In October 2022, Indonesia enacted its Personal Data Protection (PDP) Law (Law No. 27 of 2022), which is the first overarching regulation on data protection applicable to various sectors and marks a significant advancement in the country's regulatory framework for data privacy. The PDP Law reflects the growing importance of data privacy in the digital age, emphasising the rights of individuals regarding their personal data.
What is the Personal Data Protection (PDP) Law in Indonesia?
The PDP Law has 76 articles across 16 chapters, which extensively cover data ownership rights and prohibitions on data use, along with the collection, storage, processing and transfer of personal data of Indonesian users. It also introduces new concepts, including the requirement for both prior and post notifications to the regulator on cross-border personal data transfers. The PDP law goes further by introducing criminal sanctions for personal data breaches.

Overview of the Personal Data Protection (PDP) Law in Indonesia
The Indonesian Personal Data Protection (PDP) Law aims to safeguard personal data and establish a clear set of guidelines for its collection, processing and storage, aligning Indonesia with global data protection standards. It introduces comprehensive provisions governing data subjects' rights, data controllers' responsibilities and the enforcement mechanisms necessary to ensure compliance.
- Data collection and processing: Must be lawful, fair, transparent and limited to a specific purpose.
- Consent: Requires explicit, informed and specific consent from individuals for data processing, with special provisions for children and individuals with disabilities.
- Data subject rights: Individuals have rights to access, rectify, erase, withdraw consent, object to processing and request data portability.
- Security measures: Data controllers must implement appropriate security measures to protect personal data from loss, misuse or unauthorised access.
- Data breach notification: In case of a data breach, controllers must notify the affected individuals and the Personal Data Protection Agency.
The PDP Law governs personal data protection across sectors, affecting businesses within and outside Indonesia. It applies to the processing of sensitive data of Indonesian citizens or to activities that involve legal repercussions.
Violations can result in administrative penalties, including warnings, temporary suspension of data processing and fines, as well as criminal sanctions like monetary penalties and imprisonment.
Criminal penalties include fines for individuals of up to IDR 6 billion (USD 368,232), for corporations up to IDR 60 billion (USD 3,682,326) and imprisonment ranging from 4 to 6 years.
Compliance brief
Ensuring compliance with the Personal Data Protection (PDP) Law in Indonesia
Explore solutions for the Personal Data Protection Law by simplifying compliance and automating security, reducing the burden on security and compliance teams.
How Thales helps with Personal Data Protection (PDP) Law compliance in Indonesia
Thales' Cybersecurity Solutions help organisations address data security provisions on Chapters IV, V, VI and VII in the PDP Law by simplifying compliance and automating security with visibility and control, reducing the burden on security and compliance teams.
PDP compliance solutions
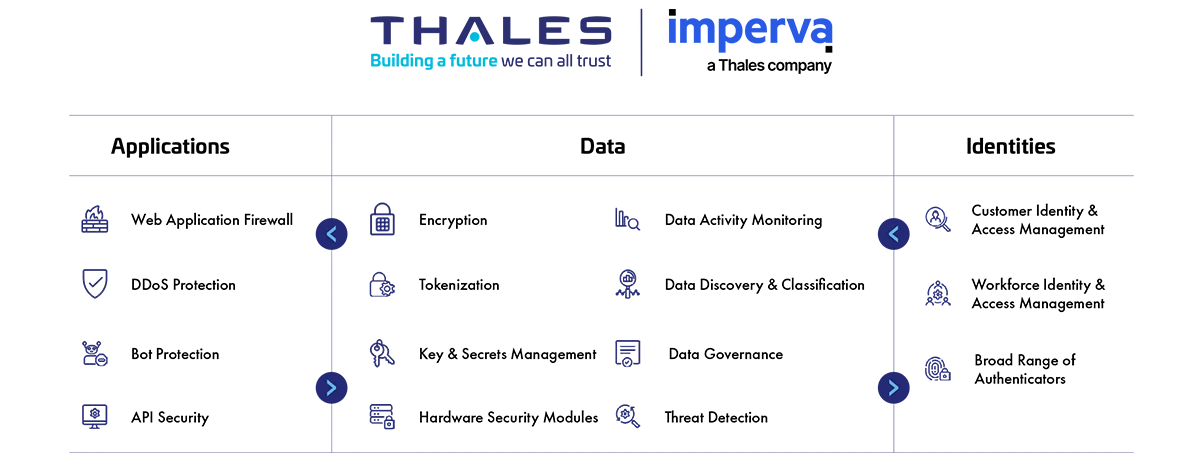
Application security
Protect applications and APIs at scale in the cloud, on-premises or in a hybrid model. Our market leading product suite includes Web Application Firewall (WAF), protection against Distributed Denial of Service (DDoS) and malicious BOT attacks, security for APIs and a secure Content Delivery Network (CDN).
Data security
Discover and classify sensitive data across hybrid IT and automatically protect it anywhere, whether at rest, in motion or in use, using encryption tokenisation and key management. Thales solutions also identify, evaluate and prioritise potential risks for accurate risk assessment as well as identify anomalous behaviour and monitor activity to verify compliance, allowing organisations to prioritise where to spend their efforts.
