Host Card Emulation
Securing a mobile phone such that it can be used to make credit or debit transactions at a physical point-of-sale (POS) terminal is a challenge. Payment systems based on magnetic stripe cards have evolved to use EMV chip cards and the natural next stage was to utilise dedicated security hardware inside most phones called a Secure Element to host the payment application, user payment credentials and the associated cryptographic keys.
However, this approach has proven difficult to take from pilot to mass deployment for a variety of reasons – lack of standardisation for mobile phones, complex certification requirements and, most importantly, the reluctance of many banks to cede control to a third party, the Trusted Service Manager (TSM). In the TSM model the bank pays to ‘rent space’ on the Secure Element, which is typically controlled by a mobile network operator (MNO) or handset manufacturer. To overcome these challenges an alternative approach is rapidly gaining support – Host Card Emulation (HCE). With HCE, critical payment credentials are stored in a secure shared repository (the issuer data centre or private cloud) rather than on the phone. Using host card emulation, limited use credentials are delivered to the phone in advance to enable contactless transactions to take place. Although host card emulation eliminates the need for TSMs and shifts control back to the banks, it brings with it a different set of security and risk challenges.
- Challenges
- Solutions
- Benefits
Host Card Emulation for Mobile Payments: Today’s Challenge
- The establishment of a centralised service to store many millions of payment credentials or create one-time use credentials on demand creates an obvious point of attack. Although banks have issued cards for years, those systems have largely been offline, not requiring round-the-cloud interaction with the payment token (in this case a plastic card). Host Card Emulation requires these services to be online and accessible in real-time as part of individual payment transactions. Failure to protect these service platforms places the issuer at considerable risk of fraud.
- Although the phone no longer acts as the store for payment credentials, it still plays three critical security roles. All three create opportunities for theft or substitution of credentials or transaction information.
- It provides the means for applications to request card data stored in the host card emulation (HCE) service
- It is the method by which a user is authenticated and authorises the service to provide the payments credentials
- It provides the communications channel over which payment credentials are passed to the POS terminal
- All mobile payments schemes are more complex than traditional card payments and yet smart phone user expectations are extremely high. Poor mobile network coverage makes HCE services inaccessible, complex authentication schemes lead to errors and software or hardware incompatibility can bring everything to a halt. A flexible approach will be required where credentials are cached and risk-based approvals will become the norm all at a time when standards will be maturing and the need for certifications will be imposed.
Host Card Emulation for Mobile Payments: Thales Solutions
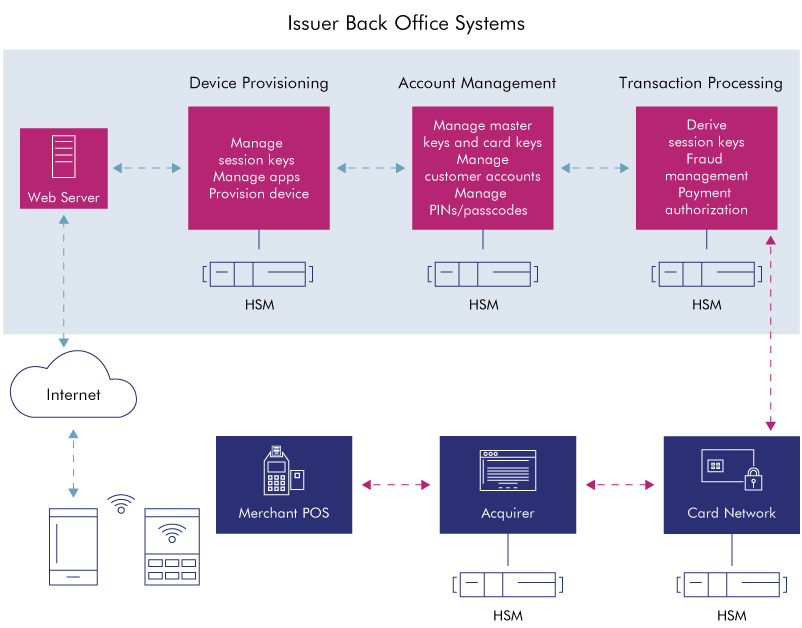
Thales payShield Hardware Security Modules (HSMs) are in use today helping to secure HCE-based solutions. Payment credentials are securely generated and stored centrally using HSMs by the issuer, who also has the flexibility to decide how many keys are stored in the phone at any given time, and therefore cover situations where offline authorisation is supported as part of the issuer risk decision. In an online authorisation situation (which is the usual deployment mode for HCE solutions), the issuer uses HSMs to validate the cryptogram which is generated by the phone app in real time as part of the contactless mobile payment transaction. In this case, the security design of the phone app is critical to ensure that the processing inside the phone limits the risk of key or sensitive data exposure to fraudulent attack. That is why the card schemes are conducting extensive validation of mobile payment app security (which includes the interface to the issuer involving HSMs) before the bank can go live with the HCE service.
Thales Hardware Security Modules help to secure HCE-based solutions
- Use the same types of Thales HSMs for HCE that are used globally today for authorising card payments and issuing EMV cards
- Take advantage of the Thales integration partner ecosystem to source proven HCE-based solutions and be automatically compatible with the latest card scheme specifications
- Choose from a range of cryptographic algorithms and key management schemes already supported by Thales HSMs to create a hardware-based secure session between the issuer system and the phone, eliminating man-in-the-middle attacks during the credential loading process
- Leverage the existing PCI HSM certifications to simplify audit compliance and ensure the best possible key generation and protection methods are deployed
