In che modo i miei dati vengono protetti?
Quali certificazioni detiene la protezione dati on-demand di Thales?
La protezione dati on-demand di Thales (DPoD - Data protection on demand) è stata sottoposta a revisione indipendente e ha ricevuto certificazioni per FIPS 140-2 livello 3, ISO 27001 e SOC 2.
La protezione dati on-demand (DPoD) di Thales detiene una certificazione FIPS?
Gli HSM utilizzati per la protezione dati on-demand di Thales sono dotati di certificazione FIPS 140-2 livello 3.
In che modo i miei dati vengono protetti?
In che modo i "miei dati" vengono separati da quelli degli altri clienti?
Gli amministratori tenant hanno accesso solo ai dati che appartengono al proprio account. I dettagli specifici del tenant e/o i metadati sono protetti a riposo utilizzando la crittografia a livello di volumi.
Thales, il mio fornitore di servizi, o chiunque altro ha accesso alle mie chiavi crittografiche memorizzate in un HSM Cloud Luna?
Quando l'istanza HSM On Demand è inizializzata, il proprietario del servizio crea password o frasi sia per il responsabile della sicurezza che per il Crypto Officer.
Questi segreti sono utilizzati in uno schema di derivati e sono necessari per consentire all'HSM di desecretare il materiale crittografico.
Solo il responsabile della sicurezza/Crypto Officer è in possesso di questi segreti. La condivisione delle credenziali, se necessario, è lasciata alla discrezione di questi responsabili.
Quanto è solida l’integrità crittografica e dei dati?
I dettagli specifici del tenant e/o i metadati sono protetti a riposo utilizzando la crittografia a livello di volumi.
All’interno di ogni PoP, una sofisticata rete di router e firewall garantisce la separazione delle reti, l’integrità e la riservatezza dei dati e dell’accesso a questi ultimi.
All’interno della rete stessa, firewall interni separano il traffico tra l’applicazione e i livelli di database per garantire riservatezza, integrità e disponibilità elevata.
Penetration test del servizio
La soluzione di protezione dati on-demand di Thales viene sottoposta a penetration test regolari delle applicazioni e della rete?
Le applicazioni di Thales sono sottoposte a penetration test regolari delle applicazioni e della rete da parte di terzi, e la protezione dati on-demand di Thales aderisce a questa pratica. La metodologia di valutazione include processi di revisione strutturati basati su pratiche all’avanguardia quali definiti da metodologie come il manuale OSSTMM (Open Source Security Testing Methodology Manual) di ISECOM, il progetto OWASP (Open Web Application Security Project), WASC (Web Application Security Consortium) e lo standard ISO 27001:2013 sulla sicurezza delle informazioni.
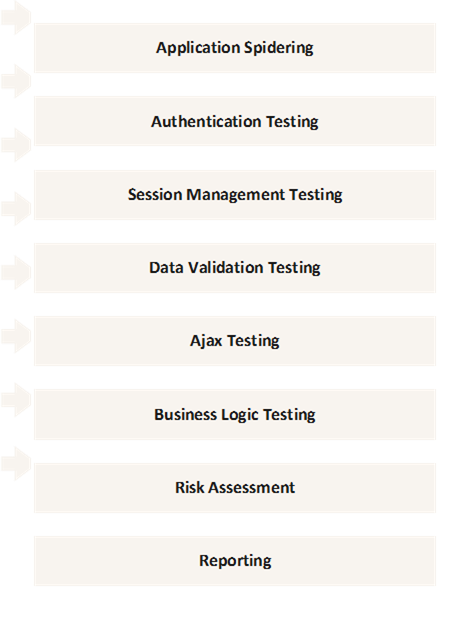
Ai fini dell’audit viene applicato il metodo gray-box per testare la sicurezza delle applicazioni. La figura seguente mostra alcuni dei vettori di attacco alla sicurezza che vengono testati. Eventuali problemi riscontrati sono risolti durante il regolare ciclo di sviluppo.
Vulnerability Manager
Posso ricevere prove del vostro programma di gestione della vulnerabilità?
Le applicazioni software di Thales sono sottoposte a penetration test regolari delle applicazioni e della rete da parte di terzi.
La metodologia di valutazione include processi di revisione basati su pratiche all’avanguardia quali definiti da metodologie come il manuale OSSTMM (Open Source Security Testing Methodology Manual) di ISECOM, il progetto OWASP (Open Web Application Security Project), WASC (Web Application Security Consortium) e lo standard ISO 27001:2013 sulla sicurezza delle informazioni.
Qual è il vostro processo di correzione delle vulnerabilità?
Quando viene rilevato un potenziale problema a carico della sicurezza, il personale autorizzato avvia un processo definito di gestione degli incidenti. Le azioni correttive sono attuate seguendo politiche e procedure definite.
Prima dell'aggiornamento effettivo del servizio vengono eseguite le seguenti attività:
- Test del provisioning: svolto sul servizio aggiornato in un ambiente controllato ed effettuato dal team addetto alle operazioni di servizio di Thales. Con la conclusione di questi test il codice ha superato con successo 3 cicli di prove, ciascuno effettuato da un gruppo diverso: test di unità a opera dello sviluppatore, test del codice in un determinato sprint eseguito dal gruppo di controllo qualità e infine il test del provisioning legato all’aggiornamento del sistema effettuato dagli addetti alle operazioni di servizio.
- Viene inviata una notifica di rilascio pianificato a tutti i clienti esistenti comunicando la portata dell’aggiornamento e la data prevista dell’effettivo aggiornamento del servizio.
