MFA implementation is still a problem for many companies
Market analysts have made the disturbing statement that many companies have still not deployed MFA broadly. A Gartner survey (1) showed that only 55% of respondents implemented MFA for administrator access to Active Directory. Recently, Kuppingercole highlighted in an Analyst Chat about MFA adoption that only 20% of M365 customers have activated MFA.
Thales customers deploying MFA are worried by the deployment phase and are eager for best practices and Return of Experience (ROX). Thales presales and partners frequently answer questions like:
- How do we ensure end-user adoption of MFA?
- How can we guide end-users into MFA activation?
- How do we reduce IT overheads and the number of calls to Helpdesk?
- How do we monitor the MFA implementation?
- How can we get MFA activated by 100% of the targeted users?
User Experience is key for successfully implementing MultiFactor Authentication
In their report “Avoid the Top 9 Pitfalls of Implementing MFA” (1), Gartner makes several recommendations that any IT Professional in charge of deploying MFA should take into consideration. According to Gartner, “deploying MFA is the single effective step you can take to improve security”, [but] “deploying MFA is a complicated endeavor. Different user constituencies require different credentials….risks and security must be carefully balanced against user experience …”
Gartner recommends Enterprises to:
- Select an MFA offering that provides multiple credential types, excellent user experience (UX), and integrates into target applications.
- Include both technical and non-technical staff in early pilots and training to improve training practices, uncover support issues and determine accurate support requirements.
Implementing MFA effectively and efficiently
Thales supports Enterprises in deploying MFA by providing a large variety of user-friendly authenticators as well as on-demand self-provisioning capabilities in our cloud MFA solution. Our customers have recognized the benefits provided by those capabilities in a recent survey:
- 83% of surveyed IT organizations said they benefit from multiple authentication methods that SafeNet Trusted Access provides
- 88% of surveyed IT organizations said the automated token provisioning that SafeNet Trusted Access provides to their organization is beneficial or very beneficial
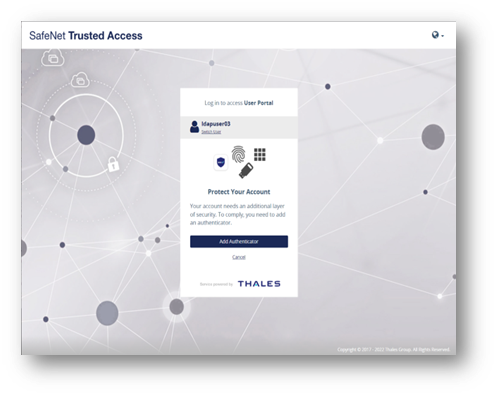
Make MFA activation available to end users when they need it
We observed that traditional bulk MFA activation - based on a one-shot enrollment emailing campaign asking end users to enroll their authenticator – was frequently unsuccessful. Many end users did not register their token right away when they received the email, as it was not an immediate need for them. When MFA became mandatory a few weeks later, the same users were blocked and called Helpdesk because they could not retrieve the enrollment email to activate their authenticator.
In our MFA solution, the option to add a new authenticator is embedded into the end user authentication flow, accessible from the login page when the user accesses a service.
Eliminate user guides and training thanks to best in class User Experience
Thales UX design team significantly improved the User Experience during authenticator self-provisioning by automating the application download, guiding the end user step-by-step all along the activation process, providing instructions directly on the screen, or making the task self-understanding.
The design was based on factual usability researches, and usability was measured via the System Usability Scale, as defined by ISO 9241-11 standard: the self-provisioning of our mobile app called SafeNet MobilePASS+ reached a score of 85 out of 100, far above other products available on the market (for which the scores were between 43 and 55 ) (2).
Cover all the variety of user authentication journeys
We provide self-provisioning capability to a broad selection of authenticators and platforms to cover the variety of authentication journeys and authenticate from everywhere:
- Internal and external users can self-provision SafeNet MobilePASS+ on their company-managed or personal devices (Android or iPhone, Windows desktops, Chromebooks, Apple Watches and Mac very soon).
- Internal and external users can self-provision GrIDsure, a software, clientless, pattern-based authenticator compatible with any OS.
- Both SafeNet MobilePASS+ and GrIDsure can be self-provisioned by multiple users on shared desktops.
- Privileged users or frontline workers can self-provision a FIDO key to
- To access high-risk, web applications securely.
IT remains in control of self-provisioning
IT must keep control of authentication self-provisioning. That is why we provide in SafeNet Trusted Access the flexibility to IT administrators to configure which type of authenticator can be self-enrolled by which group of users.
Thanks to an intuitive user interface, the IT administrator configures it in a few clicks before launching the MFA deployment.
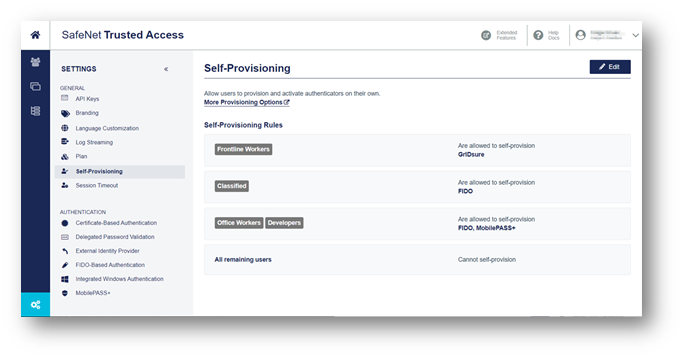
To get more information on authenticator self-provisioning within SafeNet Trusted Access, watch these videos about GridSure , SafeNet MobilePASS+, and read our guides on FIDO keys self-provisioning, self-provisioning rules for groups, GrIDsure self-provisioning, and MobilePASS+ self-provisioning.
(1) Avoid the Top 9 Pitfalls of Implementing MFA, Gartner G00745872, June 2021
(2) SUS scores obtained from a user experience study conducted by a 3rd party consultant agency for Thales in 2020 and 2022

 Holger Brückner | Product Manager, Thales
Holger Brückner | Product Manager, Thales