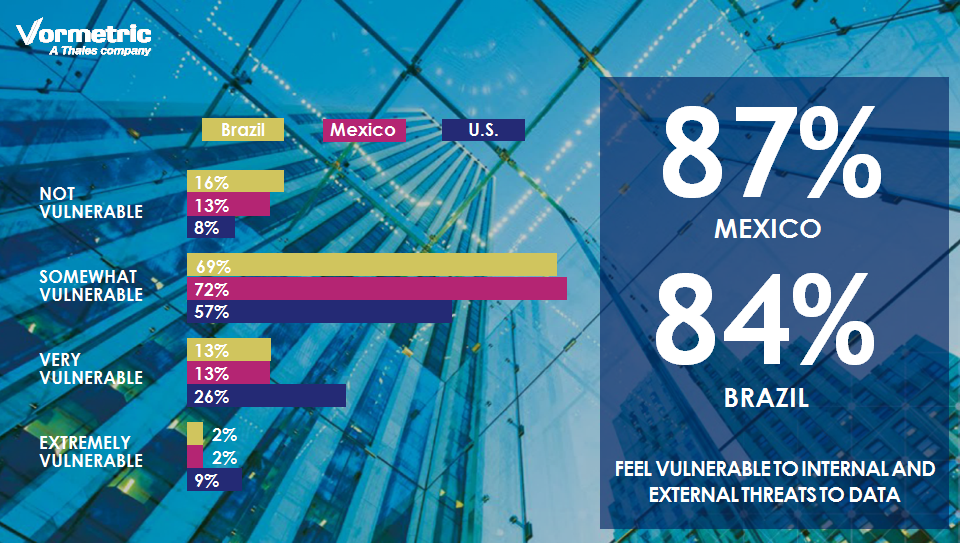 In Latin America specifically, our survey revealed that 87% of IT decision makers in Mexico and 84% of those in Brazil (up from 69% in the 2015 edition of the report) say their organization is vulnerable to data threats. Unfortunately, while the report showed that IT security leaders in both Mexico and Brazil are worried about data breaches, they are being held back from adding data-centric security by the perception of complexity (Mexico 49%, Brazil 50%) and lack of staff (Mexico 45%, Brazil 46%).
In Latin America specifically, our survey revealed that 87% of IT decision makers in Mexico and 84% of those in Brazil (up from 69% in the 2015 edition of the report) say their organization is vulnerable to data threats. Unfortunately, while the report showed that IT security leaders in both Mexico and Brazil are worried about data breaches, they are being held back from adding data-centric security by the perception of complexity (Mexico 49%, Brazil 50%) and lack of staff (Mexico 45%, Brazil 46%).
This has to be based on the experiences that most of us had 8 or more years ago with deploying the first generations of widely used encryption and other data protection tools. Those tools often had little or no integration with directory services, high overhead and were not friendly in the roll out, implementation and on-going management processes. But things have changed, although apparently most of those we surveyed haven't realized it yet. Modern solutions are well integrated with management and deployment tools, use hardware encryption to keep overhead to a minimum (in most circumstances it's hard to measure) and can even be deployed without taking down applications and systems. It's a new day for data protection tools, but, time and again we found in our global survey that IT Security Pros weren't aware that things had changed.
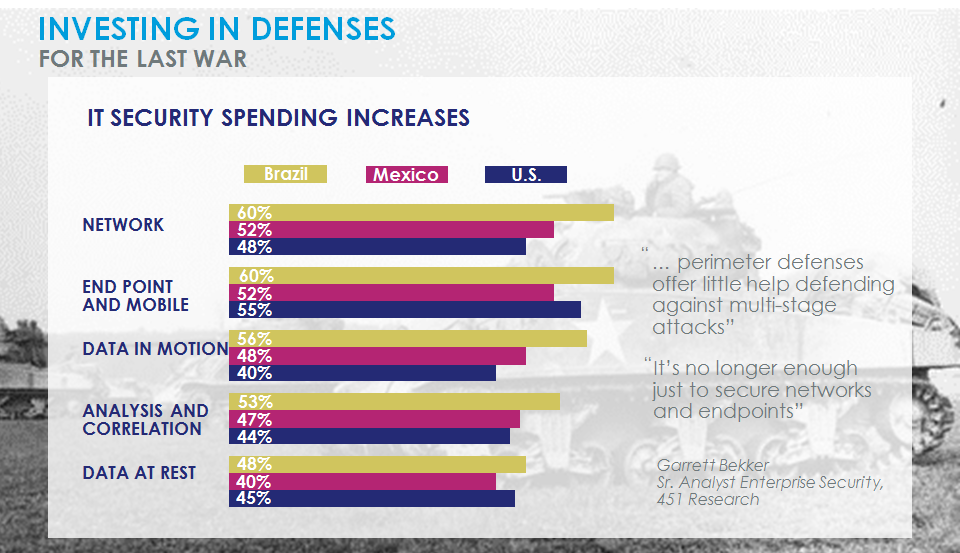
Survey respondents also stated that their IT security spending is increasing fastest on defenses that are no longer completely effective at protecting data. In Mexico, 52% of respondents indicated increased spending on both network and endpoint defenses. In Brazil, 60% of IT security pros noted increased spending on network defenses, as well as 58% on endpoint defenses. And while technologies like network and antivirus security tools are important components of a layered security approach, they are not able to ensure the safety of data once attackers compromise networks and systems.
Thankfully, there is a bright side to this story – both Mexico and Brazil showed much more optimism than other regions when it came to data security. While network defenses had a strong showing in both nations, respondents from both Mexico and Brazil ranked data-in-motion defenses as the most effective at securing sensitive data – 85% of respondents from both countries identified the latter as being either ‘very’ or ‘extremely’ effective, well ahead of the global average of 75% and the U.S. at 79%.
While data-at-rest defenses took third place for both Mexico (77%) and Brazil (80%), the percentages were higher than any other region and also comfortably ahead of the global average response of 72% and the U.S. at 75%. Unfortunately their shared optimism towards data security is not yet translating into spending, with data-at-rest defenses ranked at the bottom in terms of spending priorities for the next 12 months in both Mexico (48%) and Brazil (40%).
It’s time for organizations in Latin America and around the globe to wake up and smell the (data protection) coffee. While traditional endpoint, network and perimeter IT security solutions have reduced risk, they have not been completely effective against hackers – it’s no longer a question of if you’ll be breached, but when. And when attackers have bypassed perimeter defenses, data-at-rest security controls (such as those offered by Vormetric) will be the final layer of defense in protecting an organization’s sensitive data from compromise.
Do you have questions? Interested in learning more about what Vormetric has to offer? Leave a comment below, or tweet me @akicklighter.

 Andy Kicklighter | Director of Product Marketing
Andy Kicklighter | Director of Product Marketing