 Any party bent on destruction, exposing proprietary business intelligence and sensitive customer information like credit card numbers and medical information can try to get access. But what’s more important is learning how to protect it.
Any party bent on destruction, exposing proprietary business intelligence and sensitive customer information like credit card numbers and medical information can try to get access. But what’s more important is learning how to protect it.
ClickToTweet: Easily, Efficiently Encrypt Teradata w/@Vormetric’s Data Protection Platform http://bit.ly/1Ocr0b2 #DefenderOfData
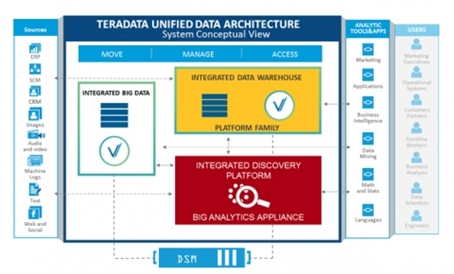
While data is crucial to enhance company product offerings and capture increased market share, when it’s not properly protected, it can be exploited. However the very advantage big data solutions provide — the ability to aggregate a wide range of data sources — can also present a significant risk. Data now comes from a variety of sources. CRM systems, files, spreadsheets can all contain sensitive information. As a result, it is critical to establish strong security controls over these sensitive assets without compromising the value of big data analytics.
Reliance on Teradata continues to proliferate, with an increasing number of enterprises leveraging these technologies to fuel the smarter decisions that can save money, enhance offerings and boost market share. As a Gartner Magic Quadrant leader and the largest global data warehousing company, we knew Vormetric’s latest platform extension was ideally suited as an extra layer of protection for Teradata.
Teradata is continually fine-tuning its offerings as data warehousing and big data continue to converge in the marketplace. Vormetric protects Teradata’s Hadoop Distribution as well as its integrated data warehouse, or Teradata’s traditional data service, which comprises the bulk of their business.
Vormetric’s offerings provide robust security solutions for Teradata’s customers as the platform extension provides a seamless integration for organizations that already work with both companies. For enterprises who make the investment in Teradata’s infrastructure, it only makes sense to also use Vormetric to provide a layer of security for this crucial data. Vormetric’s new platform add-on bolsters and protects what is usually a substantial investment made in Teradata’s infrastructure.
Through the integration, customers can take advantage of tools like sophisticated file encryption, tokenization, field-level encryption, privileged user access controls, centralized key management and file access logging to maximize their Teradata environments. This platform extension creates documented, standards-based application programming interfaces (APIs) and user-defined functions (UDFs) to perform key management operations.
Today, some of the largest and most security-conscious organizations in the world rely on the Vormetric Data Security Platform, which offers capabilities for file encryption, tokenization with dynamic data masking, field-level encryption, privileged user access controls, centralized key management, and file access logging. Now, Vormetric enables organization to leverage these robust data-at-rest security capabilities in Teradata environments.
