シンガポール政府サイバーセキュリティ庁(CSA)はサイバーセキュリティ法に従い、重要情報インフラ(CII)所有者の規制を目的とする、サイバーセキュリティ長官発行の実施規範またはパフォーマンス基準を公表しました。重要情報インフラに関するサイバーセキュリティ実施規範 – 第2版(CCoP2.0) は前版の規範に取って代わるもので、2022年7月4日から施行されています。

重要情報インフラに関するサイバーセキュリティ実践規範(CCoP)の概要 - CCoP2.0の目的
CCoP2.0は、重要情報インフラ所有者(CIIO)がCIIのサイバーセキュリティを確保するために実施する必要がある最小要件を指定することを目的としています。CIIOは、CIIのサイバーセキュリティリスクプロファイルに基づき、CIIのサイバーセキュリティをさらに強化するために、この規範に規定されている以上の措置を実施することが期待されています。
- 高度かつ巧妙なサイバー攻撃に対するCIIのサイバーセキュリティ防御を強化します。
- CIIがクラウドコンピューティング、人工知能(AI)、5Gなどのテクノロジーによってもたらされる新たな課題に取り組むためのフレームワークを提供します。
- 急速に進化するサイバーセキュリティのリスクとインシデントに対応するCIIの能力を強化します。
- サイバー脅威を迅速に特定し対応するために、政府と民間部門間の連携と情報共有を促進します。
- 破壊的なサイバーイベントに対するシンガポールのCIIの全体的なレジリエンスを向上させます。
サイバーセキュリティ法は、重要情報インフラ(CII)の指定に関するフレームワークを提供するものであり、11の重要セクターにおけるCII所有者は、CIIセクターの強力なサイバーセキュリティ基盤を確保するために、CCoP2.0に定められたサイバー衛生に関する必須慣行に準拠する必要があります。
- 11の重要なセクター:エネルギー、情報通信、水道、医療、銀行・金融、セキュリティおよび緊急サービス、航空、陸上輸送、海事、政府、メディア。
- CCoP2.0の補遺として、OT CIIのサイバーセキュリティ態勢を向上させることを目的として、運用技術(OT)に特化したサイバーセキュリティに関する一連の必須慣行が導入されました。
コンプライアンス概要
シンガポールの重要情報インフラに関するサイバーセキュリティ実践規範(CCoP2.0)への準拠
CIIが包括的なサイバーセキュリティソリューションを通じて、どのようにCCoP2.0に準拠しているかをご覧ください。また、要件の詳細もご確認いただけます。
シンガポールのCCoP2.0への準拠達成のためにThalesがお手伝いできること
Thalesのソリューションは、コンプライアンスを簡素化し、可視化と制御によってセキュリティを自動化し、セキュリティおよびコンプライアンスチームの負担を軽減することで、CIIが保護条項と検出条項に重点を置きながらCCoP2.0要件に対応できるよう支援します。
シンガポールのCCoP2.0コンプライアンスソリューション
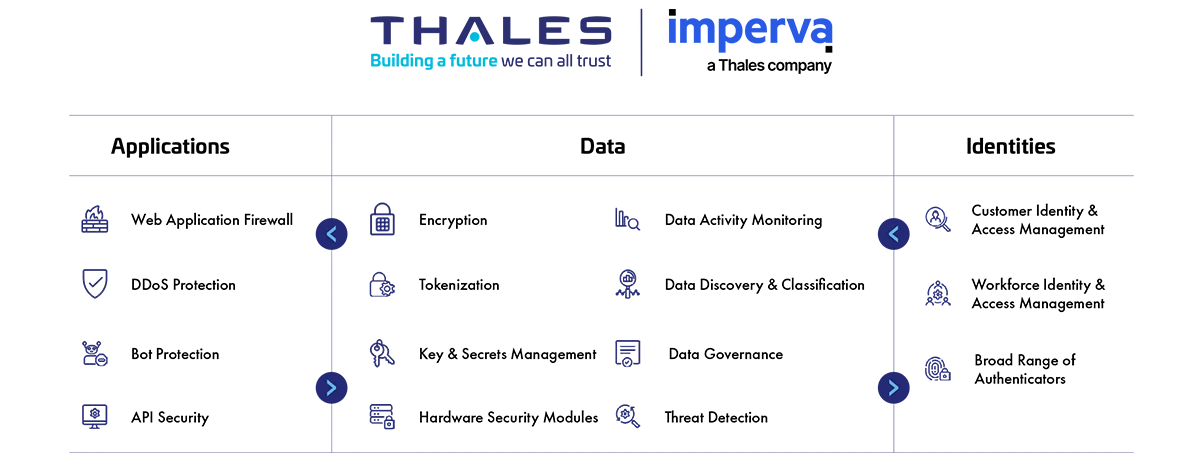
アプリケーションセキュリティ
クラウド、オンプレミス、ハイブリッドモデルのいずれにおいても、アプリケーションとAPIを大規模に保護します。当社の市場をリードする製品スイートには、Webアプリケーションファイアウォール(WAF)、分散型サービス拒否(DDoS)攻撃や悪意のあるBOT攻撃に対する保護、APIのセキュリティ、安全なコンテンツ配信ネットワーク(CDN)が含まれています。
データセキュリティ
