Build trust in online payments
Financial institutions (FIs) are facing a rising tide of cyber threats such as phishing and account takeovers. Strong customer authentication (SCA) solutions provide an additional layer of security, making it more difficult for fraudsters to impersonate customers and carry out fraudulent activities. Moreover, SCA allows FIs to achieve a harmonious blend of security, user experience, and regulatory compliance.

Bolster Security
Mitigate frauds and account takeovers. Significantly boost the security of online payment transactions.

Build customer trust
Demonstrate a commitment to safeguarding customers' financial transactions while prioritising convenience.

Ensure compliance
Comply with regulatory standards such as the EU Payment Services Directive (PSD2).
What is Strong Customer Authentication?
Strong customer authentication is a mandatory security measure introduced by the EU Payment Services Directive (PSD2) to mitigate fraud and enhance the safety of online payments. SCA mandates financial institutions to employ at least two distinct authentication methods to confirm a financial transaction. These methods may involve factors like something known to the customer (e.g., password), something possessed by the customer (e.g., phone or security token), or something inherent to the customer (e.g., fingerprint).
Why is strong customer authentication important?
By using multiple forms of authentication, SCA makes it more difficult for fraudsters to impersonate the customer and complete a fraudulent transaction. This helps protect both Fls and customers from fraud's costly and disruptive effects. SCA is also important for ensuring compliance with regulatory requirements and maintaining the trust of customers in the online payment process.
What are some challenges that financial institutions face when implementing SCA?
While strong customer authentication is an important measure for fraud detection in banking and ensuring compliance, it can also present some challenges for FIs, such as:
- Compatibility with existing systems: SCA may require Fls to change their existing systems and processes to support the use of multiple authentication methods.
- Complexity for customers: Multiple authentication methods can add extra steps to the payment process, which some customers may perceive as complex or inconvenient.
- Integration with third-party services: If a merchant uses third-party payment or billing services, they may need to ensure that these services are compatible with SCA and can support the required authentication methods.
To address these challenges, Fls may need to invest in new technology or work closely with their digital banking and payment service providers to ensure a smooth transition to SCA.
How can I streamline access while maintaining compliance?
To streamline user access, organisations should offer various authentication methods such as context-based authentication, SMS, phone tokens, or hardware tokens, catering to user roles and security profiles. Integrating passkeys into authentication options could offer a seamless yet secure approach, enhancing user experience and ensuring compliance with corporate security policies.
IdCloud – now part of the OneWelcome Identity Platform – is the perfect answer to the security requirements of regulations such as PSD2 and FFIEC. It enables FIs to meet the PSD2 requirements for SCA and dynamic linking and to offer real-time monitoring of the authentication and transaction process risk, as required by the regulatory technical standards (RTSs) of PSD2.
Complex security policies can be defined, based on the level of risk, the type of transaction and the user profile, as the FFIEC recommends. It also helps you to meet the requirement for stronger risk management to fight the increasing number of cyber-attacks and growing levels of fraud.
Data privacy regulations such as the GDPR in Europe and CCPA in the US are becoming more stringent. These can be a real challenge to comply with if data has to be processed by several different vendors for risk assessment. The OneWelcome platform has been designed to be GDPR and CCPA-compliant.
Why is SCA implementation on the rise in digital banking?
Digital banking is on the rise with the implementation of strong customer authentication because:
- Increased security: SCA provides a high level of security for online payments, reducing the risk of fraud and unauthorised transactions, which makes customers feel more secure about using digital banking services.
- Convenience: With the widespread adoption of mobile devices and the internet, digital banking offers customers the convenience of being able to manage their finances from anywhere, at any time.
- Better user experience: Digital banking platforms can provide a more intuitive and user-friendly experience, with real-time notifications and budget tracking features.
Overall, implementing SCA in digital banking helps build trust in the security of online payments, making digital banking an increasingly popular choice for customers.
How has digital banking authentication evolved?
Most financial institutions (FIs) implementing Strong Customer Authentication (SCA) use OATH technology. The next step in the evolution of digital banking authentication is FIDO and passkeys.
Embedded platform authenticators will greatly improve the user experience, and a passwordless future is within reach. We are certain that FIDO will replace OATH as the de facto standard.
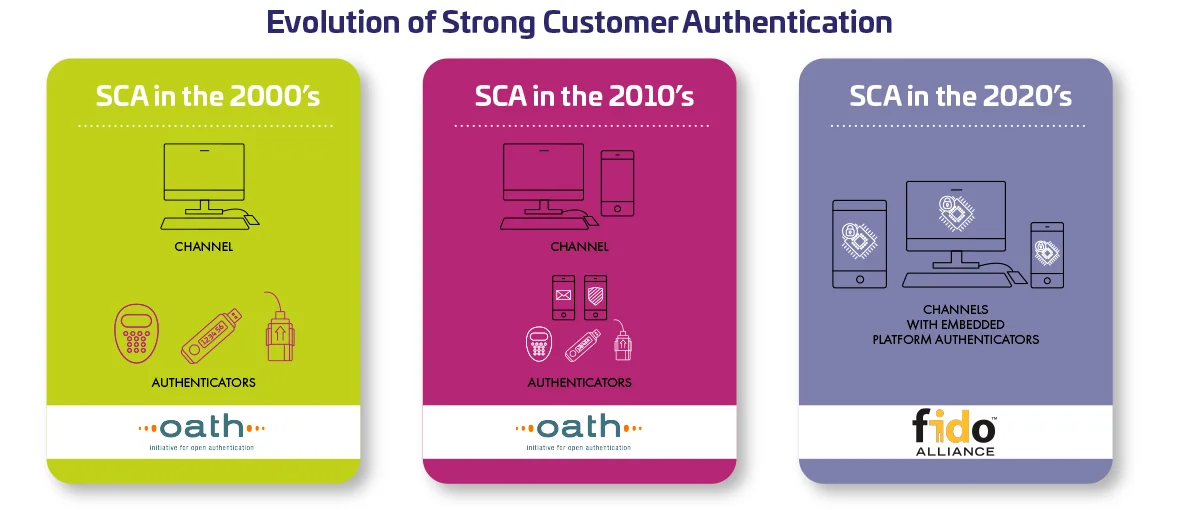
This means that FIs have to make another technological migration. IdCloud – now part of the OneWelcome Identity Platform – supports both technologies and is FIDO2 certified, plus we have the experience to help with these migrations.
We understand the importance of ensuring continuity of service and preventing any disruption or friction for end users.
We advise further enhancing security by adding Risk-based Authentication (RBA) during this migration.