Identity & access management
Provide seamless, secure and trusted access to applications and digital services for customers, employees and partners. Our solutions limit the access of internal and external users based on their roles and context with granular access policies and Multi-factor authentication that help ensure that the right user is granted access to the right resource at the right time.
Address PDP requirements
How Thales helps:
- Gain visibility by tracking, analysing and responding to database activities in real time.
How Thales helps:
- Protect against unauthorised access by users and processes in physical, virtual and cloud environments with transparent and continuous encryption.
- Pseudonymise sensitive information in databases.
- Gain full sensitive data activity visibility, track who has access, audit what they are doing and document.
- Identify abnormal user behaviour and provide a complete threat description with actionable intelligence for remediation.
- Protect the root-of-trust of a cryptographic system within a highly secure environment.
- Limit the access of internal and external users to systems and data based on roles and context with policies.
- Apply contextual security measures based on risk scoring.
Solutions:
Data security
Identity & access management
How Thales helps:
- Gain full sensitive data activity visibility, track who has access, audit what they are doing and document.
- Streamline reporting and analysis of user access rights to sensitive data.
How Thales helps:
- Provide continuous monitoring to capture and analyse all data store activity from both application and privileged user accounts with detailed audit trails.
- Protect sensitive personal data, such as personally identifiable information (PII), by replacing it with non-sensitive, format-preserving tokens.
- Encrypt data wherever it resides, on-premises, across multiple clouds and within big data and container environments.
How Thales helps:
- Examine application and database traffic to create a profile of baseline normal activity.
- Identify abnormal user behaviour and provide a complete threat description with actionable intelligence for remediation.
How Thales helps:
- Identify structured and unstructured sensitive data at risk on premises and in the cloud.
- Identify the current state of compliance, document gaps and provide a path to full compliance.
- Discover all your data and categorise it based on sensitivity and value, allowing you to uncover hidden data risks.
- Encrypt data at rest on-premises, across clouds and in big data or container environments.
- Pseudonymise sensitive information in databases.
- Protect data in applications/services as a performant SDK and eliminate the need for Developers (Devs) to manage security details and regularly update data protection.
- Protect data in motion with high-speed encryption.
- Streamline key management in cloud and on-premises environments with key lifecycle management.
- Protect the root-of-trust of a cryptographic system within a highly secure environment.
- Share and sync files in the cloud or on-premises with end-to-end encryption security.
How Thales helps:
- Prevent unauthorised access and alteration to its internals, including the audit logs.
- Pinpoint risky data access activity – for all users, including privileged users.
- Ensure complete separation of roles and restrict access to sensitive data.
- Limit access to systems and data based on roles and context with policies.
- Apply contextual security measures based on risk scoring.
- Centralise access policies and enforcement to multiple hybrid environments in a single pane of glass.
How Thales helps:
- Transparent and continuous encryption that protects against unauthorised access by users and processes in hybrid environments.
- Provide a unified visibility of risks to critical data with a unique view of the strength of encryption for data across your entire data estate.
- Prevent unauthorised access and alteration to its internals, including the audit logs.
- Alert or block database attacks and abnormal access requests in real time.
- Monitor file activity over time to set up alerts on activity that can put your organisation at risk.
- Monitor active processes to detect ransomware – identifying activities such as excessive data access, exfiltration, unauthorised encryption or malicious impersonation of a user, and alerts/blocks when such an activity is detected.
- Unify key management operations with role-based access control and provide full audit log review.
How Thales helps:
- Limit the access of internal and external users to systems and data based on roles and context with policies.
- Apply contextual security measures based on risk scoring.
- Gain full sensitive data activity visibility, track who has access, audit what they are doing and document.
- Protect against exposure in non-production environments by pseudonymising sensitive information in databases.
- Prevent unauthorised access and alteration to its internals, including the audit logs.
- Pinpoint risky data access activity – for all users, including privileged users.
- Reduce third party risk by maintaining on-premises control over encryption keys, protecting data hosted in the cloud.
- Ensure complete separation of roles between cloud provider admins and your organisation, restrict access to sensitive data.
- Monitor and alert anomalies to detect and prevent unwanted activities from disrupting supply chain activities.
- Enable relationship management with suppliers, partners or any third-party user; with clear delegation of access rights.
Solutions:
Data security
Identity & access management
How Thales helps:
- Protect sensitive personal data by monitoring and tracking the activities and interactions with a database in real time.
How Thales helps:
- Encrypt data at rest on-premises, across clouds and in big data or container environments.
- Pseudonymise sensitive information in databases.
- Unify key management operations with role-based access control and provide full audit log review.
- Protect the root-of-trust of a cryptographic system within a highly secure environment.
- Enable multi-factor authentication (MFA) with the broadest range of hardware and software methods.
- Build and deploy adaptive authentication policies based on the sensitivity of the data/application.
- Protect against phishing and man-in-the-middle attacks.
- Secure data-in-transit with future-proof encryption technologies to avoid "Harvest now, decrypt later".