ゼロトラストセキュリティモデルの主要原則
- 誰も信用しない – どこでも検証を行う
- 「デフォルト拒否」スタンスを採用する
- アクセスポイントでの安全なアプリケーション
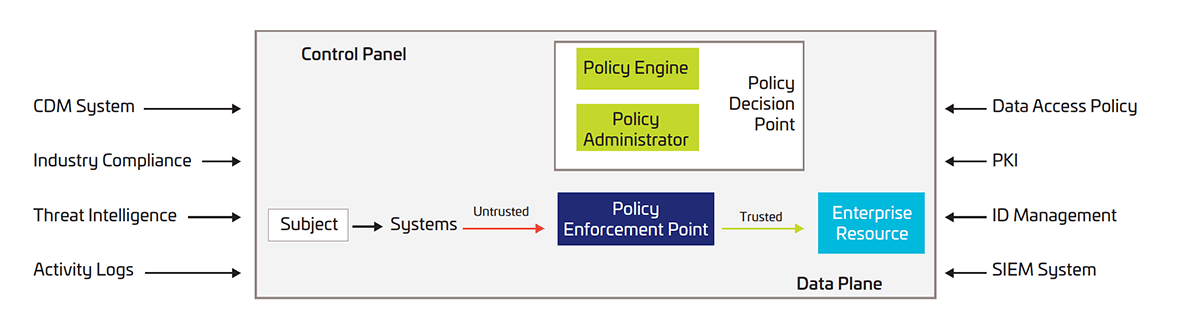
ゼロトラストセキュリティアーキテクチャ
NISTは、効果的なゼロトラストセキュリティアーキテクチャを構築するための3つのアプローチについて説明しています。
ID中心
ゼロトラストアーキテクチャのID中心のアプローチは、ユーザー、サービス、およびデバイスのIDをポリシー作成の中心に置きます。エンタープライズリソースアクセスポリシーは、IDと割り当てられた属性に基づいています。企業リソースにアクセスするための主な要件は、特定のユーザー、サービス、またはデバイスに付与されたアクセス権限に基づいています。より適応性のある認証に対応するために、ポリシーの実施では、使用されているデバイス、資産のステータス、環境要因など、他の要因も考慮する場合があります。
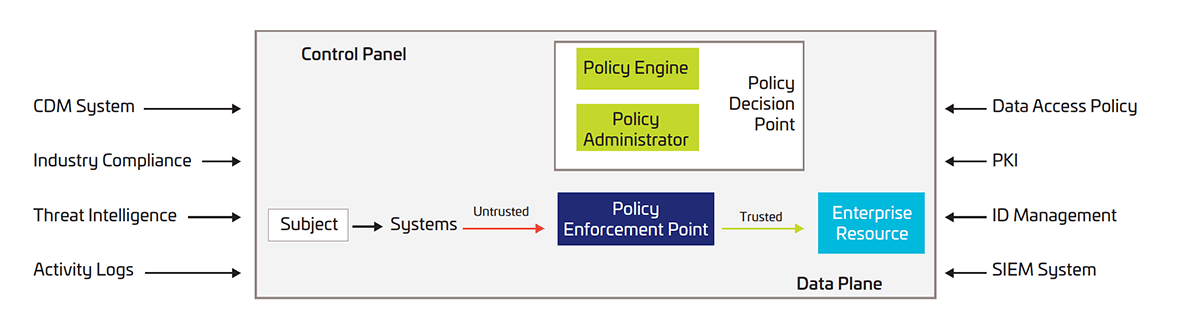
ネットワーク中心
ゼロトラストアーキテクチャのネットワーク中心のアプローチは、ゲートウェイセキュリティコンポーネントによって保護された企業リソースのネットワークマイクロセグメンテーションに基づいています。このアプローチを実装するには、企業はインテリジェントスイッチ(またはルーター)、次世代ファイアウォール(NGFW)、ソフトウェア定義ネットワーク(SDN)などのインフラストラクチャデバイスを使用して、各リソースまたは関連リソースのグループを保護するポリシー施行として機能する必要があります。
組み合わせアプローチ
クラウドベースの組み合わせゼロトラストアーキテクチャアプローチは、サービスエッジ(SASE)でクラウドベースのアクセス管理とソフトウェアを活用します。クラウドベースのアクセス管理ソリューションは、クラウドアプリケーションとサービスのIDを保護および適用し、ソフトウェア定義ネットワーク(SDN)や次世代ファイアウォール(NGFW)などのSASEコンポーネントはオンプレミスリソースを保護します。