- Penetration test: il penetration test viene effettuato su un sistema dedicato che non è in produzione, ma viene eseguito nello stesso ambiente del servizio operativo.
- Durante l’ultima fase, viene effettuato un backup di tutti i dati del servizio operativo, consentendo a Thales di eseguire un rollback immediato in caso di problemi imprevisti.
Quanto spesso cercate vulnerabilità nella rete e nelle applicazioni?
Effettuiamo revisioni mensili di tutte le patch per server e apparecchiature di rete.
Procedure e controlli interni di Thales
Thales esegue svariati controlli di servizio interni?
Sì, Thales esegue svariati controlli di servizio interni in linea con i campi di applicazione delle norme ISO27001 e SOC2, tra cui: sicurezza delle reti interne e delle informazioni, controlli basati sulla tecnologia, accesso fisico e controlli ambientali, gestione delle problematiche e dei cambiamenti, separazione delle responsabilità, gestione dei cambiamenti del software di sistema.
Sicurezza fisica del data center
In cosa consiste la protezione fisica del data center?
La sicurezza fisica è alla base di qualsiasi servizio basato su cloud, quindi tutti i data center sono presidiati 24 ore su 24, protetti da pattugliamento a piedi e ispezioni perimetrali con controlli degli accessi conformi alle best practice di settore. Questo può variare a seconda del data center, ma può includere prossimità, dati biometrici, chiavi, PIN o una combinazione dei controlli elencati.
I data center sono completamente attrezzati con videosorveglianza in tutte le strutture e i perimetri con monitoraggio della rimozione di risorse, garantendo la sicurezza delle attrezzature e dei dati detenuti al loro interno. I data center utilizzano inoltre tecnologie all’avanguardia garantendo ridondanze in connettività, alimentazione e sicurezza.
Quali sono le caratteristiche di sicurezza fisiche del servizio di protezione dati on-demand di Thales?
- In ogni struttura sono distribuite telecamere di videosorveglianza
- Protezione 24 ore su 24, 7 giorni 7 su sette: nessun accesso non protetto al data center
- Per l’ingresso al data center viene utilizzata l’autenticazione multi-fattore in ogni momento
Resilienza di rete
Come fa Thales a mantenere la capacità di selezionare la rete più resiliente in ogni dato momento?
Il data center privato è connesso ai principali fornitori di servizi internet utilizzando svariati fornitori e reti neutrali ed è situato nei pressi dei principali hub.
In che modo vengono fornite le connessioni di rete ai data center?
Le connessioni di rete ai data center vengono fornite utilizzando collegamenti sicuri con larghezza di banda ad alta capacità su connessioni in fibra per garantire una latenza minima della risposta alle richieste di autenticazione. Tutte le connessioni basate su fibra entrano negli edifici dei dati center passando in robusti seminterrati in calcestruzzo.
Su cosa si basa l’infrastruttura di rete interna del PoP?
L’infrastruttura interna del PoP si basa su una rete in fibra ad alta velocità per garantire un’elevata velocità di trasmissione dei dati. Questa infrastruttura utilizza connessioni multiple attraverso firewall e router di rete altamente sicuri per una ridondanza totale, nonché un traffico ottimale.
Quali sono le caratteristiche di sicurezza della rete dei PoP del servizio di protezione dati on-demand di Thales?
- I data center sono carrier-neutral
- Svariati canali in fibra in ogni data center
- Utilizzo di più fornitori di servizi internet per garantire un accesso a internet continuo e ad alta larghezza di banda
Alimentazione ridondante
In che modo l’alimentazione viene erogata ai data center?
L'alimentazione viene erogata ai data center utilizzando un alimentatore sotterraneo, che viene a sua volta integrato e supportato da generatori diesel ridondanti in loco (N+1) con un deposito locale di carburante diesel.
L'alimentazione viene erogata nelle stanze tramite sistemi CPS/UPS ridondanti (N+1) per garantire un approvvigionamento continuo, con alimentazione erogata ai rack PoP utilizzando unità di distribuzione elettrica (PDU) ridondanti. Ciò garantisce un accesso a internet continuo e ad alta larghezza di banda.
Backup e recupero dei dati
Su cosa si basa Thales per conservare copie dei volumi di archiviazione?
All'interno del cloud, Thales si basa su snapshot per mantenere le copie dei volumi di archiviazione associati alle istanze di applicazione.
Gli snapshot vengono creati ed eliminati a cadenza regolare. I backup dei database sono gestiti utilizzando backup di database relazionali. I log delle applicazioni sono archiviati online e memorizzati in modo sicuro per un determinato periodo di tempo. I dati sono conservati per un periodo di tempo correlato ai requisiti di conformità specifici della regione in cui sono memorizzati.
Quanto spesso vengono eseguiti test di restauro su tutto il servizio?
Ogni anno viene eseguito un test di restauro su tutto il servizio. Per questo test viene richiamato un nastro dalla memoria esterna e i dati vengono ripristinati in un ambiente di prova.
Thales ha un piano di disaster recovery?
Sì. Thales implementa un piano formale di disaster recovery, che viene mantenuto e testato su base annuale. Eventuali problemi individuati durante il test vengono formalmente discussi prima della predisposizione di piani di risanamento. Inoltre, Thales ha un piano formale di continuità aziendale che viene rivisto annualmente per introdurre eventuali aggiornamenti. Le procedure per correggere piccoli errori di elaborazione e interruzioni vengono documentate.