ハイブリッドIT全体で機密データを検出・分類し、暗号化、トークン化、鍵管理を使用して、保存中、通信中、使用中のどの状態でも機密データを自動的に保護します。また、Thalesのソリューションは、正確なリスク評価のために潜在的なリスクを特定、評価、優先順位付けするとともに、異常な行動を特定し、アクティビティを監視してコンプライアンスを検証します。これにより、組織はどこに注力すべきかを優先的に判断できます。
IDおよびアクセス管理
顧客、従業員、パートナーに対して、アプリケーションやデジタルサービスへのシームレスで安全かつ信頼性の高いアクセスを提供します。当社のソリューションは、きめ細かなアクセスポリシーと多要素認証を使用して、役割とコンテキストに基づいて内部ユーザーと外部ユーザーのアクセスを制限し、適切なユーザーに適切なリソースへの適切なタイミングでのアクセスを許可します。
CCoP2.0条項への対応
Thalesがお手伝いできること:
- 社内外のユーザーのシステムやデータへのアクセスを、役割や状況に応じてポリシーで制限します。
- リスクスコアリングに基づき、コンテキストに応じたセキュリティ対策を適用します。
- 複数のハイブリッド環境に対するアクセスポリシーと適用を1つの画面で一元管理します。
- 役割ベースのアクセス制御を使用して鍵管理操作を統合します。
- DevOpsツール全体でシークレットへのアクセスを保護し、自動化します。
- システムにアクセスするユーザーが本当に承認されていることを確認するために、多要素認証(MFA)を提供します。
- シングルサインオン(SSO)を導入し、ユーザーが単一の認証によって複数のシステムに安全にアクセスできるようにします。
- ユーザーの役割、責任、リスクに基づいてアクセスポリシーを設定します。
ソリューション:
データセキュリティ
IDおよびアクセス管理
Thalesがお手伝いできること:
- 機密データのアクティビティを完全に可視化し、誰がアクセスしているかを追跡し、その操作内容を監査して文書化します。
- 自動化されたワークフローに柔軟な認証オプションを提供することで、パスワードへの依存を軽減します。
- シングルサインオン認証をクラウドアプリケーションに拡張し、保護されたIDを使用した安全な一元アクセスを実現します。
- 機密データに特権アクセス制御を適用します。
- 認証情報、証明書、鍵の包括的なシークレット管理を可能にします。静的シークレット、動的シークレット、SSHキー、APIキーのほか、技術スタック全体の特権アカウントに対して静的シークレットの代わりにジャストインタイムアクセス(動的シークレット)をサポートするトークンなどが含まれます。
Thalesがお手伝いできること:
- すべてのパブリックAPI、プライベートAPI、シャドーAPIの潜在的なリスクを検出し、分類します。
- 正当なトラフィックの許可を継続しながら、DDoS攻撃や悪性ボットから重要なネットワーク資産を保護します。
- データトラフィックを監視して、データ漏洩のリスクを特定します。
- ビジネスロジック攻撃やOWASP トップ10のAPI脅威の多くから保護します。
- Webアプリケーションファイアウォールでサイバー脅威を検知・防御します。
- 機密データを作成された時点で暗号化し、平文データが権限のないアプリケーションや担当者によって処理または保存されるのを防ぎます。
- DevOpsツール全体でシークレットへのアクセスを保護し、自動化します。
ソリューション:
アプリケーションセキュリティ
データセキュリティ
Thalesがお手伝いできること:
