- Select Year
- 2024
- 2023
- 2022
- 2021
- 2020
- 2019
- 2018
- 2017
- 2016
- 2015
- 2014
- 2013
- 2012
- 2011
- 2010
- 2009

Many years ago, a board member said to me, “We’ve employed you to do information security, so why do we have to do anything?” This was fairly typical. My experience in the past…
Read More
In the digital transformation era, companies across all sectors are using next-generation technologies to streamline their operations, deliver value to customers, and gain a…
Read More
As I was starting to write this blog, yet another retail program data breach occurred, for…
Read More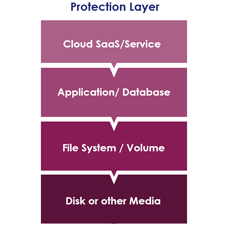
For most enterprise IT security professionals, there are some common reasons that we need to protect a given data set. For the most part, they fall into a few easy categories…
Read More
One of the top findings from the 2018 Thales Data Threat Report, Financial…
Read More
As we close in on the final few days of the year and look ahead to the clean slate that 2019 represents, I wanted to take a few moments to reflect on 2018 – specifically, what…
Read More
