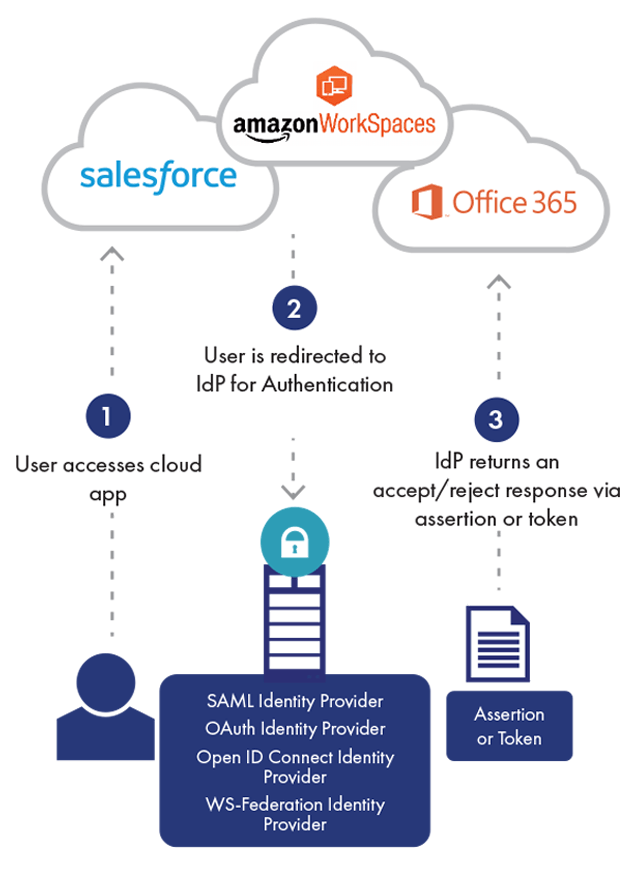
La gestione degli accessi è una funzionalità che permette di determinare se un utente ha il permesso di accedere a una certa risorsa, e consente l'applicazione dei criteri di accesso istituiti per tale risorsa.
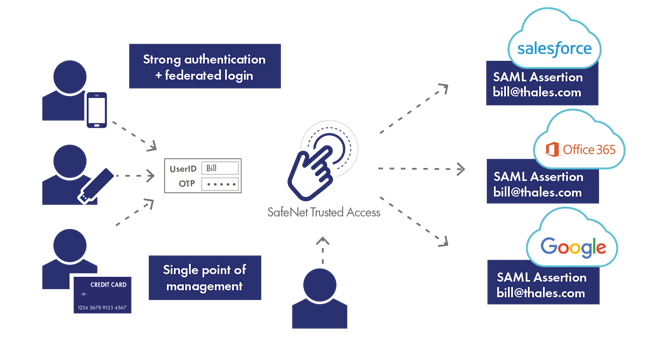
La gestione degli accessi è attuata sulla base dei criteri di accesso definiti dagli amministratori IT che includono informazioni come i gruppi di utenti (ad es. reparto vendite, ricerca e sviluppo, risorse umane) a cui è consentito l’accesso a determinate applicazioni cloud (ad es. Salesforce, Office 365, Jira, Taleo), come anche il set di attributi utente necessari per accedere (ad es. rete fidata, password, OTP).
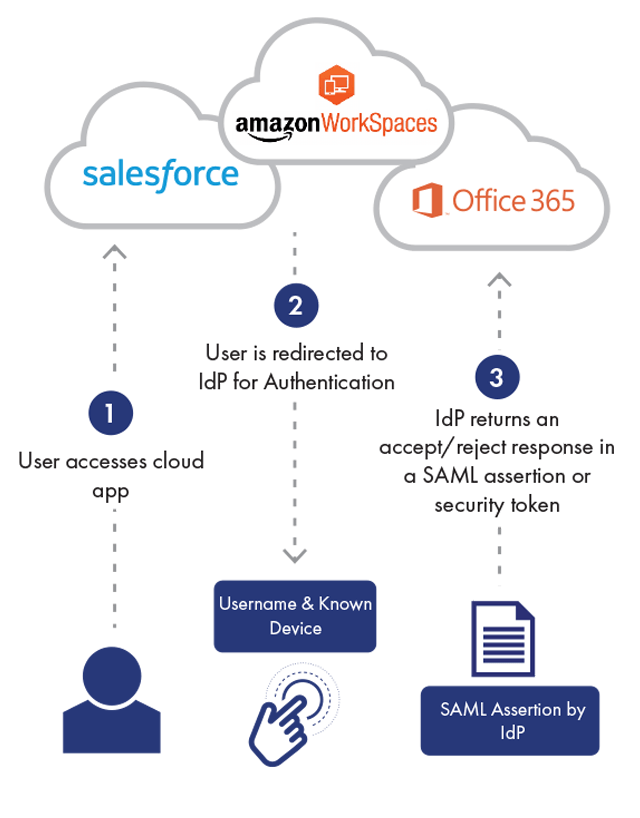
Il criterio di accesso può richiedere la valutazione di più o meno attributi utente a seconda della sensibilità di un’applicazione cloud. Questi attributi vengono valutati utilizzando l’autenticazione contestuale o basata sul rischio, fondamentale per applicare i diversi criteri di accesso definiti per ciascuna applicazione cloud (per ulteriori dettagli, leggi il nostro articolo sull’autenticazione contestuale).
Fondamentale per la gestione degli accessi al cloud è anche il Single Sign-On che, per accedere a tutte le applicazioni cloud, consente l’utilizzo di un unico set username/password o “identità” (per ulteriori dettagli, leggi il nostro articolo sul Single Sign-On).