- 機密データに対する特権ユーザーアクセス制御を有効にし、最小限の権限設計で不正アクセスを制限します。
- ソースから宛先までの列レベルでのPIIといった、高速一括トークン化/暗号化を提供します。
- さまざまなKMIPクライアント、TDEエージェントなどを含む、コネクタとサードパーティデバイスの鍵と証明書の管理を統合します。
- 機密データのアクティビティを完全に可視化し、誰がアクセスしているかを追跡し、その操作内容を監査して文書化します。
- データベース攻撃や異常なアクセス要求をリアルタイムで警告またはブロックします。
- 異常なI/Oアクティビティがないかプロセスを継続的に監視し、悪意のあるアクティビティを警告またはブロックします。
- ランサムウェアを検出するためにアクティブなプロセスを監視して、過剰なデータアクセス、流出、不正な暗号化、悪意のあるユーザーなりすましといったアクティビティを特定し、そのようなアクティビティが検出された場合に警告またはブロックします。
Thalesがお手伝いできること:
- MySQLなどのデータストアに対して評価テストを実行し、既知の脆弱性をスキャンします。
- CISベンチマークに基づく1,500を超える定義済み脆弱性テストを使用してデータベースをスキャンし、最新の脅威からデータベースを保護します。
Thalesがお手伝いできること:
- FIPS 140-3レベル3環境で暗号鍵を保護します。
- 鍵のライフサイクル管理により、クラウド環境とオンプレミス環境での鍵管理を合理化します。
- 拡大を続ける様々なクラウド鍵管理用のIaaS、PaaS、SaaSプロバイダーに対応しています。SaaSソリューションにはMicrosoft Office365、Salesforce.com、Salesforce Sandboxのほか、SAP Data Custodianが含まれます。サポートされているIaaS/PaaSソリューションには、Microsoft Azure、Microsoft Azure China National Cloud、Microsoft Azure Stack、IBM Cloud、Google Cloud Platform、Amazon Web Servicesが含まれます。
- すべてのシークレットと機密情報を管理し、保護します。
- 職務分離の原則に基づき、暗号化されたデータとその暗号鍵を別の場所に保存します。
- 量子コンピューティングの脅威に対処するために、ポスト量子アジリティを採用します。
- ネイティブクラウド鍵とその鍵ソースによって生成された鍵の完全な鍵ライフサイクル管理を実行して、BYOKとHYOKをサポートします。
Thalesがお手伝いできること:
- シグネチャ分析、行動分析、評判分析を使用して、すべてのマルウェアインジェクション攻撃をブロックします。
- Webアプリケーションファイアウォールでサイバー脅威を検知・防御します。
- クラウドおよびオンプレミスのシステム全体ですべてのデータベースアクティビティを監視・監査することで、可視性を高めます。
- ポリシー違反発生時のリアルタイム警告やユーザーアクセスのブロックによって、データを保護します。
- ユーザーの行動、アプリケーションとAPIのアクセスパターン、データソースのコンテキストの統合に基づいた洞察を提供します。
- サーバー、クラウド、ファイル共有全体で非構造化データアクセスをリアルタイムで監視します。
- インテリジェントでコンテキストに富んだ分析による詳細な可視化とAI主導の洞察により、脅威と内部リスクを検出します。