#2024TRUSTINDEX
81% of consumers
expect some form of strong authentication despite strong authentication historically associated with frustrating customer experiences. Passkeys can serve as a component in attaining a balance.

Navigate PSD2 regulations and compliance with Thales.
The PSD2 regulation drastically impacts the financial ecosystem and infrastructure for banks, fintechs, and businesses using payment data to benefit consumers. Here is everything you need to know about PSD2.

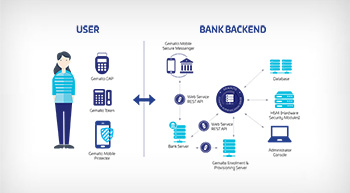
How SCA works and how we can help
SCA works by verifying a user's identity through multiple factors such as passwords, biometrics, or possession of a device.
Users must provide authentication through at least two of the following factors to complete a transaction:
Knowledge factors
This involves something only the user knows, such as a password, PIN, or answers to security questions.
Possession factors
This involves something only the user possesses, such as a mobile device, smart card, or token.
Inherence factors
This involves something inherent to the user, such as biometric data like fingerprint, facial recognition, or iris scans.
Thales provides tailored security solutions for FIs, including cloud-based managed services, to facilitate seamless and cost-effective implementation of SCA and risk management protocols.
Our cloud-based managed services enable FIs to combine identity-proofing and strong customer authentication to secure onboarding and digital banking access, within a single platform.
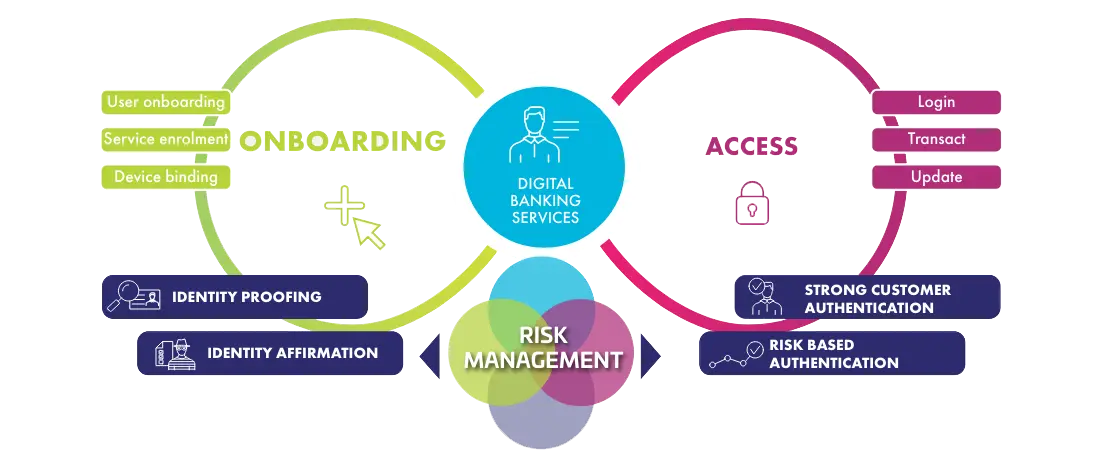

For decades, financial institutions worldwide have entrusted Thales to safeguard access to their digital services. With our wide range of solutions specifically designed to protect both financial institutions and end-users, we effectively address the security, functional, and regulatory needs of the industry."
Effectively validate identities with tailored authentication
Tailor your authentication journey to your organisation's needs, users, and risk levels for a robust and cost-effective system.
Integrate different authentication options, including:
One-Time Passwords (OTP)
Uses shared secrets to generate one-time passcodes for authentication.
Certificate-based Authentication (CBA)
Utilises unique encryption keys for authentication and digital signatures, available through Thales USB tokens and smart cards.
Context-based Authentication
Enhances identity verification using contextual information, recommended alongside other strong authentication methods.


Thales Named an Overall Leader
Find the product or service that best meets your needs, and learn why KuppingerCole named Thales a Market Leader, Overall Leader, and Innovation Leader in Access Management