NIST 제로 트러스트 보안 지침의 시행 - 백서
디지털 트랜스포메이션, 혁신적인 기술의 확산, 그리고 ‘재택근무’와 같은 새로운 트렌드는 기업의 디지털 경계를 허물었습니다. 경계가 허물어지고 그야말로 모든 곳에서 액세스 요구가 증가하는 상황에서 기존 경계 보안 솔루션으로 대응하는 것은 충분하지 않습니다.
기업 내 모든 트랜잭션을 신뢰할 수 없고 정의된 보안 경계가 없다면, 지속적으로 신원을 검증하여 액세스 포인트에서 데이터를 암호화하고 앱을 보호하는 것이 기업 보안의 핵심입니다.
안전하고 편리한 재택근무
직원이나 계약자, 컨설턴트가 어디에서 어떤 장치를 사용하든 쉽고 편리한 로그인 경험을 제공합니다.
클라우드에서
안전하게 확장
클라우드 액세스 포인트에서 클라우드 앱을 보호하여 기존 보안 체계의 한계를 극복합니다.
침해 방지 및 보유 데이터 보호
데이터를 암호화하고 지속적으로 신원을 검증하여 앱을 보호합니다.
NIST는 효과적인 제로 트러스트 보안 아키텍처를 구축하기 위한 세 가지 접근 방식을 설명합니다.
제로 트러스트 아키텍처의 신원 중심 접근 방식은 정책 생성의 중추에 사용자, 서비스, 장치의 신원을 배치합니다. 기업 리소스 액세스 정책은 신원과 할당 속성을 기반으로 합니다. 기업 리소스에 액세스하는 기본 조건은 지정된 사용자나 서비스, 장치에 부여된 액세스 권한에 따릅니다. 더욱 강력한 적응형 인증을 제공하고자 하는 경우, 사용된 장치, 자산 상태 및 환경 요인과 같은 다른 요인도 고려하여 정책을 시행할 수 있습니다.
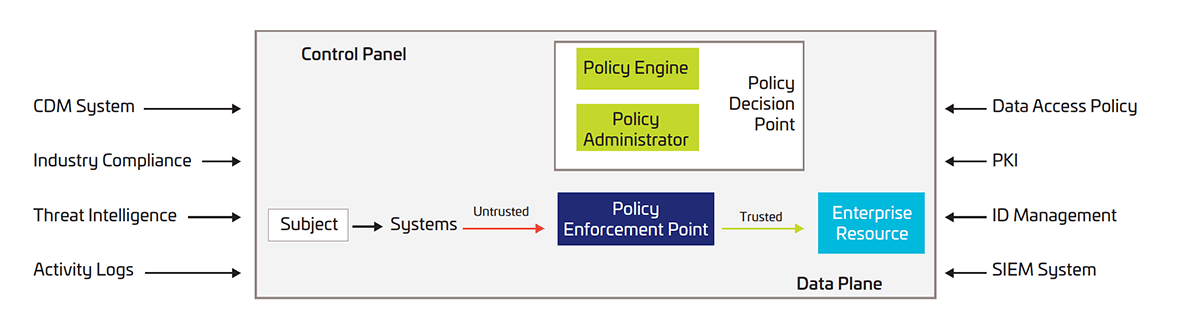
제로 트러스트 아키텍처의 네트워크 중심 접근 방식은 기업 리소스의 네트워크 마이크로 세분화를 기반으로 하며 이는 게이트웨이 보안 요소에 의해 보호받습니다. 이 접근 방식을 구현하고자 하는 기업은 지능형 스위치(또는 라우터), 차세대 방화벽(NGFW) 또는 소프트웨어 정의 네트워크(SDN)와 같은 인프라 장치를 사용하여 각각의 리소스나 관련 리소스 그룹을 보호하는 정책 시행 기능을 담당하도록 해야 합니다.
클라우드 기반 통합 제로 트러스트 아키텍처 접근 방식은 클라우드 기반 액세스 관리 및 SASE(Software at the Service Edge)를 활용합니다. 클라우드 기반 액세스 관리 솔루션은 클라우드 애플리케이션과 서비스의 신원을 보호하고 적용하는 반면, SDN(소프트웨어 정의 네트워크) 또는 NGFW(차세대 방화벽)와 같은 SASE 요소는 온프레미스 리소스를 보호합니다.

디지털 트랜스포메이션, 혁신적인 기술의 확산, 그리고 ‘재택근무’와 같은 새로운 트렌드는 기업의 디지털 경계를 허물었습니다. 경계가 허물어지고 그야말로 모든 곳에서 액세스 요구가 증가하는 상황에서 기존 경계 보안 솔루션으로 대응하는 것은 충분하지 않습니다.
SafeNet Trusted Access(STA)
탈레스의 클라우드 기반 액세스 관리·인증 서비스인 SafeNet Trusted Access는 제로 트러스트 원칙을 충족하는 효과적인 제로 트러스트 보안 구현의 출발선입니다.
SafeNet Trusted Access에 대해 자세히 알아보기

디지털 혁신, 커다란 변화를 불러오는 기술의 확산, '재택근무'와 같은 새로운 트렌드에 더해, 크게 증가하는 데이터 침해나 보안 사고로 신뢰의 개념이 사라졌습니다. 제로 트러스트 보안은 "절대 신뢰하지 말고 항상 확인하라"는 원칙을 기반으로 하며 신뢰를 취약성으로 간주하고, 엄격하고 지속적인 신원 확인으로 무조건적인 신뢰 영역을 최소화하도록 합니다.

2019년 봄, RSA 콘퍼런스 기간 중 모스콘 센터의 방대한 전시장을 방문했다면 수없이 많은 전시 부스에 놀라셨을 겁니다. 부스의 크기는 제각각으로 다양했으나 모든 부스는 같은 것을 판매하고 있었습니다. 바로, 보안입니다. 이는 예상 가능한 일이었습니다. 그러나 모두 제로 트러스트와 머신 러닝이라는 두 가지 중요한 보안 주제를 다루고 있다는 점은 예상을 벗어났습니다.

지난달, 미 국립 표준 기술원인 NIST의 컴퓨터 보안 리소스 센터는 특별 간행물 SP 800-207에서 제로 트러스트 아키텍처 구현의 일반 지침 및 권장 사항을 발표했습니다. 당연하게도 이 최신 문서는 제로 트러스트 보안에 대한 NIST의 입장을 반영하지만, 이러한 관점이 어떻게 형성되었는지를 보여주는 두 가지 정보를 짚어보는 것 또한 중요합니다.

원활한 인증, 온라인 리소스에 대한 지속적인 액세스는 달성하기 어려운 목표였습니다. 수많은 이들이 시도했지만, 실제 달성한 이는 거의 없었습니다.
모든 조직에 있어 클라우드 도입은 디지털 혁신 목표를 향한 디딤돌입니다. 비즈니스 요건에 따라 확장되며 디지털 혁신 목표의 진정한 잠재력을 달성하도록 지원하는 솔루션을 이용하여, 매우 유동적인 위협 환경에 대처하는 방법을 알아보시기 바랍니다.