탈레스 Luna Network HSM
탈레스 Luna 네트워크 하드웨어 보안 모듈(HSM)은 온프레미스 환경은 물론, 클라우드 지원 환경 전반에서 애플리케이션이 사용하는 암호키에 매우 안전한 보안을 제공합니다. 탈레스 Luna Network HSM을 이용하는 조직은 중앙 집중식 플랫폼에서 전체 키 수명 주기를 보호하고 암호화 작업을 가속화하며 통합된 위치에서 암호키 감사를 처리하는 이점을 누릴 수 있습니다.
암호화는 데이터가 어디에 존재하든지 이 데이터를 보호, 제어하는 수단을 제공합니다. 그러나 암호화를 사용하면 데이터 콘텐츠에 대한 위험이 해당 데이터를 보호하는 암호키에 대한 위험으로 바뀝니다.
탈레스의 클라우드 키 관리 솔루션을 사용하면 키를 제어할 수 있으므로 클라우드에서 민감한 데이터와 워크로드를 안전하게 실행할 수 있습니다.
이제 클라우드의 암호화, 키 관리가 완전한 온프레미스 환경과 같이 수준 높은 보호 기능을 제공하므로 모든 조직이 새로운 효율성과 보안 수준을 달성할 수 있습니다.
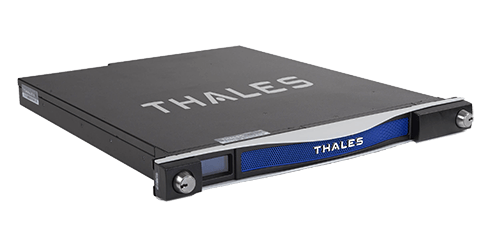
탈레스 Luna 네트워크 하드웨어 보안 모듈(HSM)은 온프레미스 환경은 물론, 클라우드 지원 환경 전반에서 애플리케이션이 사용하는 암호키에 매우 안전한 보안을 제공합니다. 탈레스 Luna Network HSM을 이용하는 조직은 중앙 집중식 플랫폼에서 전체 키 수명 주기를 보호하고 암호화 작업을 가속화하며 통합된 위치에서 암호키 감사를 처리하는 이점을 누릴 수 있습니다.
탈레스 Crypto Command Center를 사용하면 하나로 일원화된 보안 장소에서 탈레스 HSM을 쉽게 프로비저닝하고 모니터링할 수 있습니다. 이를 통해 암호화 서비스와 데이터에 대한 완벽한 제어를 유지하고 정책을 일관되게 시행하며 IT 인프라 전반에서 키 소유권을 명확하게 규정하는 동시에, 며칠이 아닌 몇 분 만에 데이터 보안 목적의 주문형 키 보관·암호화 서비스를 탄력적으로 제공할 수 있습니다.
입증받은 암호화 보안 솔루션의 이점을 누리면서 키의 완전한 소유권을 유지하는 동시에 클라우드의 유연성과 성능, 비용적 이점을 실현하실 수 있습니다. 자세한 내용은 백서에서 확인해보시기 바랍니다.

Customer-owned encryption: The only way to truly safeguard data stored and managed in cloud environments.
The inventor of the electronic exchange, The NASDAQ OMX Group provides transformative technologies for the entire lifecycle of a trade—from risk management to trade to surveillance to clearing. In the U.S. and Europe, the company owns and operates 23 markets, three...