CipherTrust Tokenisation
CipherTrust Tokenisation dramatically reduces the cost and effort required to comply with security policies and regulatory mandates like PCI DSS while also making it simple to protect other sensitive data including personally identifiable information (PII). While there are no tokenisation standards in the industry, most tokenisation solutions fall into one of two architectures: vaultless or vaulted tokenisation Both secure and anonymise sensitive assets. Tokenisation software can reside in the data centre, big data environments or the cloud.

If you are seeking a tokenisation solutions, consider:
- CipherTrust Vaultless Tokenisation with dynamic data masking or
- CipherTrust Vaulted Tokenisation
- Both offerings are easy to use, cloud friendly and highly secure.
Learn how tokenisation can be a valuable tool to aid in securing your digital transformation:
- Benefits
- Features
- Specifications
Efficiently Reduce PCI DSS Compliance Scope
Tokenisation can remove card holder data from PCI DSS scope with minimal cost and effort, enabling organisations to save on costs associated with compliance with the industry standard.
Conveniently Protect Personally Identifiable Information
Modern IT architectures require both use and protection of personally identifiable information (PII). With CipherTrust Tokenisation, PII protection is gained without encryption key management required by the software developer.
Foster Innovation Without Introducing Risk
Tokenise data and maintain control and compliance when moving data to the cloud or big data environments. Cloud providers have no access to token vaults or any of the keys associated with tokenisation root of trust.
Architect for Your Requirements: Vaultless or Vaulted and Cloud-Friendly
Both solutions leverage CipherTrust Manager as a secure encryption key source. All-software, cloud-friendly, is readily available, including with FIPS 140-2 Level 3 Root of Trust.
Tokenisation Choices
Vaultless Tokenisation with dynamic data masking offers format-preserving or random tokenisation to protect sensitive data. A RESTful API in combination with centralised management and services enables tokenisation with a single line of code per field. The service is provided by dedicated, distributed-cluster-capable CipherTrust Tokenisation Servers, delivering full separation of duties. Tokenisation management with convenient configuration workflows occurs in a graphical user interface. Simplicity results from the ability, with a few as just one line of code inserted into applications, to tokenise or detokenise with dynamic data masking.
- Dynamic data masking is provided through administrators establishing policies to return an entire field tokenised or dynamically mask parts of a field based on user or group, integrated with LDAP or AD. For example, a security team could establish policies so that a user with customer service representative credentials would only receive a credit card number with the last four digits visible, while a customer service supervisor could access the full credit card number in the clear. Looking for static data masking? Tokenisation offers static data masking but, for the broad range of static data masking use cases, consider CipherTrust Batch Data Transformation.
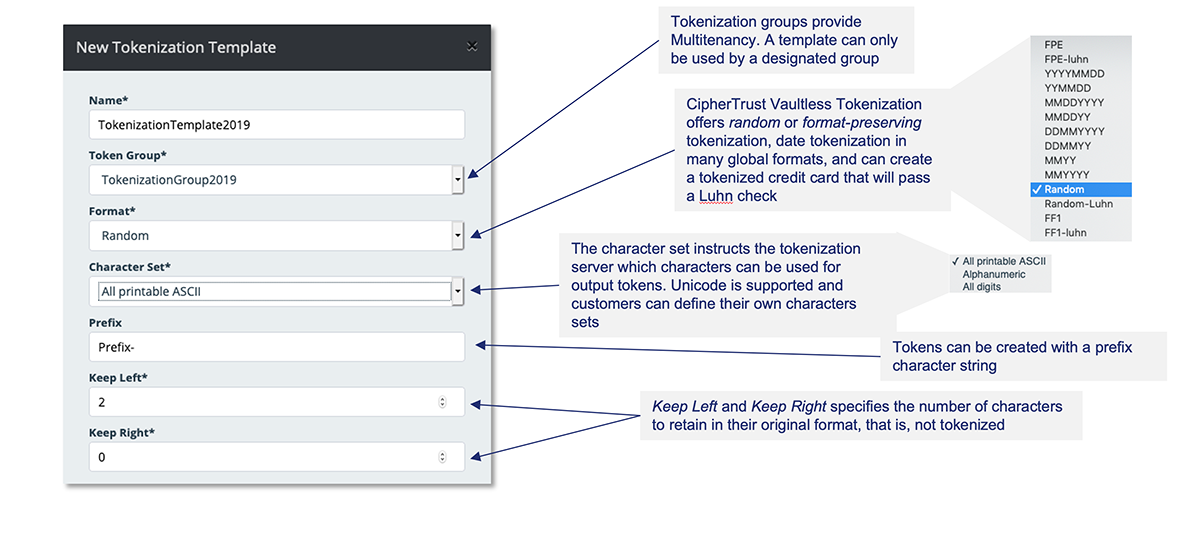
- Multi-tenancy is provided with Tokenisation groups, which ensure that data tokenised by one group cannot be detokenised by another and are centrally managed.
- Centralised Tokenisation Templates. At the core of the programming simplicity of Vormetric Tokenisation is the tokenisation template.
Vaulted tokenisation CipherTrust Vaulted Tokenisation offers non-disruptive format-preserving tokenisation with a wide range of existing formats and the ability to define custom tokenisation formats. Data tokenisation can be applied directly on application servers on which the software is installed, or API requests from application to web servers on which tokenisation software is installed can be utilised for tokenisation. A full range of predefined tokenisation formats are provided with the distribution and customers can create additional formats.
Vaultless Tokenisation Technical Specifications
Tokenisation Capabilities
- Format-preserving tokens with irreversible option. Random tokenisation for data length up to 128K. Data tokenisation. Luhn checking option for FPE and random tokens
Dynamic data masking capabilities
- Policy based, number of left and/or right characters exposed, with customisable mask character
- Authentication with Lightweight Directory Access Protocol (LDAP) or Active Directory (AD)
Tokenisation Server deployment form factors and options
- Open Virtualisation Format (.OVA) and International Organisation for Standardisation (.iso)
- Microsoft Hyper-V VHD
- Amazon Machine Image (.ami)
- Microsoft Azure Marketplace
- Google Cloud Platform
Tokenisation Server deployment requirements
- Minimum hardware: 4 CPU cores, 16 GB RAM. 32 GB RAM recommended
- Minimum disk: 85GB
Application integration
- RESTful APIs
Performance:
- More than 1 million credit card size tokenisation transactions per second, per token server (using multiple threads and batch (or vector) mode) on a 32-core server (dual-socket Xeon E5-2630v3) with 16 GB RAM
Vaulted Tokenisation Technical Specifications
Tokenisation capabilities:
- Format-preserving tokens
- Random or sequential token generation
- Masked: Last four, First six, First two, etc.
- Fixed length and width masking
- Customer defined custom formats
- Regular expressions (Java style)
Supported token vault databases
- Microsoft SQL server
- Oracle
- MySQL
- Cassandra
Application integration
- REST
- Java
- .NET

